The Hudson virus belongs under the ransomware type of malicious agent. Ransomware of such sort encrypts all user’s data on the PC (photos, text files, excel tables, music, videos, etc) and adds its own extension to every file, leaving the README.TXT files in every folder which contains the encrypted files.
What is known about the Hudson virus?
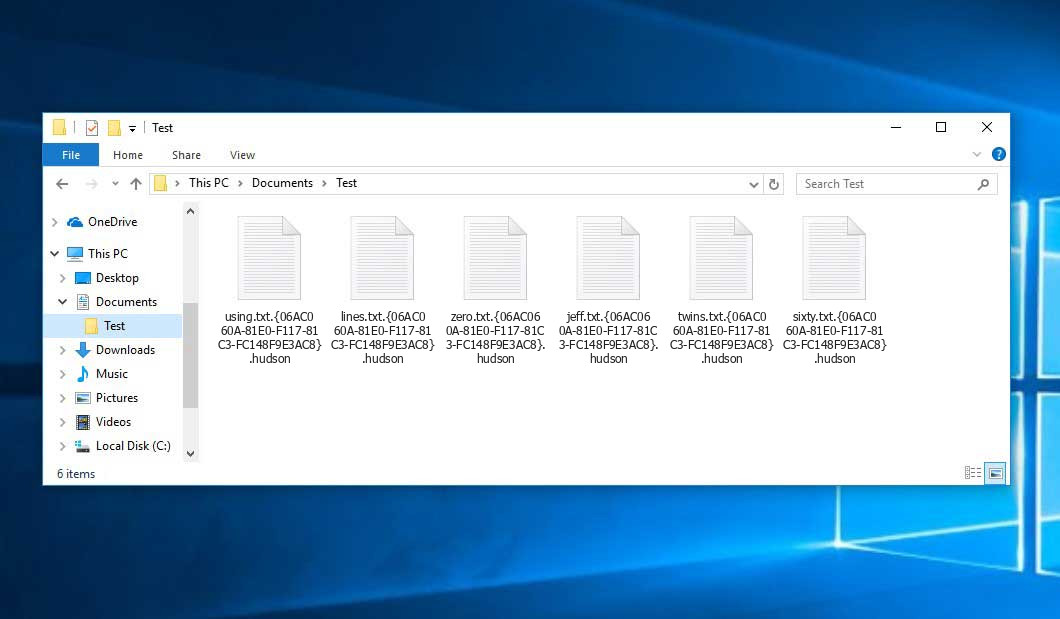
The renaming will be done by the following pattern: .hudson. After the encryption, a file named, for example, “report.docx” will be changed to “report.docx.06AC060A-81E0-F117-81C3-FC148F9E3AC8.hudson”.
In each directory containing the encoded files, a README.TXT file will be found. It is a ransom money memo. It contains information on the ways of paying the ransom and some other remarks. The ransom note most probably contains instructions on how to purchase the decryption tool from the tamperers. You can get this tool after contacting [email protected] through email. That is pretty much the scheme of the malefaction.
Hudson Summary:
| Name | Hudson Virus |
| Extension | .hudson |
| Ransomware note | README.TXT |
| Contact | [email protected] |
| Detection | Trojan:Win32/Tnega!MSR Removal, Win32:Adware-DNA [Adw] Virus Removal, Win32:Secat [Trj] Virus Removal |
| Symptoms | Your files (photos, videos, documents) get a .hudson extension and you can’t open them. |
| Fix Tool | See If Your System Has Been Affected by Hudson virus |
The README.TXT file accompanying the Hudson malware states the following:
YOUR FILES ARE ENCRYPTED Your files, documents, photos, databases and other important files are encrypted. You are not able to decrypt it by yourself! The only method of recovering files is to purchase an unique private key. Only we can give you this key and only we can recover your files. To be sure we have the decryptor and it works you can send an email: [email protected] and decrypt one file for free. But this file should be of not valuable! Do you really want to restore your files? Write to email: [email protected] Attention! * Do not rename encrypted files. * Do not try to decrypt your data using third party software, it may cause permanent data loss. * Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam. * Do not contact the intermediary companies. Negotiate on your own. No one but us will be able to return the files to you. As evidence, we will offer to test your files.
In the screenshot below, you can see what a folder with files encrypted by the Hudson looks like. Each filename has the “.hudson” extension appended to it.
How did my machine catch Hudson ransomware?
There are plenty of possible ways of ransomware injection.
There are currently three most exploited ways for criminals to have the Hudson virus settled in your system. These are email spam, Trojan injection and peer file transfer.
- Another option for ransom hunters is a Trojan virus scheme. A Trojan is a program that gets into your PC disguised as something different. For instance, you download an installer for some program you need or an update for some software. But what is unboxed reveals itself a harmful program that encrypts your data. As the installation wizard can have any name and any icon, you’d better be sure that you can trust the source of the stuff you’re downloading. The best way is to use the software companies’ official websites.
- As for the peer networks like torrent trackers or eMule, the threat is that they are even more trust-based than the rest of the Web. You can never know what you download until you get it. So you’d better be using trustworthy resources. Also, it is a good idea to scan the directory containing the downloaded files with the anti-malware utility as soon as the downloading is done.
How do I get rid of ransomware?
It is crucial to note that besides encrypting your files, the Hudson virus will most likely deploy Vidar Stealer on your machine to get access to credentials to various accounts (including cryptocurrency wallets). That program can extract your credentials from your browser’s auto-filling data.
How to avoid ransomware attack?
Hudson ransomware has no superpower, neither does any similar malware.
You can armour yourself from its attack within three easy steps:
- Ignore any emails from unknown mailboxes with strange addresses, or with content that has likely no connection to something you are expecting (how can you win in a money prize draw without participating in it?). In case the email subject is more or less something you are waiting for, scrutinize all elements of the dubious letter carefully. A hoax letter will surely have mistakes.
- Do not use cracked or untrusted software. Trojans are often spreaded as an element of cracked software, most likely as a “patch” to prevent the license check. Understandably, untrusted programs are very hard to tell from reliable software, because trojans sometimes have the functionality you need. Try to find information on this program on the anti-malware message boards, but the optimal solution is not to use such programs at all.
Frequently Asked Questions
🤔 Are the “.hudson” files accessible?
There’s no way to do it, unless the files “.hudson” files are decrypted.
🤔 I really need to decrypt those “.hudson” files ASAP. How can I do that?
Hopefully, you have made a copy of those important files. Otherwise, you might try to employ System Restore. The only question is whether you have saved any Restore Points that would be helpful now. There are other ways to beat ransomware, but they take time.
🤔 What actions should I take if the Hudson malware has blocked my PC and I can’t get the activation code.
🤔 And what should I do now?
Some of the blocked files can be located elsewhere.
- If you exchanged your important files through email, you could still download them from your online mail server.
- You might have shared images or videos with your friends or family members. Just ask them to send those images back to you.
- If you have initially downloaded any of your files from the Internet, you can try downloading them again.
- Your messengers, social media pages, and cloud drives might have all those files as well.
- It might be that you still have the needed files on your old computer, a portable device, mobile, external storage, etc.
HINT: You can employ data recovery programs1 to get your lost data back since ransomware blocks the copies of your files, deleting the authentic ones. In the video below, you can learn how to recover your files with PhotoRec, but be advised: you won’t be able to do it before you eradicate the virus with an antivirus program.
I need your help to share this article.
It is your turn to help other people. I have written this article to help people like you. You can use the buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan SmithReferences
- Here are Top 10 Data Recovery Software Of 2024.


Leave a Comment