The Black ice virus belongs with the ransomware type of infection. Ransomware of this type encrypts all the data on your computer (images, text files, excel sheets, audio files, videos, etc) and appends its own extension to every file, creating the ICE_Recovey.txt text files in every directory with the encrypted files.
What is Black ice virus?
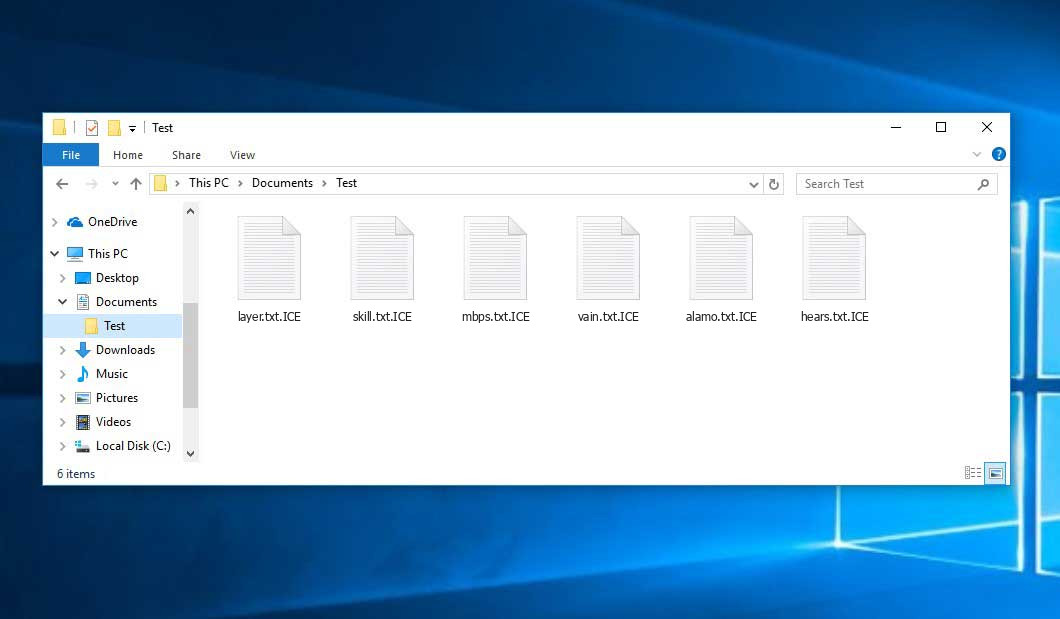
Black ice appends its specific .ICE extension to the name of every encrypted file. For instance, an image entitled “photo.jpg” will be changed to “photo.jpg.ICE”. In the same manner, the Excel file with the name “table.xlsx” will be altered to “table.xlsx.ICE”, and so forth.
In each directory containing the encrypted files, a ICE_Recovey.txt text file will be found. It is a ransom money note. Therein you can find information about the ways of contacting the racketeers and some other remarks. The ransom note most probably contains instructions on how to buy the decryption tool from the ransomware developers. You can obtain this decrypting software after contacting [email protected] through email. That is it.
Black ice Summary:
| Name | Black ice Virus |
| Extension | .ICE |
| Ransomware note | ICE_Recovey.txt |
| Contact | [email protected] |
| Detection | Win32/Filecoder.Spacecolon.A, Virus:Win32/Emdup.A, Trojan:Win32/Agent.WTK!MTB |
| Symptoms | Your files (photos, videos, documents) get a .ICE extension and you can’t open them. |
| Fix Tool | See If Your System Has Been Affected by Black ice virus |
The ICE_Recovey.txt file coming in package with the Black ice ransomware states the following:
Personal ID : - +++ BLACK ICE +++ ALL YOUR IMPORTANT FILES ARE STOLEN AND ENCRYPTED! and now have the \"ICE\" extension. There is only one way to get your files back: 1. Contact with us 2. In subject line please write your Personal ID 3. To prove that we can decrypt your files, send us 1 unimportant encrypted files. (up to 1 MB) and we will decrypt them for free. 4. We accept Bitcoin Contact us: [email protected] [email protected] +Do not delete or modify encrypted files. +Any attempts to restore your files with the thrid-party software will be fatal for your files! To recovery your data and not to allow data leakage, it is possible only through purchase of a private key from us. +Don\'t go to recovery companies, they are essentially just middlemen who will make money off you and cheat you. We are well aware of cases where recovery companies tell you that the ransom price is 5 BTC but in fact they secretly negotiate with us for 1 BTC, so they earn 4 BTC from you. If you approached us directly without intermediaries you would pay 5 times less, that is 1 BTC.
In the image below, you can see what a folder with files encrypted by the Black ice looks like. Each filename has the “.ICE” extension added to it.
How did my computer get infected with Black ice ransomware?
There are many possible ways of ransomware injection.
There are currently three most exploited ways for malefactors to have ransomware planted in your system. These are email spam, Trojan infiltration and peer-to-peer networks.
- If you access your inbox and see emails that look like familiar notifications from utility services providers, postal agencies like FedEx, Internet providers, and whatnot, but whose addresser is unknown to you, beware of opening those letters. They are very likely to have a malicious file enclosed in them. Therefore, it is even riskier to download any attachments that come with emails like these.
- Another option for ransom hunters is a Trojan file model. A Trojan is an object that gets into your PC pretending to be something different. For instance, you download an installer of some program you want or an update for some software. However, what is unpacked turns out to be a harmful program that encodes your data. As the update package can have any title and any icon, you have to make sure that you can trust the resource of the files you’re downloading. The best way is to use the software companies’ official websites.
- As for the peer-to-peer networks like BitTorrent or eMule, the danger is that they are even more trust-based than the rest of the Web. You can never know what you download until you get it. Our suggestion is that you use trustworthy websites. Also, it is reasonable to scan the directory containing the downloaded objects with the anti-malware utility as soon as the downloading is finished.
How do I get rid of ransomware?
It is important to note that besides encrypting your files, the Black ice virus will most likely install Vidar Stealer on your PC to seize your credentials to different accounts (including cryptocurrency wallets). That spyware can derive your credentials from your browser’s auto-filling cardfile.
How сan I avert ransomware infection?
Black ice ransomware doesn’t have a endless power, neither does any similar malware.
You can armour your PC from its injection in several easy steps:
- Never open any letters from unknown mailboxes with strange addresses, or with content that has likely no connection to something you are expecting (can you win in a money prize draw without participating in it?). If the email subject is more or less something you are waiting for, scrutinize all elements of the questionable email with caution. A fake email will surely have mistakes.
- Do not use cracked or untrusted programs. Trojan viruses are often distributed as an element of cracked software, most likely as a “patch” which prevents the license check. But dubious programs are difficult to distinguish from reliable software, as trojans may also have the functionality you seek. You can try searching for information about this program on the anti-malware forums, but the best way is not to use such software.
Frequently Asked Questions
🤔 How can I open “.ICE” files?Can I somehow access “.ICE” files?
Negative. That is why ransomware is so frustrating. Until you decode the “.ICE” files you will not be able to access them.
🤔 What should I do to make my files accessible as fast as possible?
If the “.ICE” files contain some really important information, then you probably have them backed up. In case you haven’t, there is still a chance that you do have a Restore Point from some time ago to roll back the whole system to the moment when it had no virus yet, but already had your files. There are other ways to beat ransomware, but they take time.
🤔 What actions should I take if the Black ice malware has blocked my computer and I can’t get the activation code.
🤔 What can I do right now?
Some of the encrypted files can be located elsewhere.
- If you exchanged your important files via email, you could still download them from your online mailbox.
- You may have shared images or videos with your friends or family members. Simply ask them to post those images back to you.
- If you have initially got any of your files from the Web, you can try doing it again.
- Your messengers, social media pages, and cloud disks might have all those files as well.
- It might be that you still have the needed files on your old computer, a portable device, mobile, flash memory, etc.
USEFUL TIP: You can use file recovery utilities1 to retrieve your lost information since ransomware encrypts the copies of your files, removing the original ones. In the tutorial below, you can learn how to use PhotoRec for such a restoration, but be advised: you can do it only after you eradicate the ransomware itself with an anti-malware program.
I need your help to share this article.
It is your turn to help other people. I have written this article to help users like you. You can use the buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan SmithReferences
- Here’s the list of Top 10 Data Recovery Software Of 2023.


Leave a Comment