The Deathfile virus belongs to the MedusaLocker ransomware family. This ransomware encrypts all user’s data on the PC (photos, documents, excel tables, music, videos, etc), adds its specific extension to every file.
Deathfile Virus
☝️ Deathfile can be correctly identify as a MedusaLocker ransomware-type infection.
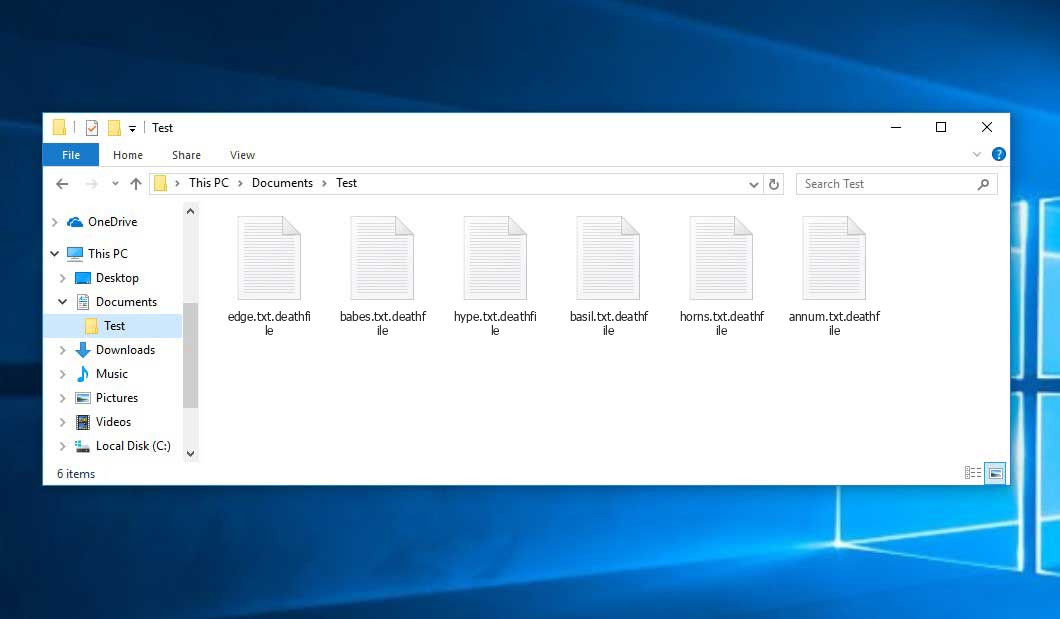
Deathfile adds its specific “.deathfile” extension to the name of every file. For example, your photo named as “my_photo.jpeg” will be transformed into “my_photo.jpeg.deathfile“, report in Excel tables named “report.xlsx” – to “report.xlsx.deathfile“, and so on.
Inside of the ransom note, there is usually an instruction saying about purchasing the decryption tool. This decryption tool is created by ransomware developers.
Here is a Recovery_Instructions.html
YOUR PERSONAL ID:
-
/!\ YOUR COMPANY NETWORK HAS BEEN PENETRATED /!\
All your important files have been encrypted!
Your files are safe! Only modified. (RSA+AES)
ANY ATTEMPT TO RESTORE YOUR FILES WITH THIRD-PARTY SOFTWARE
WILL PERMANENTLY CORRUPT IT.
DO NOT MODIFY ENCRYPTED FILES.
DO NOT RENAME ENCRYPTED FILES.
No software available on internet can help you. We are the only ones able to
solve your problem.
We gathered highly confidential/personal data. These data are currently stored on
a private server. This server will be immediately destroyed after your payment.
If you decide to not pay, we will release your data to public or re-seller.
So you can expect your data to be publicly available in the near future..
We only seek money and our goal is not to damage your reputation or prevent
your business from running.
You will can send us 2-3 non-important files and we will decrypt it for free
to prove we are able to give your files back.
Contact us for price and get decryption software.
hxxp://gvlay6u4g53rxdi5.onion/21-waFUDgYyUeAjcQQEdFOrZkA KjF8qu47B-ULRruZ5GNsCcrkIrFs1s5eoAcoQLfxUa
* Note that this server is available via Tor browser only
Follow the instructions to open the link:
1. Type the addres "hxxps://www.torproject.org" in your Internet browser. It opens the Tor site.
2. Press "Download Tor", then press "Download Tor Browser Bundle", install and run it.
3. Now you have Tor browser. In the Tor Browser open "{{URL}}".
4. Start a chat and follow the further instructions.
If you can not use the above link, use the email:
[email protected]
[email protected]
* To contact us, create a new mail on the site: protonmail.com
Make contact as soon as possible. Your private key (decryption key)
is only stored temporarily.
IF YOU DON'T CONTACT US WITHIN 72 HOURS, PRICE WILL BE HIGHER.
Here is a summary for the Deathfile:
| Name | Deathfile Virus |
| Ransomware family1 | MedusaLocker ransomware |
| Extension | .deathfile |
| Criminal Contact | [email protected], [email protected] |
| Ransom Message | Recovery_Instructions.html |
| Detection | Generik.JBLJKZL, Trojan.Win32.Deapax.pef, Trojan.Win32.Eb.blq |
| Symptoms | Your files (photos, videos, documents) have a .deathfile extension and you can’t open it. |
| Fix Tool | See If Your System Has Been Affected by Deathfile virus |
The image below gives a clear vision of how the files with “.deathfile” extension look like:
How did I get MedusaLocker?
When the MedusaLocker ransomware is mounted to your PC, it will do different startup routines to prepare your computer for encryption
Step 1
MedusaLocker will create the Registry value EnableLinkedConnections under the HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System registry key and also established it to 1. This is done to make certain mapped drives come also in a UAC launched process.
Step 2
Next, ransomware will restart the LanmanWorkstation service in order to make certain that Windows networking is running which mapped network drives come.
Step 3
MedusaLocker will seek as well as end the complying with procedures in order to shut down security programs and to make certain all data files are closed and easily accessible for encrypting:
wrapper, DefWatch, ccEvtMgr, ccSetMgr, SavRoam, sqlservr, sqlagent, sqladhlp, Culserver, RTVscan, sqlbrowser, SQLADHLP, QBIDPService, Intuit.QuickBooks.FCS, QBCFMonitorService, sqlwriter, msmdsrv, tomcat6, zhudongfangyu, SQLADHLP, vmware-usbarbitator64, vmware-converter, dbsrv12, dbeng8, wxServer.exe, wxServerView, sqlservr.exe, sqlmangr.exe, RAgui.exe, supervise.exe, Culture.exe, RTVscan.exe, Defwatch.exe, sqlbrowser.exe, winword.exe, QBW32.exe, QBDBMgr.exe, qbupdate.exe, QBCFMonitorService.exe, axlbridge.exe, QBIDPService.exe, httpd.exe, fdlauncher.exe, MsDtSrvr.exe, tomcat6.exe, java.exe, 360se.exe, 360doctor.exe, wdswfsafe.exe, fdlauncher.exe, fdhost.exe, GDscan.exe, ZhuDongFangYu.exe
Step 4
Finally, it gets rid of the Shadow Volume Copies to ensure that they can not be made use of to bring back files, gets rid of back-ups made with Windows back-up, and also disables the Windows automatic start-up repair work making use of the complying with commands:
vssadmin.exe Delete Shadows /All /Quiet
wmic.exe SHADOWCOPY /nointeractive
bcdedit.exe /set {default} recoveryenabled No
bcdedit.exe /set {default} bootstatuspolicy ignoreallfailures
wbadmin DELETE SYSTEMSTATEBACKUP
wbadmin DELETE SYSTEMSTATEBACKUP -deleteOldest
Step 5
MedusaLocker will currently begin to scan the computer’s drives for files to encrypt. When encrypting documents, it will miss all data that have the extensions.exe,. dll,. sys,. ini,. lnk,. rdp,. encrypted (or other expansion utilized for encrypted files) in addition to data in the adhering to folders.
USERPROFILE PROGRAMFILES(x86) ProgramData \AppData WINDIR \Application Data \Program Files \Users\All Users \Windows \intel \nvidia
When encrypting documents, it will use AES file encryption to encrypt the data and afterwards the AES key will be encrypted by a RSA-2048 public key consisted of in the virus executable.
For every data that is encrypted, it will add among the adhering to extensions depending on the version of the ransomware.
- .encrypted
- .bomber
- .boroff
- .breakingbad
- .locker16
- .newlock
- .nlocker
- .skynet
When done, the ransomware will rest for 60 secs and afterward scan the drives again for new files to encrypt.
When mounted, this ransomware will likewise duplicate itself to %UserProfile%\AppData\Roaming\svchostt.exe and also create a scheduled job that releases the program every 30 mins in order to continue to be resident.
How to remove Deathfile virus?
In addition to encode a victim’s files, the Deathfile infection has also started to install the Azorult Spyware on system to steal account credentials, cryptocurrency wallets, desktop files, and more.
To ensure the user that ransomware distributors really have the decryption tool, they may offer to decrypt several encrypted files. And they are the single owners of this decryption program: Deathfile ransomware is a completely new type, so there is no legit program from anti-malware vendors, which can decrypt your files. But such a situation is in momentum: decryption tools are updating every month.
However, paying the ransom is a bad decision, too. There is no guarantee that Deathfile ransomware developers will send you the decryption tool and a proper decryption key. And there are a lot of cases when ransomware distributors deceived their victims, sending the wrong key or even nothing. In the majority of cases, there is a way to recover your files for free. Search for available backups, and restore your system using it. Of course, there is a chance that the backup you found is too old, and does not contain a lot of files you need. But, at least you will be sure that there is no malware in your system. However, to ensure that there are no malicious programs in your system after the backup, you need to scan your PC with anti-malware software.
Deathfile ransomware is not unique. These examples of ransomware act in a similar way: encrypting your files, adding a specific extension, and leaving a great number of ransom money notes in every folder. But there are two things that make difference between these ransomware – cryptography algorithm, which is used for file encryption, and ransom amount. In some cases, victims are able to decrypt their files without any payments, just using free solutions produced by several anti-malware vendors, or even with the decryption tool which is offered by ransomware creators. The last scenario is possible when ransomware distributors have typed your decryption key inside of a ransom money note. However, as you can already guess, such luck is a very rare thing. Ransomware is created for money gaining, not for jokes or scaring.
Reasons why I would recommend GridinSoft2
The is an excellent way to deal with recognizing and removing threats – using Gridinsoft Anti-Malware. This program will scan your PC, find and neutralize all suspicious processes3.
Download Removal Tool.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When setup file has finished downloading, double-click on the setup-antimalware-fix.exe file to install GridinSoft Anti-Malware on your PC.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your PC for Deathfile infections and other malicious programs. This process can take a 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has completed, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in right corner.

Frequently Asked Questions
No way. These files are encrypted by Deathfile ransomware. The contents of .deathfile files are not available until they are decrypted.
If your data remained in the .deathfile files are very valuable, then most likely you made a backup copy.
If not, then you can try to restore them through the system function – Restore Point. All other methods will require patience.
Of course not. Your encrypted files do not pose a threat to the computer. What happened has already happened.
You need GridinSoft Anti-Malware to remove active system infections. The virus that encrypted your files is most likely still active and periodically runs a test for the ability to encrypt even more files. Also, these viruses install keyloggers and backdoors for further malicious actions (for example, theft of passwords, credit cards) often.
In this situation, you need to prepare the memory stick with a pre-installed Trojan Killer.
You can try to find a copy of an original file that was encrypted:
- Files you downloaded from the Internet that were encrypted and you can download again to get the original.
- Pictures that you shared with family and friends that they can just send back to you.
- Photos that you uploaded on social media or cloud services like Carbonite, OneDrive, iDrive, Google Drive, etc)
- Attachments in emails you sent or received and saved.
- Files on an older computer, flash drive, external drive, camera memory card, or iPhone where you transferred data to the infected computer.
Also, you can contact the following government fraud and scam sites to report this attack:
- In the United States: On Guard Online;
- In Canada: Canadian Anti-Fraud Centre;
- In the United Kingdom: Action Fraud;
- In Australia: SCAMwatch;
- In New Zealand: Consumer Affairs Scams;
- In France: Agence nationale de la sécurité des systèmes d’information;
- In Germany: Bundesamt für Sicherheit in der Informationstechnik;
- In Ireland: An Garda Síochána;
To report the attack, you can contact local executive boards. For instance, if you live in USA, you can have a talk with FBI Local field office, IC3 or Secret Service.
How сan I avoid ransomware attack?
Deathfile ransomware doesn’t have a superpower.
You can easily protect yourself from its injection in several easy steps :
- Ignore all emails from unknown mailboxes with a strange unknown address, or with content that has likely no connection to something you are waiting for (can you win in a lottery without taking part in it?). If the email subject is likely something you are waiting for, check carefully all elements of the suspicious letter. A fake email will surely contain a mistake.
- Do not use cracked or untrusted programs. Trojans are often distributed as a part of cracked software, possibly under the guise of “patch” which prevents the license check. But untrusted programs are very hard to distinguish from trustworthy software, because trojans may also have the functionality you need. You can try to find information about this program on the anti-malware forums, but the best solution is not to use such programs.
- And to be sure about the safety of the files you downloaded, use GridinSoft Anti-Malware. This program will surely be a perfect shield for your personal computer.
I need your help to share this article.
It is your turn to help other people. I have written this guide to help people like you. You can use the buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan SmithHow to Remove DEATHFILE Ransomware & Recover PC

Name: DEATHFILE Virus
Description: DEATHFILE Virus is a ransomware-type infections. This virus encrypts important personal files (video, photos, documents). The encrypted files can be tracked by a specific .deathfile extension. So, you can't use them at all.
Operating System: Windows
Application Category: Virus
User Review
( votes)References
- My files are encrypted by ransomware, what should I do now?
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison