Phishers more often fake Microsoft pages than pages of other brands. According to Akamai experts, the American IT giant outstrips Paypal, DropBox and DHL by the number of fake pages, which also took the top lines of the rating.
This data is contained in the new study of State of the Internet, which is dedicated to phishing technologies.“Phishing is a long-term problem that we expect will have adversaries continuously going after consumers and businesses alike until personalized awareness training programs and layered defense techniques are put in place”, — said Martin McKeay, Editorial Director of the State of the Internet/Security report for Akamai.
The authors highlighted the importance of phishing packs – ready-to-use solutions that allows deploying malicious pages and stealing users’ data.
The content of such packages varies from simple HTML forms to multifunctional products that can hide from defense systems and attack targets using precise targeting settings. Phishing packs can be rented – attackers deploy full-fledged Internet services with the ability to analyze and configure campaigns, monitor software updates.
In less than nine months of research, experts have discovered thousands of malicious domains that used dozens of different sets. Most often, criminals draw up landing pages for Microsoft sites – specialists saw this brand in 62 packages deployed on 3.9 thousand sites. PayPal service came in second in popularity (14 phishing packs, 1.7 sites). Next come the LinkedIn social network (6 packages, 1.6 thousand domains) and the DocuSign digital signature system (4 packages, 400 domains).
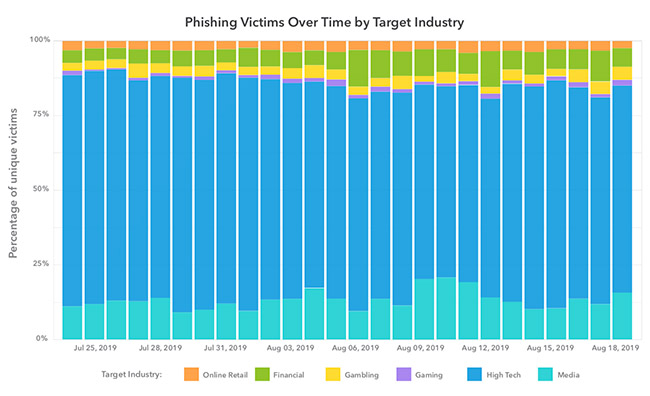
In addition to the technology sector, users of online stores, banking systems and entertainment services suffer from phishing attacks.
According to analysts, attackers have two ways – they can upload phishing packs on their own sites or embed them in other people’s web resources.
The second option helps criminals to avoid blocking for longer time. Analytical systems constantly monitor and block domains that receive complaints about unwanted activity, and new sites attract special attention. Hiding behind someone else’s site, phishers get a certain amount of time due to their positive reputation.
However, to hack an Internet resource, criminals need to find a vulnerability in its CMS or web server, and this task can be difficult. Therefore, more often phishers prefer to conduct campaigns on a variety of their own domains, which they purchase at a wholesale scale. Researchers estimate that about 90% of these addresses are blocked on the first day. The criminals have enough of this time to recoup the costs of creating a site and even get a plus. Another 5% of resources stop working within three days.
To extend the life of a malicious page, their creators check to see if the network data of the next victim is connected with information security companies and Internet corporations like Amazon or Google. Many malicious packages automatically generate URLs and other data, making blacklisting difficult.
“As the phishing landscape continues to evolve, more techniques such as BEC attacks will develop, threatening a variety of industries across the globe. The style of phishing attacks is not one size fits all; therefore, companies will need to do due diligence to stay ahead of business-minded criminals looking to abuse their trust”, — said Martin McKeay.
Why phishing attacks are dangerous and how to protect from them
As the researchers pointed out, the threats of phishing campaigns are not limited to compromising private and corporate information. Often, such an attack is only the first link in the chain of malicious actions, and criminals seek not only to resell the stolen data, but to establish long-term tracking of the victim.
Therefore, almost 80% of cases of cyber espionage in one way or another are associated with phishing activity. Authoritarian states use these methods to infect the devices of dissidents, unscrupulous companies are trying to learn the secrets of competitors. In other scenarios, a phishing incident helps hackers collect data on the infrastructure of the target organization, gain access to its partners and counterparties, and set the stage for an encryptor’s attack.
Read also: Spear phishing recognized as the fastest growing threat to businesses
Less obvious threats are related to the features of the development of phishing packs. As the researchers said, the creators of such software do not aim to avoid plagiarism as identical code sections are found in products. Thus, errors and bugs of the original phishing pack are distributed on its copies. If such a package falls into a legitimate web resource, the affected site becomes vulnerable to possible attacks.
Experts emphasize that in the current environment, user training is no longer sufficient to protect against phishing. Criminals take into account the growing digital literacy of victims and are constantly developing attack methods. In order not to suffer from their actions, companies should use specialized protective solutions that automatically block suspicious activity inside the infrastructure.


Leave a Comment