The Inc virus belongs under the ransomware type of infection. Malware of such sort encrypts all user’s data on the computer (photos, documents, excel sheets, music, videos, etc) and appends its specific extension to every file, leaving the INC-README.txt files in each directory with the encrypted files.
What is known about the Inc virus?
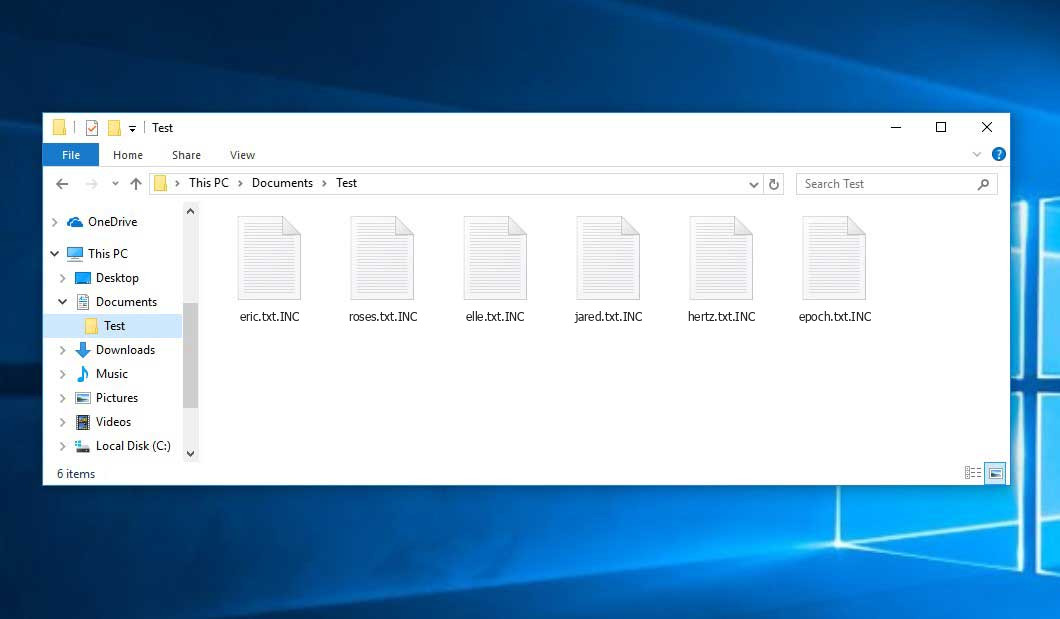
Inc will add its specific .INC extension to the name of each encoded file. For instance, a file named “photo.jpg” will be changed to “photo.jpg.INC”. Likewise, the Excel sheet with the name “table.xlsx” will become “table.xlsx.INC”, and so on.
In every directory with the encoded files, a INC-README.txt text document will be found. It is a ransom money memo. Therein you can find information about the ways of contacting the racketeers and some other information. The ransom note usually contains a description of how to purchase the decryption tool from the racketeers. You can obtain this decrypting software after contacting Onion site through Tor browser. That is it.
Inc Overview:
| Name | Inc Virus |
| Extension | .INC |
| Ransomware note | INC-README.txt |
| Contact | Onion site |
| Detection | Win32/Filecoder.Spacecolon.A, Virus:Win32/Emdup.A, Trojan:Win32/Agent.WTK!MTB |
| Symptoms | Your files (photos, videos, documents) get a .INC extension and you can’t open them. |
| Fix Tool | See If Your System Has Been Affected by Inc virus |
The INC-README.txt file accompanying the Inc ransomware states the following:
Inc. Ransomware We have hacked you and downloaded all confidential data of your company and its clients. It can be spread out to people and media. Your reputation will be ruined. Do not hesitate and save your business. Please, contact us via: - Your personal ID: - We\'re the ones who can quickly recover your systems with no losses. Do not try to devalue our tool - nothing will come of it. Starting from now, you have 72 hours to contact us if you don\'t want your sensitive data being published in our blog: - You should be informed, in our business reputation - is a basic condition of the success. Inc provides a deal. After successfull negotiations you will be provided: 1. Decryption assistance; 2. Initial access; 3. How to secure your network; 4. Evidence of deletion of internal documents; 5. Guarantees not to attack you in the future.
In the picture below, you can see what a directory with files encrypted by the Inc looks like. Each filename has the “.INC” extension appended to it.
How did Inc ransomware end up on my PC?
There are many possible ways of ransomware infiltration.
There are currently three most popular methods for evil-doers to have the Inc virus settled in your digital environment. These are email spam, Trojan injection and peer-to-peer file transfer.
- If you access your mailbox and see emails that look like familiar notifications from utility services companies, postal agencies like FedEx, Internet providers, and whatnot, but whose “from” field is unknown to you, beware of opening those emails. They are most likely to have a viral file enclosed in them. So it is even riskier to open any attachments that come with letters like these.
- Another option for ransom hunters is a Trojan horse model. A Trojan is an object that gets into your PC disguised as something legal. For example, you download an installer for some program you need or an update for some software. However, what is unpacked reveals itself a harmful program that encrypts your data. As the installation wizard can have any title and any icon, you’d better be sure that you can trust the source of the stuff you’re downloading. The best thing is to use the software developers’ official websites.
- As for the peer-to-peer networks like BitTorrent or eMule, the threat is that they are even more trust-based than the rest of the Internet. You can never know what you download until you get it. So you’d better be using trustworthy resources. Also, it is reasonable to scan the directory containing the downloaded objects with the antivirus as soon as the downloading is complete.
How do I get rid of ransomware?
It is crucial to inform you that besides encrypting your files, the Inc virus will most likely install Vidar Stealer on your PC to get access to credentials to different accounts (including cryptocurrency wallets). The mentioned program can extract your credentials from your browser’s auto-filling data.
How do I avert ransomware infiltration?
Inc ransomware has no endless power, neither does any similar malware.
You can protect your system from its injection in several easy steps:
- Never open any emails from unknown mailboxes with strange addresses, or with content that has nothing to do with something you are expecting (how can you win in a money prize draw without even taking part in it?). If the email subject is more or less something you are expecting, scrutinize all elements of the suspicious email carefully. A hoax email will always have a mistake.
- Never use cracked or untrusted software. Trojan viruses are often shared as an element of cracked products, most likely under the guise of “patch” to prevent the license check. But untrusted programs are difficult to tell from trustworthy software, because trojans may also have the functionality you need. Try searching for information about this program on the anti-malware forums, but the optimal way is not to use such software.
FAQ
🤔 How can I open “.INC” files?Are the “.INC” files accessible?
Unfortunately, no. You need to decipher the “.INC” files first. Then you will be able to open them.
🤔 I really need to decrypt those “.INC” files ASAP. How can I do that?
Hopefully, you have made a copy of those important files. If not, there is still a function of System Restore but it needs a Restore Point to be previously saved. There are other ways to beat ransomware, but they take time.
🤔 What to do if the Inc malware has blocked my computer and I can’t get the activation code.
🤔 And what should I do now?
Some of the blocked files can be found elsewhere.
- If you exchanged your important files by email, you could still download them from your online mailbox.
- You might have shared images or videos with your friends or relatives. Just ask them to give those pictures back to you.
- If you have initially got any of your files from the Web, you can try to do it again.
- Your messengers, social media pages, and cloud disks might have all those files as well.
- Maybe you still have the needed files on your old PC, a notebook, cellphone, memory stick, etc.
USEFUL TIP: You can employ data recovery utilities1 to retrieve your lost information since ransomware blocks the copies of your files, deleting the authentic ones. In the video below, you can learn how to use PhotoRec for such a restoration, but be advised: you can do it only after you remove the virus with an anti-malware program.
I need your help to share this article.
It is your turn to help other people. I have written this article to help people like you. You can use the buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan SmithReferences
- Here are Top 10 Data Recovery Software Of 2023.


Leave a Comment