What is DOC/TrojanDownloader.Agent.CGP infection?
In this short article you will certainly find about the definition of DOC/TrojanDownloader.Agent.CGP as well as its negative effect on your computer. Such ransomware are a kind of malware that is specified by on the internet scams to demand paying the ransom money by a sufferer.
Most of the instances, DOC/TrojanDownloader.Agent.CGP ransomware will certainly advise its victims to initiate funds move for the purpose of counteracting the modifications that the Trojan infection has actually presented to the sufferer’s device.
DOC/TrojanDownloader.Agent.CGP Summary
These alterations can be as follows:
- Attempts to connect to a dead IP:Port (1 unique times);
- A process created a hidden window;
- Performs some HTTP requests;
- A potential decoy document was displayed to the user;
- A document file initiated network communications indicative of a potential exploit or payload download;
- Ciphering the papers located on the sufferer’s hard disk drive — so the victim can no more use the data;
- Preventing routine accessibility to the target’s workstation. This is the typical behavior of a virus called locker. It blocks access to the computer until the victim pays the ransom.
Similar behavior
Related domains
| saeshoes.com | Ransom.U.Qakbot.lu |
DOC/TrojanDownloader.Agent.CGP
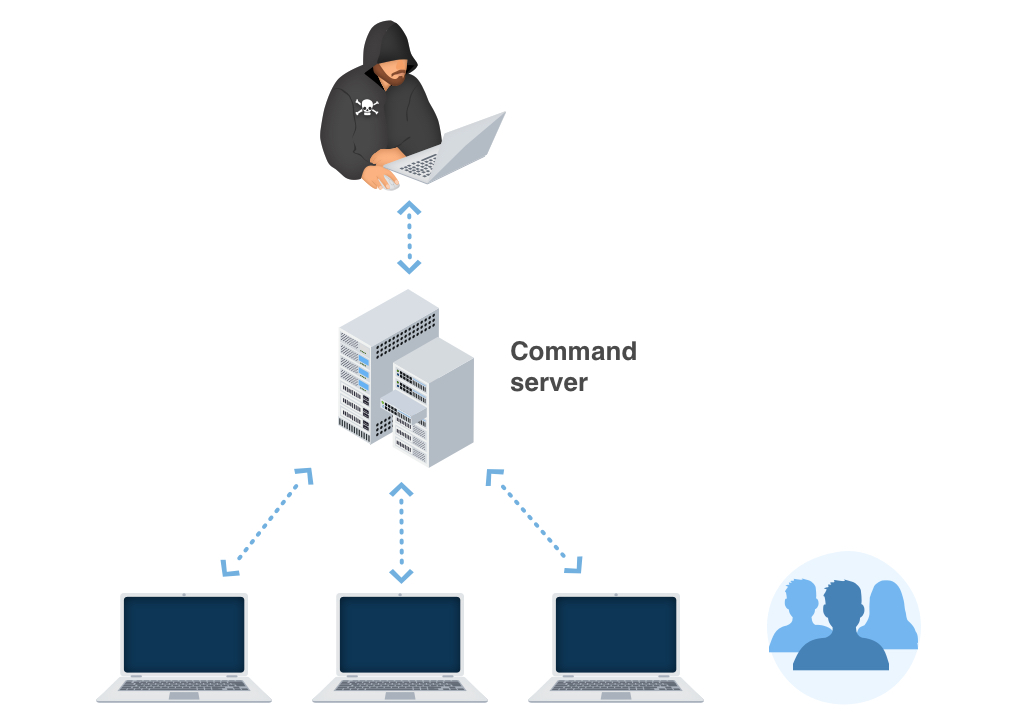
The most typical networks through which DOC/TrojanDownloader.Agent.CGP are injected are:
- By methods of phishing e-mails. Email phishing is a cyber attack that uses disguised email as a goal is to trick the recipient into believing that the message is something they want or need — a request from their bank, for instance, or a note from someone in their company — and to click a link for download a malware.
- As a consequence of individual winding up on a source that organizes a malicious software program;
As soon as the Trojan is successfully injected, it will either cipher the data on the victim’s PC or avoid the gadget from working in a proper way – while also placing a ransom money note that points out the requirement for the sufferers to effect the settlement for the function of decrypting the files or restoring the data system back to the preliminary problem. In most circumstances, the ransom note will certainly come up when the customer restarts the COMPUTER after the system has actually already been harmed.
DOC/TrojanDownloader.Agent.CGP circulation networks.
In various edges of the world, DOC/TrojanDownloader.Agent.CGP expands by leaps as well as bounds. Nevertheless, the ransom money notes and also techniques of obtaining the ransom amount might vary depending on particular local (local) settings. The ransom money notes as well as methods of obtaining the ransom money amount might vary depending on specific local (regional) setups.
For example:
Faulty alerts about unlicensed software application.
In specific areas, the Trojans typically wrongfully report having found some unlicensed applications enabled on the target’s gadget. The alert after that requires the user to pay the ransom.
Faulty statements concerning illegal content.
In nations where software application piracy is less preferred, this approach is not as effective for the cyber fraudulences. Conversely, the DOC/TrojanDownloader.Agent.CGP popup alert might wrongly claim to be stemming from a law enforcement establishment and also will report having situated kid porn or various other illegal data on the device.
DOC/TrojanDownloader.Agent.CGP popup alert may falsely assert to be deriving from a law enforcement organization as well as will certainly report having situated kid porn or various other illegal data on the tool. The alert will likewise include a demand for the individual to pay the ransom money.
Technical details
File Info:
crc32: D54089FBmd5: 0a86c9a66be83b5032df9fa5d84f79bfname: upload_filesha1: 0e2f4cd816bec7788db0c70a68f81fb5843bf49bsha256: c033e2bf0fc650b5d36baeb574d2777637c6d4e03c647b6cef5b2ce6a3ee1d40sha512: bb6529461b0eb2128c853aad5884022c52ee07a4a869431354790316725fdba8c288c4853fb1cba0632fb61a8e821eff3c8276cba884e7ca778c7a7f1309e7c1ssdeep: 768:imNBYBDPMEWAyS8NEJyDQdUzaGcoo54CPEK:imNGdbyS8NStd209FPEKtype: Microsoft Excel 2007+Version Info:
0: [No Data]
DOC/TrojanDownloader.Agent.CGP also known as:
| GridinSoft | Trojan.Ransom.Gen |
| McAfee | X97M/Downloader.fk |
| Kaspersky | HEUR:Trojan-Downloader.MSOffice.SLoad.gen |
| McAfee-GW-Edition | Artemis!Trojan |
| Ikarus | Trojan.Dropper |
| Microsoft | TrojanDownloader:O97M/Qakbot.PB!MTB |
| Gridinsoft | Ransom.U.Qakbot.lu |
| ZoneAlarm | HEUR:Trojan-Downloader.MSOffice.SLoad.gen |
| ESET-NOD32 | DOC/TrojanDownloader.Agent.CGP |
| Fortinet | MSExcel/Agent.CGJ!tr.dldr |
How to remove DOC/TrojanDownloader.Agent.CGP ransomware?
Unwanted application has ofter come with other viruses and spyware. This threats can steal account credentials, or crypt your documents for ransom.
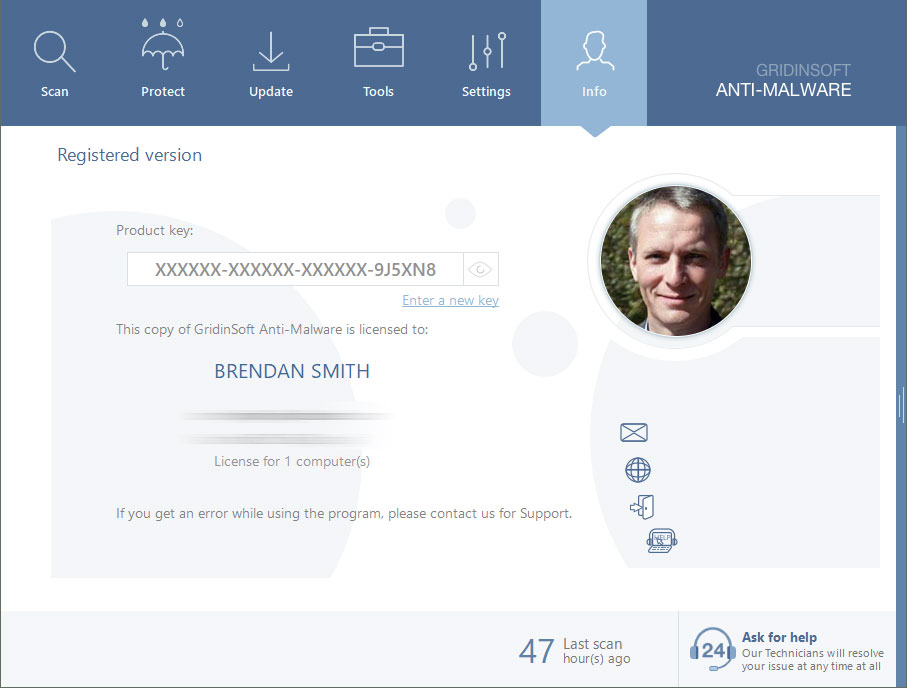
Reasons why I would recommend GridinSoft1
The is an excellent way to deal with recognizing and removing threats – using Gridinsoft Anti-Malware. This program will scan your PC, find and neutralize all suspicious processes.2.
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for DOC/TrojanDownloader.Agent.CGP files and other malicious programs. This process can take a 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.

Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offer real-time protection for first 2 days. If you want to be fully protected at all times – I can recommended you to purchase a full version:
If the guide doesn’t help you to remove DOC/TrojanDownloader.Agent.CGP you can always ask me in the comments for getting help.
User Review
( votes)References
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison