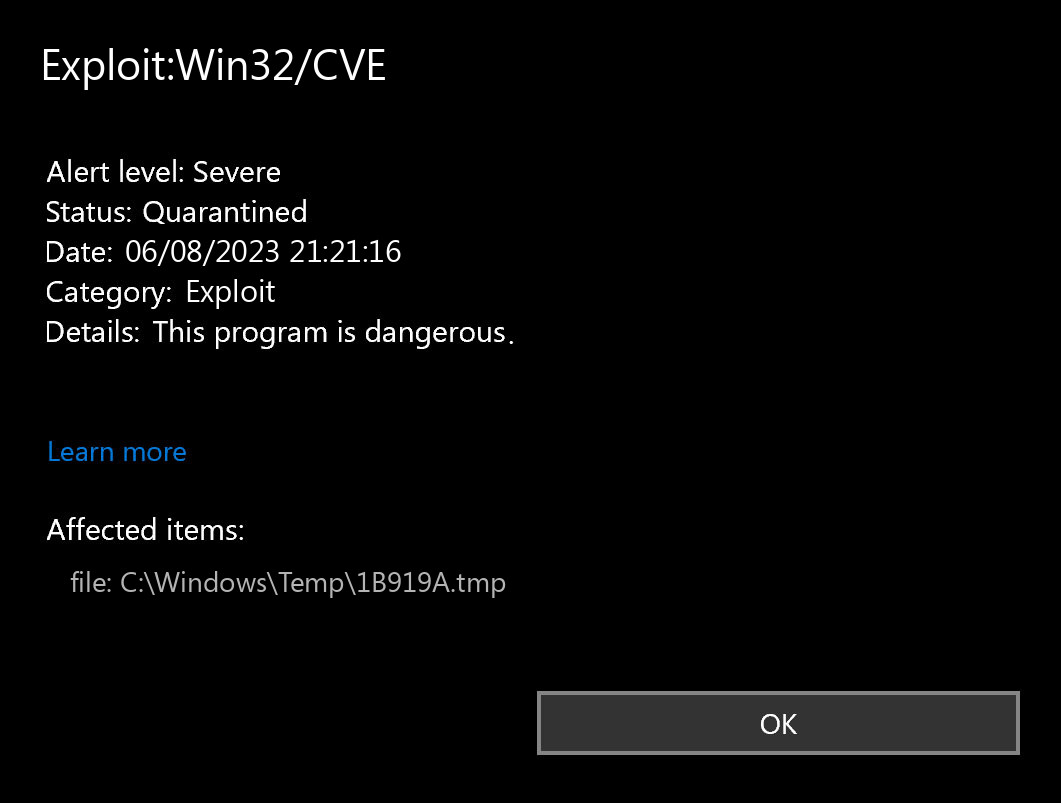
If you spectate the alert of Exploit:Win32/CVE detection, it appears that your computer has a problem. All malicious programs are dangerous, without any exceptions. CVE is a virus that hunts for security breaches in your system and makes them ready for further malware injections. Removing it must definitely be your key response after spotting the detection pop-up.
Any malware exists with the only target – make money on you. And the programmers of these things are not thinking about morality – they use all available methods. Grabbing your personal data, getting the comission for the ads you watch for them, utilizing your system components to mine cryptocurrencies – that is not the full list of what they do. Do you want to be a riding equine? That is a rhetorical question.
What does the pop-up with Exploit:Win32/CVE detection mean?
The Exploit:Win32/CVE detection you can see in the lower right side is demonstrated to you by Microsoft Defender. That anti-malware application is good at scanning, but prone to be mainly unstable. It is vulnerable to malware invasions, it has a glitchy interface and bugged malware clearing capabilities. Thus, the pop-up which says concerning the CVE is simply an alert that Defender has actually detected it. To remove it, you will likely need to use a separate anti-malware program.
The exact Exploit:Win32/CVE infection is a very undesirable thing. Exploits are like open gates for other viruses. They take advantage of the exposures in the apps you have installed on your computer. After examining your system and discovering all exploitable security breaches, viruses like CVE download other malware. The specific kind of malware can be any of the ones present nowadays – coin miners, backdoors or spyware, for example. Their activity is quiet, so you will definitely fail to see the instant when that malware begins its task. However, you will definitely be dissatisfied to observe what happens to your PC when it downloads a payload of other viruses.
Exploit Summary:
| Name | CVE Exploit |
| Detection | Exploit:Win32/CVE |
| Damage | CVE exploit is gain access to a computer system and then install malware on it. |
| Similar | Watrmeera, Script Exchgproxyrequest, Script Exchgproxyrequest, Trojan Nettool, Iishack, Generic, Js Kaixin, Wordperf |
| Fix Tool | See If Your System Has Been Affected by CVE exploit |
Is Exploit:Win32/CVE dangerous?
As I have actually pointed out before, non-harmful malware does not exist. And Exploit:Win32/CVE is not an exclusion. Exploit will definitely complete its dirty task if you give it a chance. And the effects of its activity will not make you happy – tons of various malware will likely make your computer entirely inoperative. Furthermore, exploits like CVE one usually inject spyware and stealer viruses. It says that not only the computer functions, but also your privacy is in danger. It is exceptionally reckless to undervalue the risk of exploits.
Exploits and counteractions
Exploits are among the most common viruses among cybercriminal groups that target at enterprises. Injecting ransomware or spyware/stealers into a corporate network that has some standard security functions allowed needs some preliminary interruptions. At the same time, they may easily be neutralized. A lot of the weakness in the programs are resolved in upcoming updates. Just install them – and make your system as well as your company network secure.
How did I get this virus?
It is difficult to line the origins of malware on your computer. Nowadays, things are mixed up, and distribution tactics utilized by adware 5 years ago can be used by spyware nowadays. But if we abstract from the exact distribution way and will think of why it works, the reply will be very simple – low level of cybersecurity awareness. People click on promotions on strange sites, open the pop-ups they get in their browsers, call the “Microsoft tech support” assuming that the weird banner that states about malware is true. It is essential to understand what is legitimate – to avoid misconceptions when trying to find out a virus.
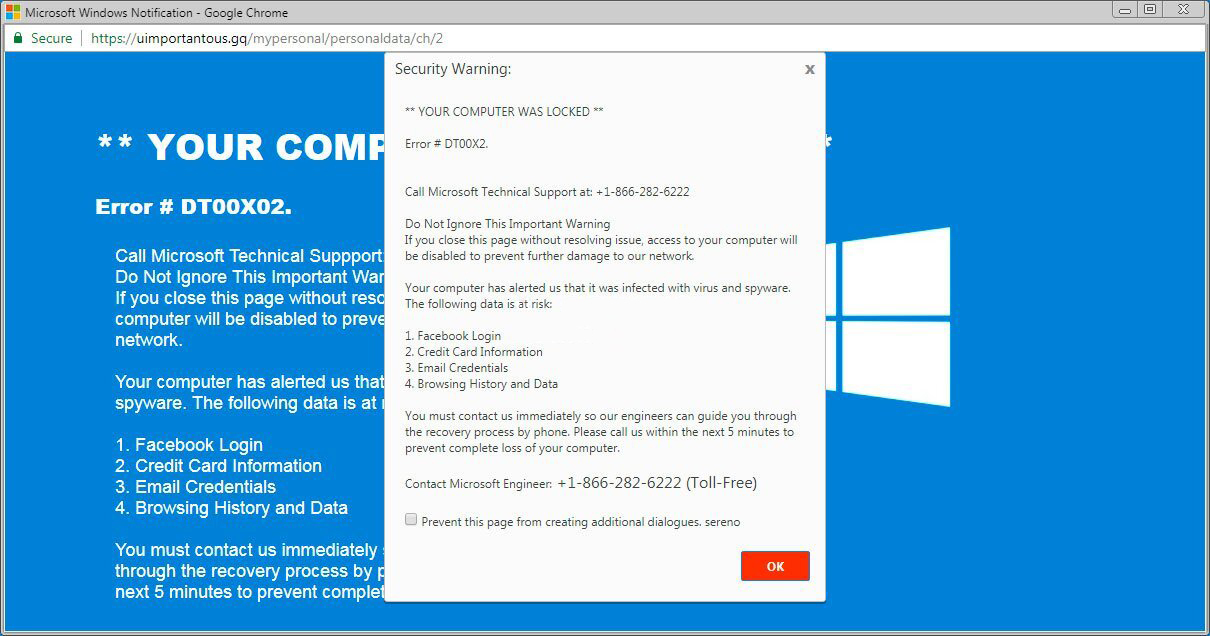
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most common tactics of malware distribution – lure emails and also injection into a hacked program. While the first one is not so easy to evade – you need to know a lot to recognize a fake – the 2nd one is simple to address: just don’t utilize cracked programs. Torrent-trackers and various other providers of “free” applications (which are, in fact, paid, but with a disabled license checking) are really a giveaway point of malware. And Exploit:Win32/CVE is just one of them.


Leave a Comment