A group of researchers, led by a hacker known as Sick Codes, spoke at Def Con about the discovery of multiple vulnerabilities in John Deere and Case New Holland systems, two largest agricultural equipment companies.
Experts warned that in the hands of attackers, these vulnerabilities could threaten both consumers and the global food supply chains.Both companies produce high-tech agricultural machinery, and the researchers believe that attacking users of such agricultural enterprises could seriously affect crop yields and compromise trade secrets.
Interestingly, John Deere recently launched its own bug bounty program on HackerOne, and Sick Codes was invited to join the initiative as he contacted the company this spring about the bugs found. However, in the end, the researcher refused to participate in the program, as he realized that in this case he would have to sign a non-disclosure agreement.
During a talk at Def Con, Sick Codes considered a number of vulnerabilities, eventually reaching problems that allow “any user to download arbitrary files, log in as any user <...> download whatever we want, download whatever we want, destroy any data, log in to any accounts “.
The hackers emphasized that the vulnerabilities could give attackers remote access to download or upload files on agricultural equipment, including tractors.
In response to this presentation, John Deere representatives stated the following:
In addition, the company said it has increased security spending “by about 750%” over the past seven years.
For example, Case New Holland provides customers with remote access to some equipment, located hundreds of miles away, using only user data.
Research by the Sick Codes team has shown that the Case JavaMelody server can be compromised, leading to the disclosure of sensitive data, including location data, IP addresses, session IDs, and full names of people. Using this information, attackers will be able to impersonate users and infiltrate the system.
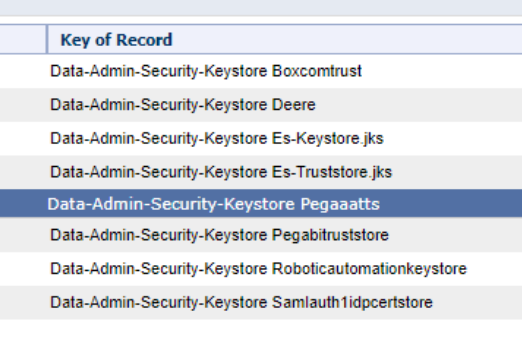
The hackers also gained access to administrative credentials from John Deere Pega, which they describe as a master key for accessing “critical” information. In addition, they discovered an issue in the user numbering system that allowed an unauthenticated remote attacker to gain access to a user’s personal information, including IDs, full names, and addresses.
Bugs were also found in the system that is used to reserve demo units of equipment for exhibitions and conferences. Researchers could book rooms, change or cancel appointments. They were also able to “book” any demo car ever provided.
The Sick Codes team also managed to obtain the original decryption password and signing certificate for the company’s Okta, which is an SSO platform used to provide employees with access to all of the company’s software. According to Sick Codes, an attacker could use this to log in as any user, download or delete any data, delete accounts, and more.
Since the presentation, no one from the research team has received a response from John Deere or Case New Holland, Sick Codes said. The screenshots provided by the group confirm that they briefed John Deere Chief Information Officer James Johnson about the issues, and also informed the company that they intend to publish their research (by providing presentation files in advance). And although there were no responses from the companies, according to the Sick Codes website, all vulnerabilities that were disclosed at the conference have been fixed.
Let me remind you that we also talked about INFRA: HALT vulnerabilities affect industrial equipment from 200 manufacturers.

