ZDNet reports that Ryuk ransomware attacked a well-known government contractor of US Department of Defense, Electronic Warfare Associates (EWA), which manufactures electronics. Apparently, the attack was successful.
According to EWA’s official website, the company works with the U.S. Department of Defense, the U.S. Department of Homeland Security and the U.S. Department of Justice.Electronic Warfare Associates (EWA), a 40-year-old electronics company and a well-known US government contractor, has suffered a ransomware infection, ZDNet has learned. The infection hit the company last week. Among the systems that had data encrypted during the incident were the company’s web servers”, — writes ZDNet.
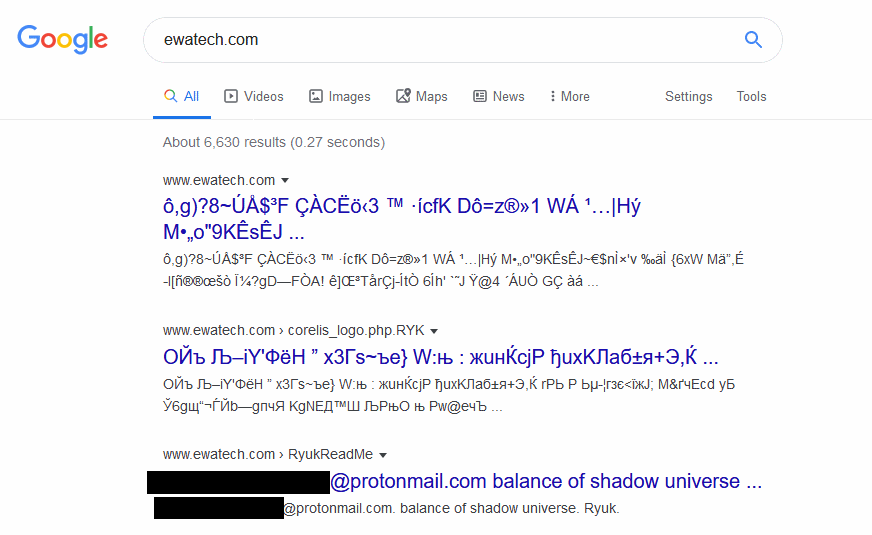
The attack affected the company’s web servers: traces of this can still be found on the Internet. Even a week later, encrypted files and ransom messages are still available in the Google cache, although the company turned off the attacked web servers long time age.
ZDNet journalists consulted with Information security experts, which say that the encrypted files and a ransom demand no doubt indicate an attack by the Ryuk ransomware.
Apparently, several EWA-owned sites were affected during the attack, including:
- EWA Government Systems Inc. – a subsidiary of EWA, it provides electronic warfare equipment to government and commercial clients, and is engaged in the development of radars, reconnaissance, security, training, planning tactical missions, information management and so on;
- EWA Technologies Inc. – a subsidiary of EWA, specializing in JTAG-products;
- Simplicikey is another EWA subsidiary specializing in the manufacturing of remote-controlled locking devices for the consumer market;
- Homeland Protection Institute is a nonprofit organization chaired by the CEO of EWA.
It is still unknown what exactly in the company’s internal network was damaged during the incident, since the EWA has not yet issued public statements about the incident, and company representatives refused to speak with reporters.
Making matters worse is that Ryuk is not your regular ransomware strain. This type of ransomware is solely used in targeted attacks on high-profile companies. It is usually installed on infected networks after a victim is infected with the Emotet/TrickBot trojans, two well-known cybercrime-as-a-service platforms. The data exfiltration happens via a Ryuk module called the Ryuk Stealer, which security researchers have been spotting deployed in recent Ryuk attacks”, — write ZDNEet journalists.
Interestingly, in September 2019, Ryuk was updated in such a way that it could not only encrypt files, but also to steal financial information, as well as secret data of military and law enforcement agencies.
Recently it has also been revealed that Ryuk ransomware now uses the Wake-on-LAN feature to turn on devices in a compromised network and ensure better encryption. Moreover, according to a recent report by Bleeping Computer, the developers of malware continue to improve this functionality by adding more new keywords and file formats.

Hi, my files still encrypted with an on line keys, is there any solutions please, thank you