The Backdoor:Win32/Rukap.AC notification means that your system has a problem. Allowing it to keep running may end up with really bad consequences. Rukap gives the criminals an easy access to your system, or even adds it to the botnet.
Backdoors like Rukap are flexible threats that can act as autonomous malware, and be used in staged attacks. Their primary target is creating a remote access point to the infected computer, that functions without the owner’s knowledge. To avoid any interruptions, backdoor tries to stay as low as possible.
Backdoor:Win32/Rukap.AC Detection Overview
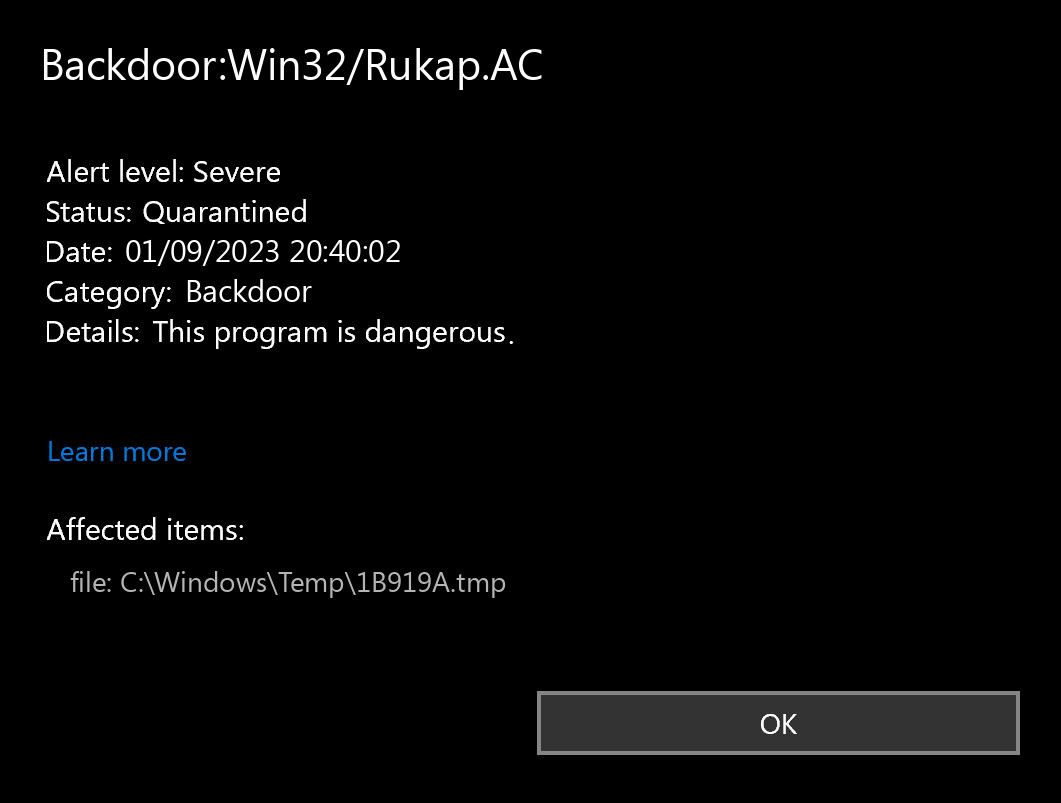
The Backdoor:Win32/Rukap.AC detection you can see in the lower right side is displayed to you by Microsoft Defender. That anti-malware application is good at scanning, but prone to be generally unreliable. It is prone to malware attacks, it has a glitchy interface and bugged malware clearing capabilities. Therefore, the pop-up which states concerning the Rukap is just a notification that Defender has actually found it. To remove it, you will likely need to make use of another anti-malware program.
Backdoor Summary:
| Name | Rukap Backdoor |
| Detection | Backdoor:Win32/Rukap.AC |
| Damage | Gain access to the operating system to perform various malicious actions. |
| Similar | Msil Eletgbot, Quiterat Malware, Imecab, Hacktool Python Remoteshell, Janelarat Malware, Double Rat Attacks, Win64 Repezor, Redsip |
| Fix Tool | See If Your System Has Been Affected by Rukap backdoor |
Shortly about backdoors
Backdoors are viruses that can obtain both separated and built-in shapes. One time you can discover that an official program from a widely known developer has a functionality that enables somebody to connect to your computer. Will it be somebody from the creators or a 3rd party – nobody knows. However, the scandal when this aspect is spotted in a legit program is nearly impossible to miss. There is additionally gossip that there is a hardware-based backdoor in Intel CPUs1.
Is Backdoor:Win32/Rukap.AC dangerous?
As I have specified previously, non-harmful malware does not exist. And Backdoor:Win32/Rukap.AC is not an exception. This backdoor does not deal a many harm exactly after it releases. However, it will be a really unpleasant surprise when a random forum or site in the Internet will not let you in, due to the fact that your IP-address is banned after the DDoS attack. However, even if it is not vital for you – is it pleasurable in any way to understand that someone else can simply access your computer, read your discussions, open your files, and spectate what you do?
The spyware that is frequently present as a supplement to the Backdoor:Win32/Rukap.AC malware will be just another reason to remove it as fast as you can. Nowadays, when users’ information is priced very high, it is too illogical to provide the criminals such a possibility. Even worse if the spyware will somehow handle to grab your financial info. Seeing 0 on your bank account is the most awful problem, in my opinion.
How did I get this virus?
It is hard to trace the sources of malware on your computer. Nowadays, things are mixed up, and spreading methods chosen by adware 5 years ago may be utilized by spyware nowadays. But if we abstract from the exact spreading way and will think of why it works, the answer will be pretty uncomplicated – low level of cybersecurity awareness. People click on promotions on odd websites, click the pop-ups they receive in their browsers, call the “Microsoft tech support” assuming that the odd banner that says about malware is true. It is very important to understand what is legit – to stay away from misunderstandings when attempting to identify a virus.
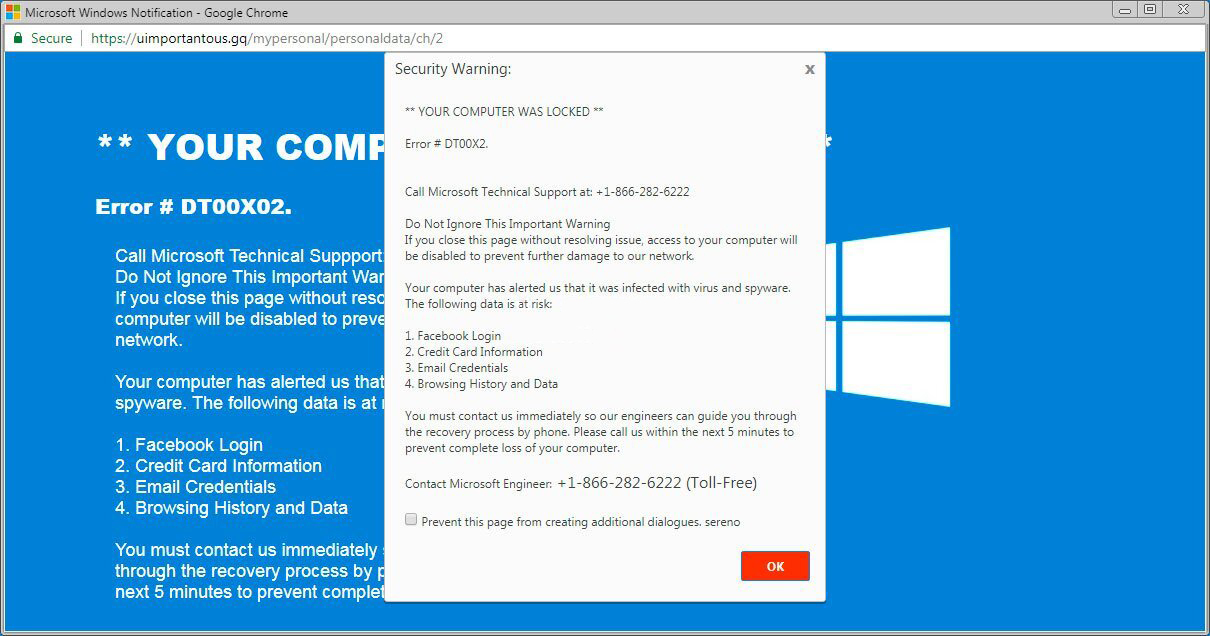
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most extensive ways of malware distribution – lure e-mails and also injection into a hacked program. While the first one is not so easy to avoid – you need to know a lot to understand a counterfeit – the 2nd one is simple to get rid of: just don’t utilize hacked applications. Torrent-trackers and other sources of “free” applications (which are, actually, paid, but with a disabled license checking) are really a giveaway point of malware. And Backdoor:Win32/Rukap.AC is simply amongst them.
References
- Gossip about the backdoor in Intel processors on Reddit.


Leave a Comment