The Exploit:Ruby/Metasploit alert means that your system has a problem. Giving it a go may lead to some really bad consequences. It is widely applied as a way for hacking system security mechanisms, an option highly needed during cyberattacks.
Metasploit is a virus that searches for weakness in your system and makes them ready for further attacks. Removing it should be your key response after noticing the detection pop-up.
Exploit:Ruby/Metasploit Detection Overview
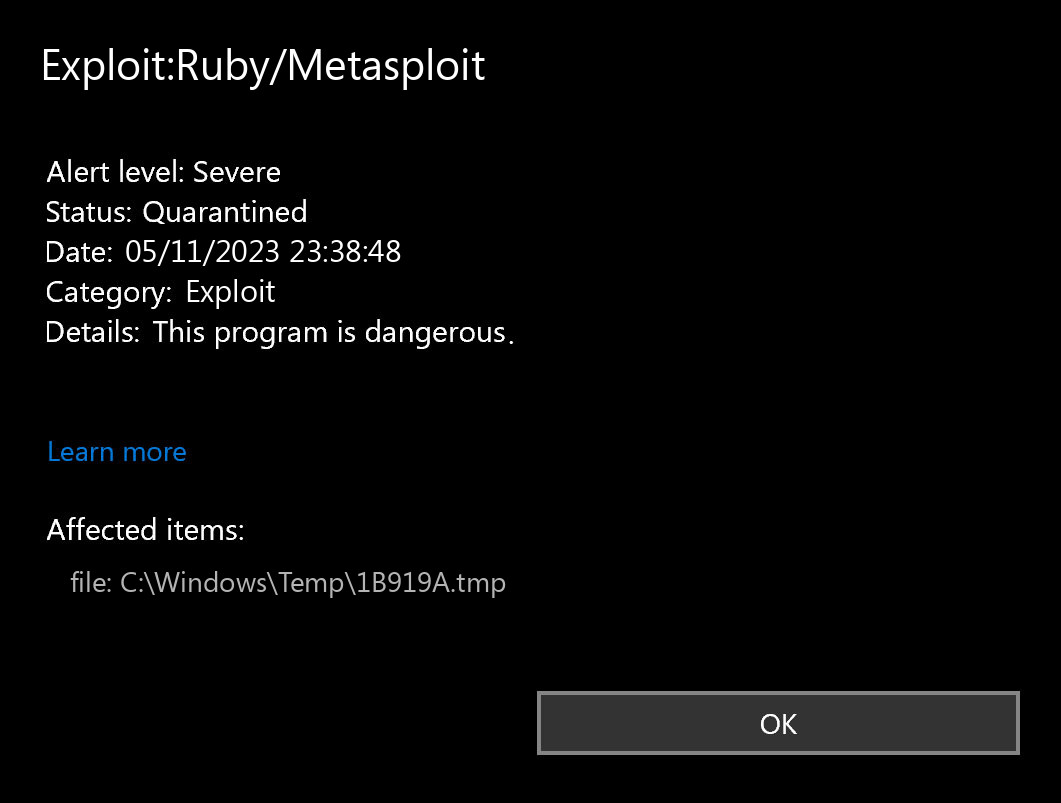
The Exploit:Ruby/Metasploit detection you can see in the lower right corner is displayed to you by Microsoft Defender. That anti-malware application is good at scanning, however, prone to be basically unreliable. It is defenseless to malware invasions, it has a glitchy user interface and bugged malware removal features. Thus, the pop-up which says concerning the Metasploit is simply an alert that Defender has actually found it. To remove it, you will likely need to use another anti-malware program.
The exact Exploit:Ruby/Metasploit infection is a very unpleasant thing. Exploits are like open gates for various other viruses. They take advantage of the exposures in the software you have installed on your computer. After examining your system and recognizing all exploitable vulnerabilities, viruses like Metasploit inject other malware. The particular kind of malware can be any of the ones present nowadays – coin miners, backdoors or spyware, for example. Their activity is quiet, so you will likely fail to see the instant when that malware commences its activity. However, you will definitely be sad to see what happens to your system when it injects a payload of additional viruses.
Exploit Summary:
| Name | Metasploit Exploit |
| Detection | Exploit:Ruby/Metasploit |
| Damage | Metasploit exploit is gain access to a computer system and then install malware on it. |
| Similar | W32 Wormlink, Cve, Watrmeera, Script Exchgproxyrequest, Script Exchgproxyrequest, Trojan Nettool, Iishack, Generic |
| Fix Tool | See If Your System Has Been Affected by Metasploit exploit |
Is Exploit:Ruby/Metasploit dangerous?
As I have actually specified before, non-harmful malware does not exist. And Exploit:Ruby/Metasploit is not an exception. Exploit will likely complete its dirty task if you give it a chance. And the results of its activity will not make you pleased – tons of different malware will likely make your computer totally inoperative. Additionally, exploits like Metasploit one usually inject spyware and stealer viruses. It means that not only the system functions, but also your personal privacy is in danger. It is exceptionally thoughtless to undervalue the threat of exploits.
Exploits and counteractions
Exploits are among the most prevalent viruses among cybercriminal organizations who aim at corporations. Injecting ransomware or spyware/stealers into a corporate network that has some typical security components allowed needs some initial intrusions. Meanwhile, they may quickly be counteracted. Most of the vulnerabilities in the software are resolved in upcoming updates. Just install them – and make your system as well as your company network protected.


Leave a Comment