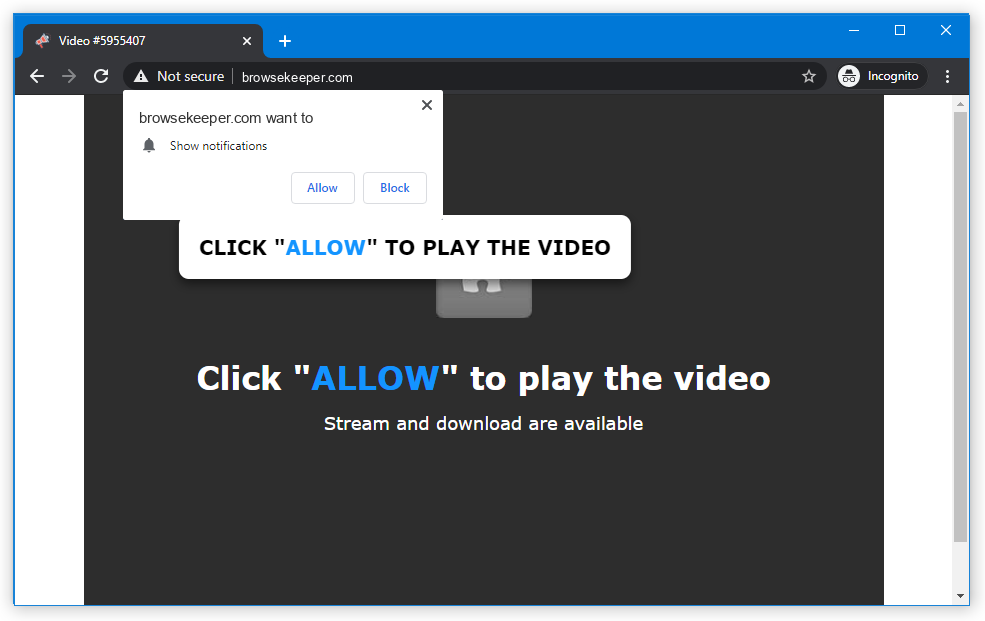
Browsekeeper pop-ups appear when you do not expect, distracting and irritating you. Nonetheless, they are slightly more than annoying notifications – their origins is purely malicious, and they may install other malware to your device. In this article, I will guide you on how to remove Browsekeeper pop-up advertisements and explain how to avoid them in the future.
Any interaction with Browsekeeper pop-up advertisements will be ineffective at best. At worst, the websites it can throw you to may introduce malware to your system. These pop-ups can also advertise fake shopping sites which will take your money and payment info. The latter generally ends up with losing all the money you have on the exposed card.
What are Browsekeeper pop-up notifications?
As the pop-up definition goes, these are short and small advertisements that attract your attention to a product they promote. But the difference between regular pop-up notifications and Browsekeeper notifications is the malignant origins of the latter. Common pop-up ads are offered for you to enable on different sites with a benevolent purpose – keep you aware about the latest posts, goods for sale and so on. It is an effective approach to help your site to retain visitors and help the interested users to have the best deal.
Brief description of the Browsekeeper.com pop-ups:
| Name | Browsekeeper.com |
| Hosting | AS13335 Cloudflare, Inc. United States, San Francisco |
| IP Address | 172.64.111.31 |
| Malware type | Adware1 |
| Effect | Unwanted pop-up advertisements |
| Hazard level | Medium |
| Malware source | Apps from third-party websites, ads on dubious websites |
| Similar behavior | Ismilinstite, Thunderforge, Bushbunshot |
| Removal method |
To remove possible virus infections, try to scan your PC
|
Browsekeeper pop-up ads, in contrast, have a deal with less legit web pages. You will generally witness the proposition to enable them following the redirection from another website. Redirects are OK unless it throws you into such a questionable place. In this case, enabling pop-up notifications is served under the guise of the anti-bot filtering. In other cases, the sites can refuse to show you the contents unless you enable these push notifications. These demands should already be the red flag, as sites usually have a more convenient anti-bot mechanism. Spectating such an requirement is a reason to close the website doubtlessly. Sometimes, even after clicking “Allow”, you will not get to the site – it has only a landing page with the offer to turn on the pop-up notifications.
How does this work?
The vast majority of web browsers support enabling pop-ups from websites. Sites, on the other hand, can send notifications with the content of their choice. It may be an advertisement of the page listed for sale on this particular site, or an ad of their partner page. As a result, you can see the pop-up from site X, but interacting with it will direct you to website Y – because a link to that website was embedded.
Cyber burglars rely on this ability in their attempt to earn money through advertising. They trick victims into allowing them to show the banners, and after that just spread numerous ads of other crooks they contract with. As you can suppose, no legit companies will have a deal with fraudsters. All the Browsekeeper push ads you can see lead to other untrustworthy sites. At some point, the same victim may get into a trap of multiple pop-up spamming websites, and its browser will turn into a complete mess.
The ads these criminals show are paid under the pay-per-view model. It commonly provides a miserable payment for one person, but when you have hundreds of victims and make it hundreds of times every day – that is a much bigger sum. Despite most of such ads are ineffective, it may still bring all the parties a lot of profit.
Are Browsekeeper push notifications dangerous?
Yes, they are. At the surface, they can look non-threatening – just a colourful window that appears from time to time. However, the contents of this window differ drastically from what you generally see in pop-up ads. Browsekeeper.com web page is ruled by fraudsters, who intendedly spread hundreds and thousands of malicious ads in pop-ups. They also never follow any manners of advertising and can make sporadic pop-up ads into a storm of ads. For weak computers, that may be enough to cause performance issues. But problems are not over at this point.
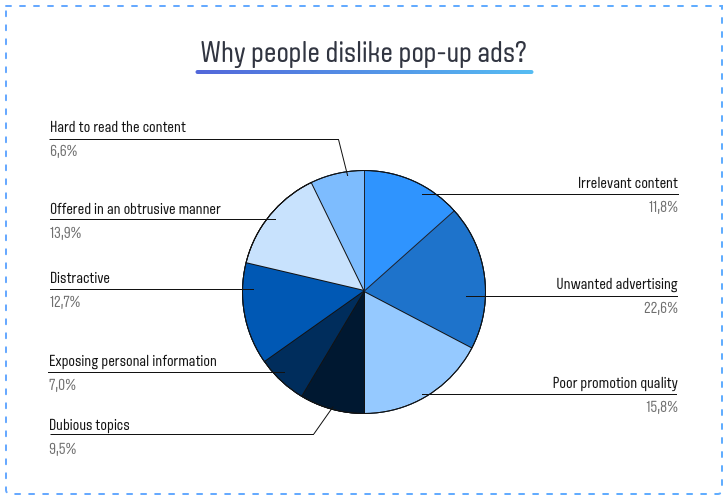
As with any other thing that touches illegal ads, Browsekeeper pop-up ads do not contain any legit offers. Even when hackers make the banners looking similar to ones from Amazon, Walmart or Ebay, the web page these ads will throw you to are completely different. And these pages can offer you to turn on other pop-ups, install a “useful” program, or pay for a thing at a big discount and never receive it. Let’s leave aside the cases when pop-ups promote phishing pages or straightforward malware. There’s no way these pages will bring you any good, thus interacting with them is a very bad idea. For the same reason, Browsekeeper push notifications are not recommended to click on either, and the best solution is to disable them as soon as possible.
How to remove Browsekeeper pop-ups?
First of all, you should reset your browser settings. It is possible to do in both manual and automatic manner. The former, obviously, requires more time to complete and may be somewhat complicated if you have never done that. Automated supposes the use of anti-malware programs that can reset all browser settings at once.
Reset your browsers manually
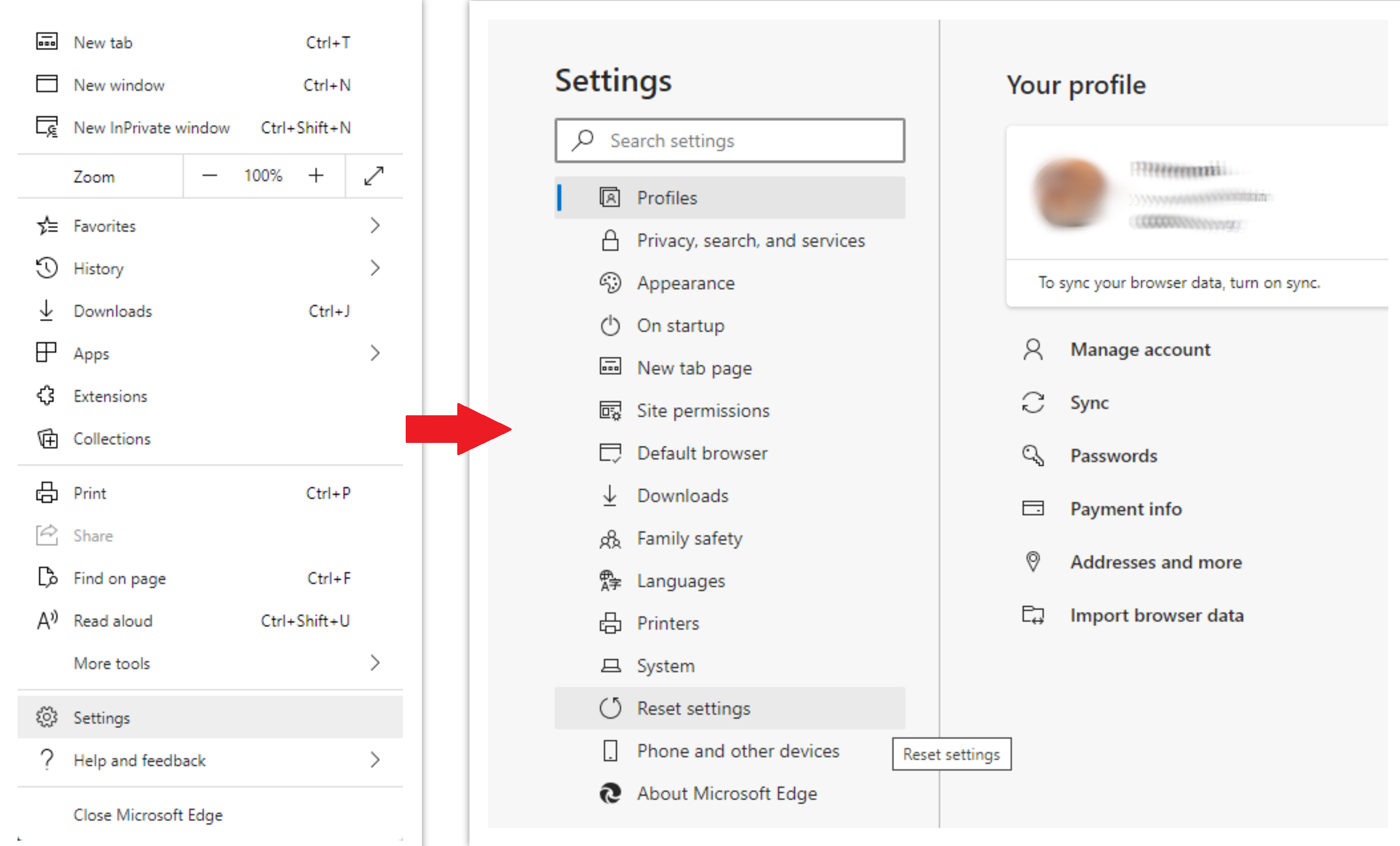
To reset Edge, do the following steps:
- Open “Settings and more” tab in upper right corner, then find here “Settings” button. In the appeared menu, choose “Reset settings” option:
- After picking the Reset Settings option, you will see the following menu, stating about the settings which will be reverted to original:
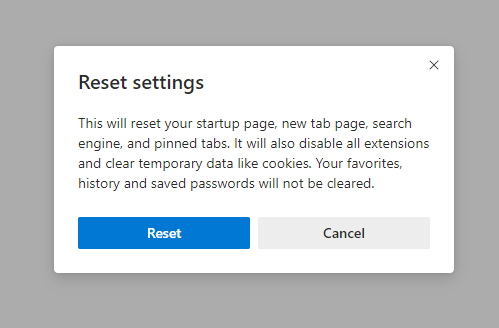
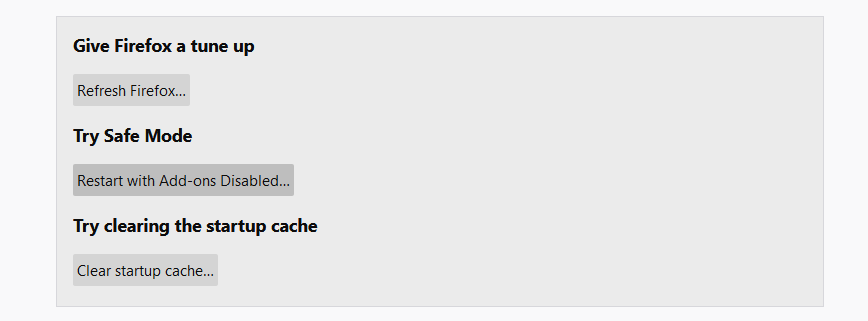
For Mozilla Firefox, do the next actions:
- Open Menu tab (three strips in upper right corner) and click the “Help” button. In the appeared menu choose “troubleshooting information”:
- In the next screen, find the “Refresh Firefox” option:
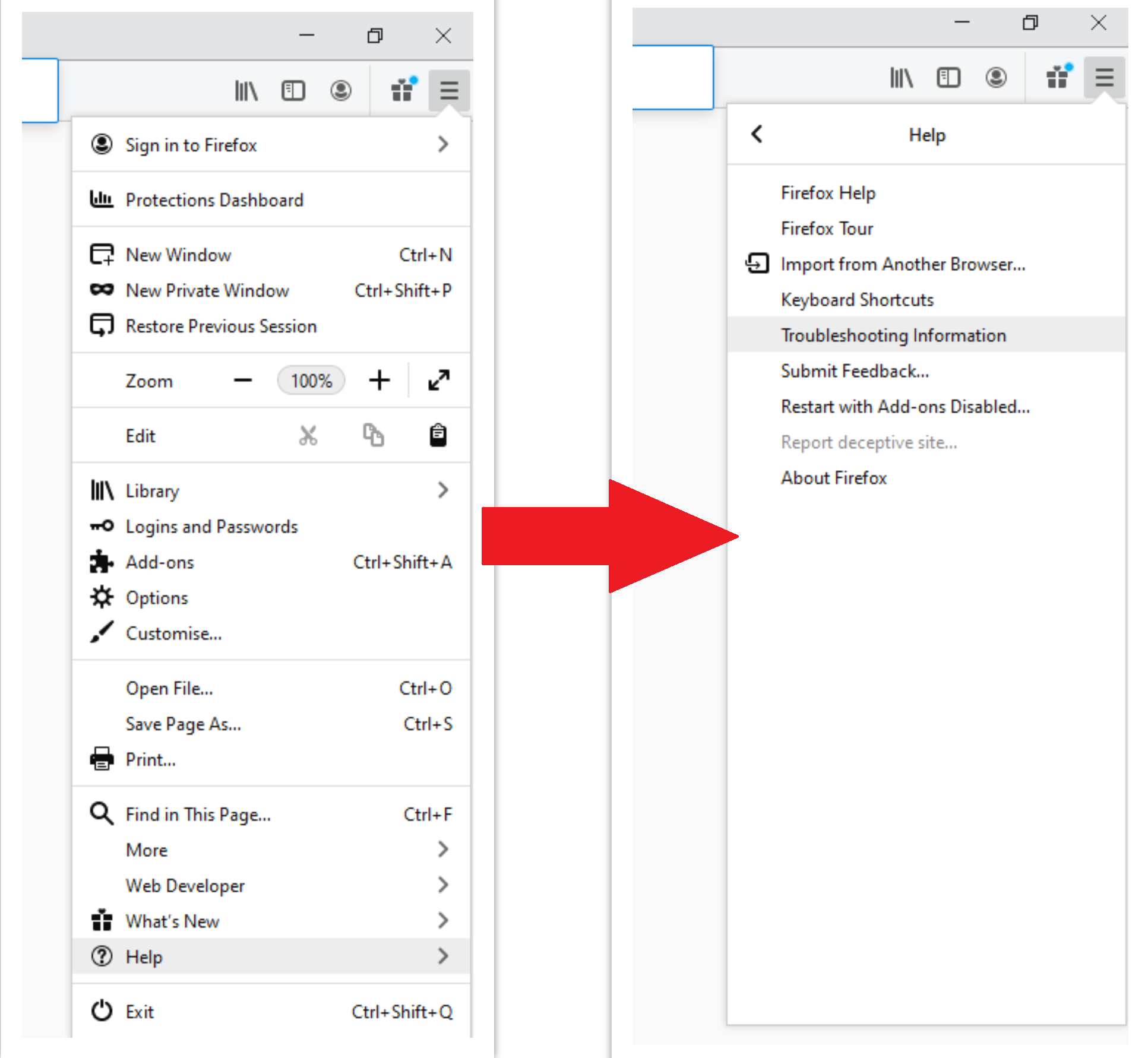
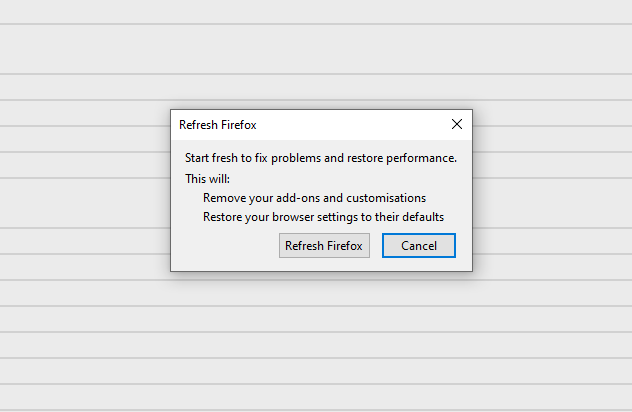
After choosing this option, you will see the next message:
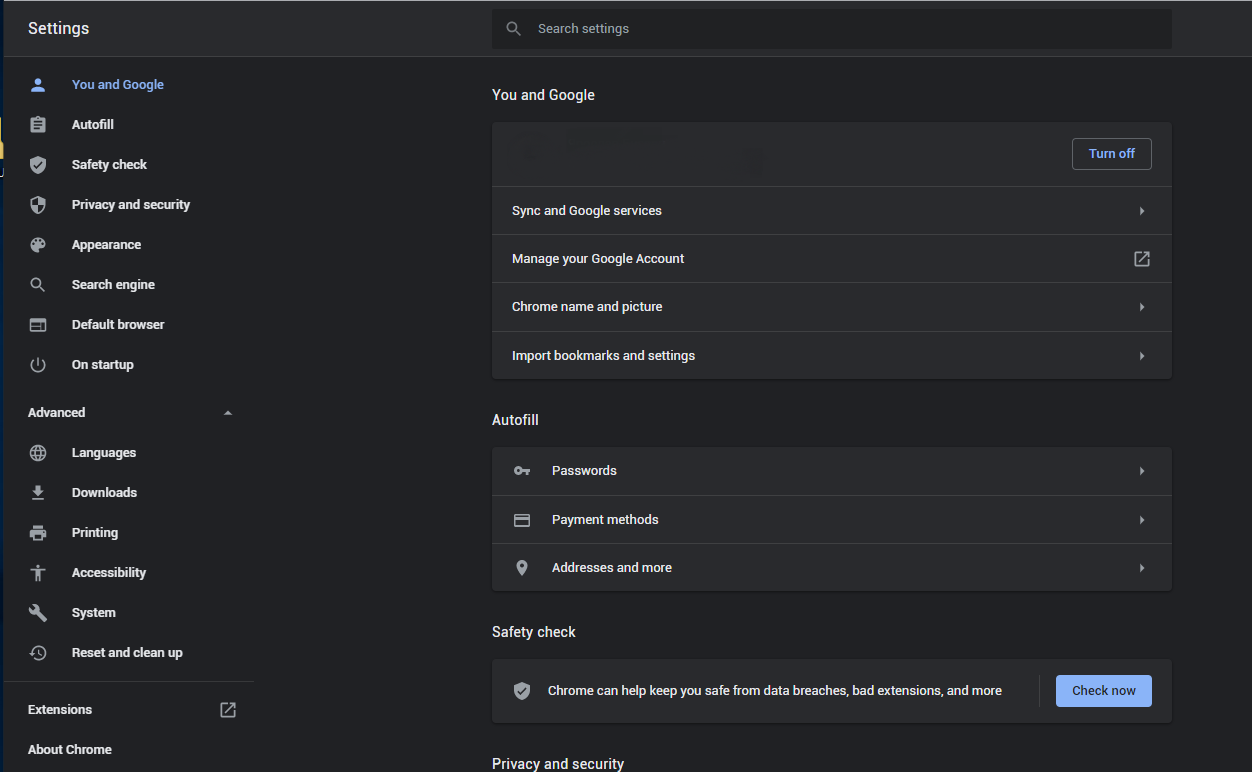
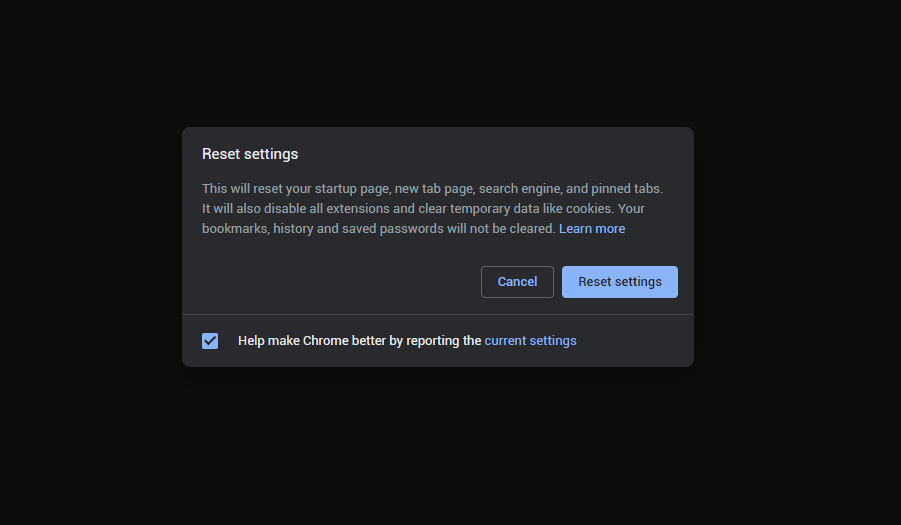
If you use Google Chrome
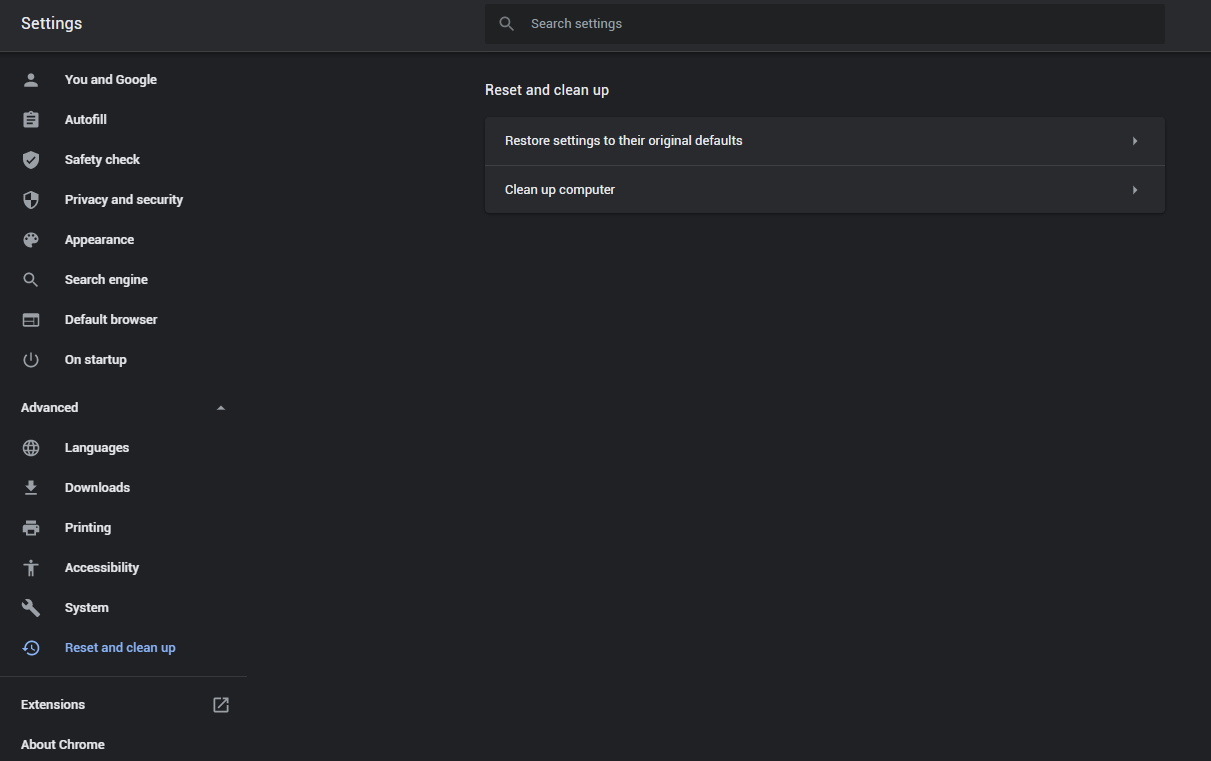
- Open Settings tab, find the “Advanced” button. In the extended tab choose the “Reset and clean up” button:
- In the appeared list, click on the “Restore settings to their original defaults”:
- Finally, you will see the window, where you can see all the settings which will be reset to default:
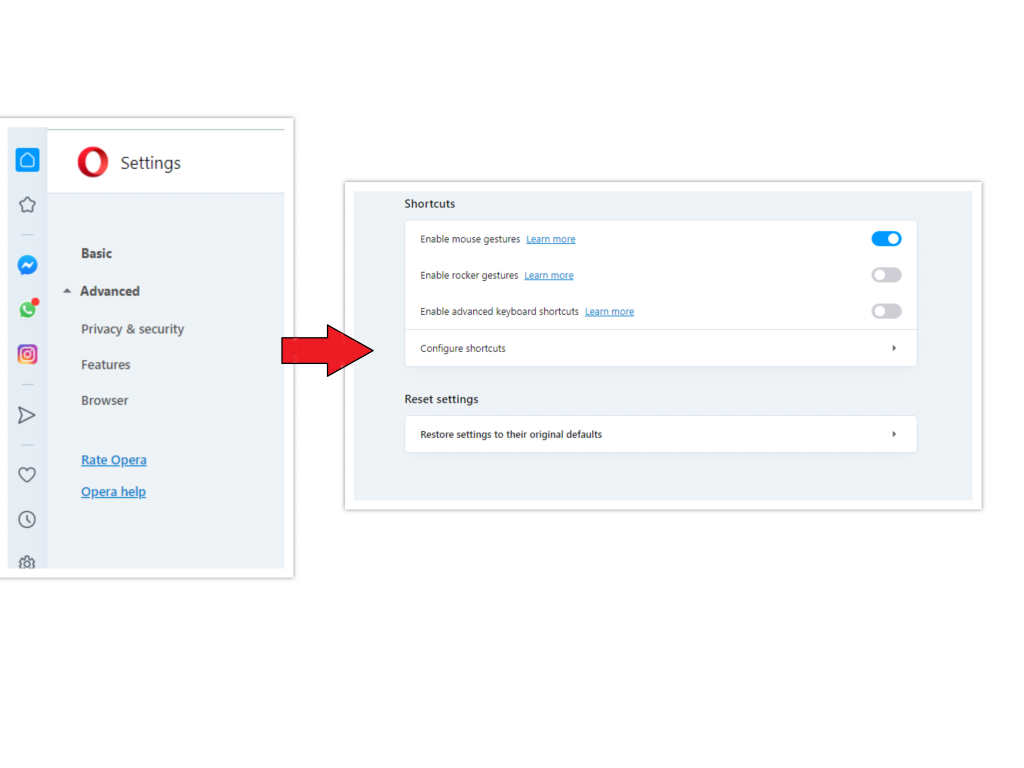
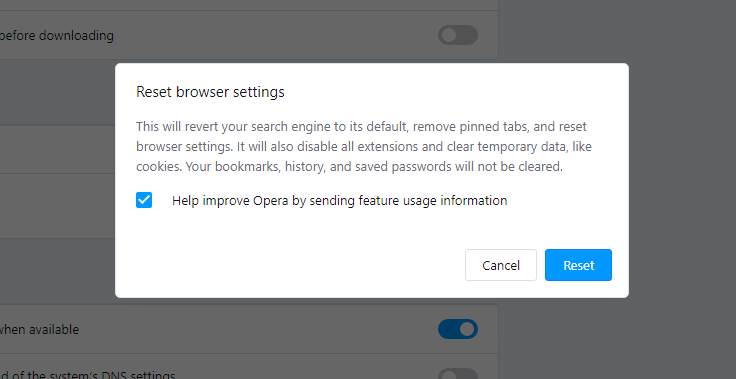
Opera can be reset in the next way
- Open Settings menu by pressing the gear icon in the toolbar (left side of the browser window), then click “Advanced” option, and choose “Browser” button in the drop-down list. Scroll down, to the bottom of the settings menu. Find there “Restore settings to their original defaults” option:
- After clicking the “Restore settings…” button, you will see the window, where all settings, which will be reset, are shown:
When the browsers are reset, you need to ensure that your browser will connect the right DNS while connecting to the site you need. Create a text file titled “hosts” on your pc’s desktop, then open it and fill it with the following lines2:
# Copyright (c) 1993-2006 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# localhost name resolution is handle within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
Find the hosts.txt file in C:/Windows/System32/drivers/etc directory. Rename this file to “hosts.old.txt” (to distinguish it from the new one), and then move the file you created on the desktop to this folder. Remove the hosts.old from this folder. Now you have your hosts file as good as new.
Scan your system for possible viruses
Once the scan is complete, you will see the detections or a notification about a clean system. Proceed with pressing the Clean Up button (or OK when nothing is detected).
References
- Official Microsoft guide for hosts file reset.


Leave a Comment