Bitdefender analysts have warned that Agent Tesla spyware has been actively used in attacks on oil and gas companies.
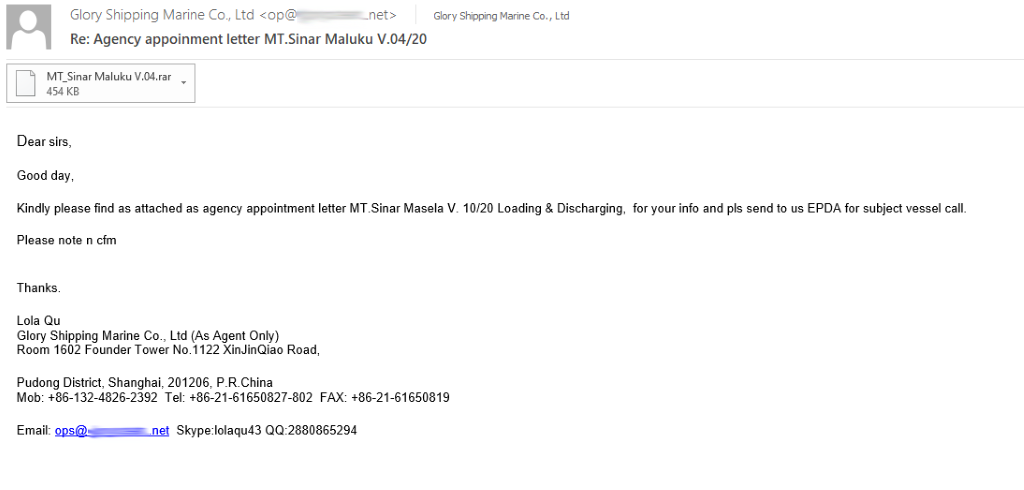
So, in one of the phishing campaigns, attackers posed themselves as the Egyptian state oil company Enppi (Engineering for Petroleum and Process Industries), and targeted their attacks on organizations in Malaysia, the United States, Iran, South Africa, Oman,Turkey and other countries.In another campaign, hackers pretended to be transport company employees and used genuine information on an oil/chemical tanker to trick their victims in the Philippines.
Interestingly, during this campaign, hackers demonstrated excellent knowledge of industry jargon, which made their letters seem real.
As part of the first campaign, attackers posed themselves as Enppi representatives to request the purchase of equipment and materials under the Rosetta Sharing Facilities project on behalf of the gas company Burullus. These emails contained attached archives, designed to deliver Agent Tesla to victims’ machines.
Having penetrated the system, the malware collected credentials and confidential information, and then transmitted it to the management server located at smtp[:]//smtp.yandex.com:87.
According to Bitdefender, the peak of attacks occurred on March 31, 2020, although the usual daily number of incidents still does not exceed five. Malaysia, the Middle East, North Africa and the United States have been mostly attacked by this campaign.
The second campaign seems to have begun around April 12, 2020, and now the target of the Agent Tesla are the logistic companies on the Philippines.
Attacks on the oil and gas industry are becoming more frequent since October 2019, and peaked in February 2020. During this time, were received more than 5,000 reports about attacks from energy companies, and analysts believe that this activity may be due to fluctuations in oil prices and the oil crisis”, – note in Bitdefender.
Researchers emphasize that this is the first time that Agent Tesla is used to attack oil and gas companies. The fact is that the infostiller itself is a completely simple solution, according to experts’ assessments. It is not difficult to get it on hacker forums and it is used by many attackers. According to a recent study, it has even become one of the most commonly used malware, associated with the COVID-19 pandemic.
Reference:
Agent Tesla is an advanced RAT, that is, a remote access trojan known to information security experts since 2014. The malicious program is written in .Net and is able to track and collect input from the victim’s keyboard, from the clipboard, take screenshots and retrieve credentials related to various programs installed on the victim’s computer (including Google Chrome, Mozilla Firefox and Microsoft Outlook). Malware can to disable anti-virus solutions and processes that try to analyze it and interfere with its work.


Leave a Comment