ZenRAT is a multifaceted threat that infiltrates computers through deceptive tactics, often masquerading as legitimate software, such as Bitwarden. This malware combines stealth with extensive data-gathering capabilities, including browser credential theft.
It employs a modular approach, potentially expanding its functionalities beyond initial capabilities. ZenRAT’s intricate infiltration methods and versatile actions make it a significant privacy and security threat. Users must remain vigilant and cautious to avoid falling victim to this potent malware.
ZenRAT Overview
ZenRAT is a Remote Access Trojan (RAT) with data-stealing capabilities that has been active since at least the summer of 2023. This malware is modular, allowing cybercriminals to add additional functionality to it, making it a versatile tool in their malicious arsenal. ZenRAT has been distributed through a fraudulent Bitwarden website, but it’s important to note that neither the website nor the RAT is affiliated with the legitimate Bitwarden service.
| Name | ZenRAT |
| Threat Type | Trojan, RAT, password-stealing virus, banking malware, spyware. |
| Similar Behavitor | Loda RAT, HiatusRAT |
| Detection | Trojan:Win32/Casdet!rfn (Microsoft) |
| Damage | Stolen passwords and banking information, identity theft, the victim’s computer added to a botnet. |
Technical Analysis
ZenRAT infiltrates systems by disguising itself as legitimate software or bundling with it. Upon infection, ZenRAT collects various device data, including hardware details, IP addresses, and installed apps. It also employs anti-analysis features to detect virtual machine environments. ZenRAT’s modular nature allows it to expand its capabilities, such as stealing browser credentials and sensitive data.
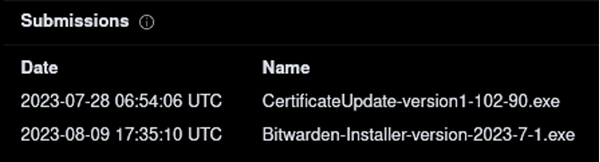
Leaked certificate used by ZenRAT to mask itself in the system
Future variants may introduce different functionalities. ZenRAT poses severe threats, including privacy breaches, financial losses, and identity theft. Users should remain vigilant to avoid infection and use reputable antivirus software.
Spreading Methords
ZenRAT is typically spread through a fake website that looks like the official website of the Bitwarden password manager. The fake website has a similar URL to the real one but has a single stray letter “i”. Suppose someone using Windows visits this website and chooses to download the software. In that case, they will get an installer that includes ZenRAT. However, suppose someone using a different operating system, such as MacOS or Linux, tries downloading the software. In that case, they will be redirected to the legitimate Bitwarden website. Thus, the fake website will display something else entirely for those not using Windows.
Another variant of ZenRAT submitted to the VirusTotal platform pretends to be Speccy, a freeware utility software for viewing data related to hardware and software present on a computer. Some ZenRAT-containing setups claim to be signed by Tim Kosse, a developer known for the FileZilla FTP program, among other software. However, the actual executables for ZenRAT can include different supposed developer details.
It is worth noting that ZenRAT could be spread using other techniques or disguises. Malicious files can come in various formats, such as archives (RAR, ZIP, etc.), executables (.exe, .run, etc.), documents (Microsoft Office, Microsoft OneNote, PDF, etc.), JavaScript, and more. Phishing and social engineering are also standard techniques used to spread malware.
The most widely used distribution methods for ZenRAT include online scams, malicious attachments or links in spam emails or messages, drive-by downloads, dubious download channels (e.g., freeware and free file-hosting sites, Peer-to-Peer sharing networks, etc.), malvertising, illegal software activation tools (“cracks”), and fake updates. Some malicious programs can self-spread via local networks and removable storage devices (e.g., USB flash drives, external hard drives, etc.). Unfortunately, unwanted applications often come bundled with viruses and spyware. These threats can steal account credentials or encrypt your documents for ransom.


Leave a Comment