The Mal virus falls under the Xorist ransomware family. A harmful program of this type encrypts all user’s data on the computer (images, text files, excel sheets, audio files, videos, etc) and adds its extra extension to every file, leaving the HOW TO DECRYPT FILES.txt files in each directory containing encrypted files.
What is Mal virus?
☝️ A scientifically correct denomination for the Mal would be “a Xorist family ransomware-type malicious agent”.
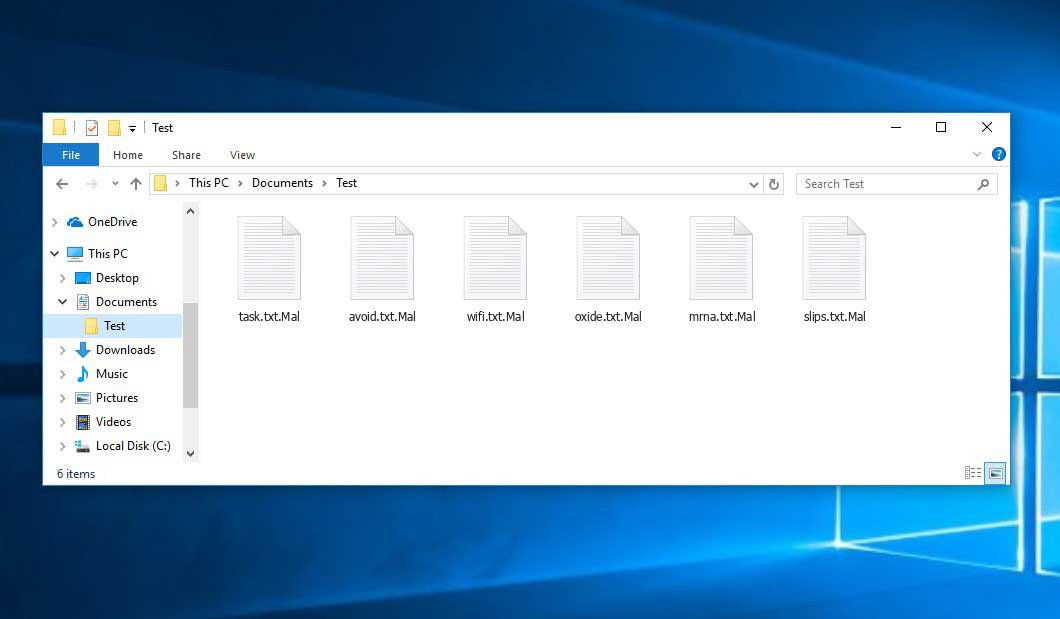
Mal will add its extra .Mal extension to the title of each encrypted file. For instance, an image entitled “photo.jpg” will be turned into “photo.jpg.Mal”. Just like the Excel sheet named “table.xlsx” will be altered to “table.xlsx.Mal”, and so forth.
In every directory containing the encrypted files, a HOW TO DECRYPT FILES.txt file will be created. It is a ransom money note. Therein you can find information about the ways of paying the ransom and some other information. The ransom note usually contains a description of how to buy the decryption tool from the tamperers. That is how they do it.
Mal abstract:
| Name | Mal Virus |
| Ransomware family1 | Xorist ransomware |
| Extension | .Mal |
| Ransomware note | HOW TO DECRYPT FILES.txt |
| Detection | Worm.WormBuilder, Ursu.885954, MSIL/FiryWorm-A |
| Symptoms | Your files (photos, videos, documents) get a .Mal extension and you can’t open them. |
| Fix Tool | See If Your System Has Been Affected by Mal virus |
In the screenshot below, you can see what a directory with files encrypted by the Mal looks like. Each filename has the “.Mal” extension appended to it.
How did my machine catch Mal ransomware?
There are plenty of possible ways of ransomware infiltration.
There are currently three most popular methods for evil-doers to have the Mal virus working in your digital environment. These are email spam, Trojan infiltration and peer file transfer.
If you open your mailbox and see emails that look just like notifications from utility services companies, delivery agencies like FedEx, Internet providers, and whatnot, but whose addresser is strange to you, beware of opening those emails. They are very likely to have a malicious item attached to them. Thus it is even more dangerous to open any attachments that come with letters like these.
As for the peer networks like torrents or eMule, the danger is that they are even more trust-based than the rest of the Internet. You can never know what you download until you get it. Our suggestion is that you use trustworthy resources. Also, it is reasonable to scan the directory containing the downloaded items with the anti-malware utility as soon as the downloading is finished.
How do I get rid of the Mal virus?
It is crucial to note that besides encrypting your data, the Mal virus will probably deploy the Azorult Spyware on your PC to seize your credentials to different accounts (including cryptocurrency wallets). The mentioned spyware3 can extract your credentials from your browser’s auto-filling data.
Often tamperers would decode few of your files so you know that they really have the decryption tool. Since Mal virus is a relatively new ransomware, anti-malware engineers have not yet found a way to reverse its work. However, the decryption tools are constantly updated, so the effective countermeasure may soon arrive.
Of course, if the tamperers succeed in encrypting someone’s critical files, the hopeless person will probably comply with their demands. However, paying to criminals does not necessarily mean that you’re getting your data back. It is still risky. After getting the ransom, the racketeers may deliver a wrong decryption code to the injured party. There were reports of hackers just disappearing after getting the money without even bothering to reply.
The optimal countermeasure to ransomware is to have aan OS restore point or the copies of your essential files in the cloud drive or at least on an external disk. Obviously, that might be not enough. The most important thing could be that file you were working upon when it all happened. Nevertheless, it is something. It is also wise to scan your PC for viruses with the anti-malware utility after the system is rolled back.
There are other ransomware products, besides Mal, that work similarly. Examples of those are Jhdd, Tuid, Dewd, and some others. The two major differences between them and the Mal are the ransom amount and the method of encryption. The rest is almost identical: files become encrypted, their extensions changed, ransom notes emerge in every folder containing encoded files.
Some lucky users were able to decrypt the blocked files with the help of the free tools provided by anti-malware specialists. Sometimes the criminals mistakenly send the decryption key to the victims in the ransom readme. Such an epic fail allows the user to restore the files. But naturally, one should never expect such a chance. Make no mistake, ransomware is a tamperers’ technology to pull the money out of their victims.
How do I avoid ransomware infection?
Mal ransomware doesn’t have a superpower, so as any similar malware.
You can protect your system from ransomware attack in three easy steps:
- Ignore any emails from unknown senders with unknown addresses, or with content that has likely no connection to something you are expecting (how can you win in a money prize draw without even taking part in it?). If the email subject is likely something you are expecting, check all elements of the suspicious letter carefully. A hoax email will surely have mistakes.
- Avoid using cracked or unknown programs. Trojans are often shared as a part of cracked products, most likely as a “patch” to prevent the license check. Understandably, potentially dangerous programs are difficult to tell from trustworthy software, because trojans sometimes have the functionality you need. You can try searching for information on this program on the anti-malware forums, but the optimal way is not to use such programs at all.
Reasons why I would recommend GridinSoft4
Download Removal Tool.
Run the setup file.


Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.

Click on “Clean Now”.

FAQ
🤔 How can I open “.Mal” files?Are the “.Mal” files accessible?
There’s no way to do it, unless the files “.Mal” files are decrypted.
🤔 The encrypted files are very important to me. How can I decrypt them quickly?
It’s good if you have fаr-sightedly saved copies of these important files elsewhere. Otherwise, you might try to employ System Restore. The only question is whether you have saved any Restore Points that would be helpful now. All other solutions require time.
🤔 What actions should I take if the Mal malware has blocked my PC and I can’t get the activation key.
🤔 What can I do right now?
Many of the encoded files might still be at your disposal
- If you sent or received your critical files through email, you could still download them from your online mailbox.
- You may have shared photographs or videos with your friends or relatives. Simply ask them to send those pictures back to you.
- If you have initially downloaded any of your files from the Internet, you can try doing it again.
- Your messengers, social networks pages, and cloud drives might have all those files too.
- Maybe you still have the needed files on your old computer, a notebook, phone, flash memory, etc.
USEFUL TIP: You can use data recovery programs6 to retrieve your lost information since ransomware blocks the copies of your files, deleting the authentic ones. In the tutorial below, you can learn how to recover your files with PhotoRec, but remember: you won’t be able to do it before you remove the virus with an antivirus program.
Also, you can contact the following governmental fraud and scam sites to report this attack:
- In the United States: On Guard Online;
- In Canada: Canadian Anti-Fraud Centre;
- In the United Kingdom: Action Fraud;
- In Australia: SCAMwatch;
- In New Zealand: Consumer Affairs Scams;
- In France: Agence nationale de la sécurité des systèmes d’information;
- In Germany: Bundesamt für Sicherheit in der Informationstechnik;
- In Ireland: An Garda Síochána;
To report the attack, you can contact local executive boards. For instance, if you live in USA, you can have a talk with FBI Local field office, IC3 or Secret Service.


Leave a Comment