How to increase your security on the Internet
We have warned so many times about how serious security on the Internet is today, so it is not out of place to give some new tips and suggestions that will help you adequately protect yourself. Of course, 100% protection does not exist, but you can still reduce the chances of malicious hackers harming you.
First and foremost, if you notice that some emails are suspicious or look suspicious, delete them immediately. Do not open them under any circumstances. Malware and phishing scams are becoming more sophisticated, so be careful.
Also, this rule applies to all attachments you receive via email. Don’t even click on any links or sign in to some accounts, because they could “scratch”. Update your operating system, stay up to date with the latest security software, turn on automatic updates, and don’t “leave” your computer.
Be careful if you get some great offer or let you know that you inherited a lot of money from some distant relatives from Kenya. Further protection concerns blocking third-party cookies on your browser. Always use a secure wireless connection (do not use public Wi-Fi networks).
If you don’t have a strong password on your home Wi-Fi network, it’s time to create one real password that in most cases can only contain “1234” characters and the like. Yes, people aren’t too up-to-date about coming up with passwords, and they don’t know how it can hurt them. A firewall is also a must-have option and make sure that the option is turned on. Not to mention how important it is to have an antivirus program to keep your computer clean. But let’s get back to the passwords. It would be best if they had different passwords for different accounts.
So the worst solution is to have one password, so you use it everywhere. You should use eight-character passwords and have a mix of numbers and letters. Take care of your safety on the Internet, and these simple instructions can save your head.
Cybersecurity
Cybersecurity can no longer be viewed in isolation from real-world security. The damage caused by a cyberattack is very real and causes real consequences in the physical world as well. However, due to the specifics related to the technology, types, perpetrators, and victims of such attacks, the issue of cybersecurity requires special care of all those who deal with the Internet.
Cybersecurity is in the center of interest of modern society thanks to the rapid expansion of the number of Internet users, which repeated the old truth that technology can be both useful and threatening. What can be used for the benefit of society, can also be used to its detriment.
The accompanying effect of the sudden integration of the Internet into almost all forms of human activity is the increased vulnerability of modern society to cyber attacks. The Internet is part of a critical global infrastructure and many other essential services of modern society (e-Commerce, e-Banking) are increasingly dependent on the Internet and are a frequent target of cyberattacks.
Remembering passwords and using managers
When you have more complicated passwords like this, the problem is remembering or forgetting them. In such a situation, the solution will be to use a password management application. These are applications through which you enter all the codes that are important to you in the encrypted database, which you will automatically use by going to the sites where you need to log in. All you have to do is create one main, extremely strong password to access the database with passwords, and then you will store passwords in the database for various services, sites, and even various other important and secret data.
All passwords are encrypted with the help of your master password which is used as a key and is kept secure. The database is unusable without your master password. These applications can also generate a random password and make it easier for you to register on new internet services and sites. When using, you can also activate two-factor authentication, which will raise security to an even higher level and will require you to enter an additional code that you read from your mobile phone when logging in. Password managers are a fully efficient solution that also stores all your passwords in an encrypted database and can generate new ones, but store them on your computer, so they are not available from every device. You can also store its database on, say, a USB flash drive, and always carry all passwords with you.
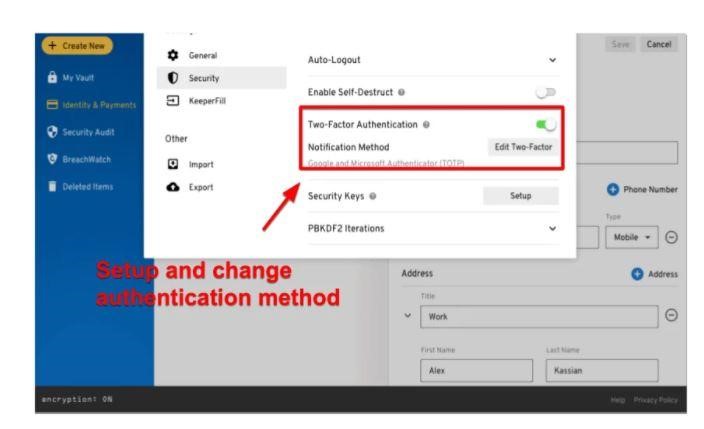
Two-Factor Authentication For Keeper Password Manager
When using certain sites with registration and login, it’s good to test the probabilities ahead and, if necessary, set alternative email addresses and ways to recover the password. just in case you forget the access parameters, you’ll request a password reset, and a link to enter a replacement password is going to be sent to the email address from the account. This email address must be always current because otherwise the email is sent to an address that you just not use and so you’d not be able to solve the matter.
Beware of phishing
The owners themselves are often answerable for revealing passwords, as they do not pay enough attention when opening the links they receive in messages. On social networks, in emails, and comments on sites, spam messages are often spread with links that result in sites that resemble the first ones but are located at a very different address. after you access them, they ask you to log in with a username and password. By entering your access data, you’re sending that data to the hacker, who founded such a fake (phishing) site.
Many internet users don’t notice that this is often a malicious site and enter their data and thus compromise their accounts. it’s important to always check the source of the message and if it seems suspicious to you, never open the links that are in it. Also, if you visit a page from suspicious messages, ensure that the net address matches the right one, before entering any data on such a site.
As you’ll see, as time goes on, the necessity for increasingly complex passwords grows. one of all the solutions is that the mentioned password managers, but it’ll be easier for us when the technology develops even more and when rather than entering the codes, we scan the thumb, fist, or cornea. These immutable and unique biometric data are often used as another thing about applications, without which access to services isn’t possible.


in my computer all file data encrypted how to solve this problem yytw