What is Win32:Zorex-A [Wrm] infection?
In this short article you will certainly find concerning the interpretation of Win32:Zorex-A [Wrm] and also its adverse impact on your computer. Such ransomware are a type of malware that is elaborated by on-line scams to demand paying the ransom money by a victim.
Win32:Zorex-A [Wrm] detection overview
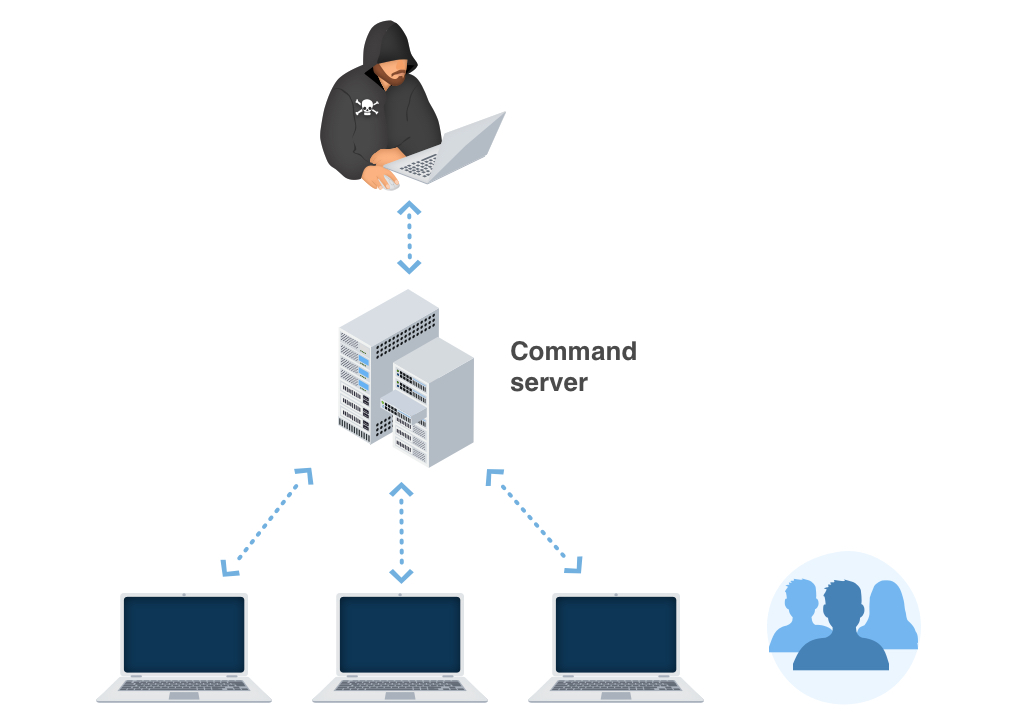
Win32:Zorex-A [Wrm] is a worm-style malware detection. The [Wrm] part matters: worm-like threats are designed to spread, copy themselves, or move through removable drives, shared folders, or network-accessible locations rather than stay as one isolated file.
The detected path tells you how urgent the cleanup is. A blocked download is different from a file found in Startup, AppData, ProgramData, a shared folder, or a removable drive. If removable media or shared folders were connected, check them before using them on another PC.
How dangerous is it?
Treat this detection as high risk until scans confirm the machine and connected storage are clean. Worm behavior can lead to repeated reinfection if a USB drive, network share, or scheduled task is left untouched. Some worm families also drop additional payloads, including stealers or remote-access components.
Could it be a false positive?
It is possible but less likely when the file is unsigned, stored in a user-writable folder, copied across drives, or detected in multiple locations. A legitimate file should have a known publisher, a clear installation path, and no reason to appear on removable media under a random name.
Symptoms worth checking
- Files or shortcuts appear on USB drives unexpectedly.
- The same detection appears in several folders.
- Unknown startup entries or scheduled tasks are created.
- Security settings, hidden-file settings, or folder options change.
- Network shares show new executable files you did not copy.
Manual verification checklist
- Write down every detected path from Windows Security or your antivirus.
- Disconnect USB drives and network shares until scanning is complete.
- Scan the system drive first, then scan removable drives separately.
- Check Startup folders, Task Scheduler, Services, and recently modified files in AppData and ProgramData.
- Enable viewing hidden files temporarily and inspect USB drives for unknown executables or shortcut files.
- Update security definitions before repeating the scan.
Removal steps
- Let the security tool quarantine detected files.
- Remove persistence entries tied to the detected folder or file name.
- Scan every removable drive before reconnecting it to another PC.
- Patch Windows and update vulnerable software that may have been abused.
- Reboot and run another full scan to confirm the worm does not reappear.
After cleanup
Do not assume the job is finished until connected drives and shared folders are also clean. If the PC was used for sensitive accounts after the infection, change passwords from a clean device. If this happened on a work network, notify the administrator so shared locations can be checked.
FAQ
Is a worm worse than a Trojan? It can be, because spread behavior increases the chance of reinfection and impact on other devices.
Can I clean only the main PC? Not if USB drives or shared folders were connected. They may carry copies.
Why does the detection come back? A startup entry, scheduled task, removable drive, or shared folder may be restoring the file.
Related guides: Kepavll Trojan detection, Seedmine coin miner, and malware removal guides.
Win32:Zorex-A [Wrm]
The most common networks whereby Win32:Zorex-A [Wrm] Ransomware Trojans are infused are:
- By ways of phishing emails;
- As a repercussion of customer ending up on a source that holds a destructive software program;
As quickly as the Trojan is effectively infused, it will certainly either cipher the data on the victim’s PC or avoid the tool from functioning in a proper way – while also positioning a ransom money note that states the demand for the victims to impact the payment for the function of decrypting the papers or recovering the file system back to the first problem. In most instances, the ransom note will certainly show up when the client reboots the PC after the system has currently been damaged.
Win32:Zorex-A [Wrm] distribution channels.
In various corners of the globe, Win32:Zorex-A [Wrm] expands by jumps as well as bounds. Nonetheless, the ransom notes as well as tricks of extorting the ransom money quantity may vary depending upon specific regional (local) settings. The ransom money notes and also tricks of obtaining the ransom money quantity might vary depending on certain local (regional) settings.
For instance:
Faulty informs regarding unlicensed software.
In particular areas, the Trojans usually wrongfully report having actually detected some unlicensed applications made it possible for on the sufferer’s tool. The sharp after that requires the user to pay the ransom.
Faulty statements about prohibited material.
In countries where software application piracy is much less popular, this technique is not as efficient for the cyber frauds. Additionally, the Win32:Zorex-A [Wrm] popup alert may wrongly declare to be stemming from a law enforcement institution and will report having located youngster porn or various other illegal information on the tool.
Win32:Zorex-A [Wrm] popup alert might incorrectly declare to be deriving from a law enforcement organization and also will certainly report having located child pornography or various other illegal data on the tool. The alert will likewise include a need for the customer to pay the ransom.
Technical details
File Info:
crc32: 86392EA0md5: 0942c0dc0996794bed2e199f77a28b59name: 0942C0DC0996794BED2E199F77A28B59.mlwsha1: e4b0d41ed4167c74e6c496e5be2171ed467040b7sha256: a3c35c617adf3dbf8953b3d5dc912bafbdb197992d3731d80106332c5303f831sha512: e72d3289ee94c9ff2b904e82b0798b069cfe7ae81e8cb4c040e670dc1ca92de57950472dbe405cae394756a6435ce1d8ff7946d60541b3786bfc87f0134b2714ssdeep: 12288:EMSApJVYG5lDLyjsb0eOzkv4R7QnvUUilQ35+6G756sM:EnsJ39LyjbJkQFMhmC+6GHtype: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
0: [No Data]
Win32:Zorex-A [Wrm] also known as:
| GridinSoft | Trojan.Ransom.Gen |
| Bkav | W32.AIDetect.malware2 |
| Elastic | malicious (high confidence) |
| Cynet | Malicious (score: 100) |
| CAT-QuickHeal | Sus.Nocivo.E0011 |
| McAfee | GenericRXOW-IL!0942C0DC0996 |
| Sangfor | Win.Malware.Delf-6899401-0 |
| CrowdStrike | win/malicious_confidence_100% (W) |
| Cybereason | malicious.ed4167 |
| Symantec | Trojan.Gen.2 |
| ESET-NOD32 | Win32/Delf.NBX |
| Zoner | Trojan.Win32.88102 |
| APEX | Malicious |
| Avast | Win32:Zorex-A [Wrm] |
| ClamAV | Win.Malware.Delf-6899401-0 |
| Kaspersky | Trojan-Ransom.Win32.Makop.d |
| Tencent | Win32.Trojan.Makop.Eyc |
| Sophos | Mal/Generic-S |
| Comodo | Heur.Corrupt.PE@1z141z3 |
| VIPRE | Worm.Win32.AutoRun |
| TrendMicro | Ransom_Makop.R035C0DFK21 |
| McAfee-GW-Edition | BehavesLike.Win32.Generic.tm |
| FireEye | Generic.mg.0942c0dc0996794b |
| SentinelOne | Static AI – Malicious PE |
| Jiangmin | Trojan.Generic.bhoqf |
| eGambit | Unsafe.AI_Score_100% |
| Microsoft | Worm:Win32/AutoRun.XXY!bit |
| ZoneAlarm | Trojan-Ransom.Win32.Makop.d |
| GData | Win32.Backdoor.Agent.AXS |
| Acronis | suspicious |
| Malwarebytes | Lamer.Virus.FileInfector.DDS |
| TrendMicro-HouseCall | Ransom_Makop.R035C0DFK21 |
| Rising | Virus.Synaptics!1.CC9C (CLASSIC) |
| Yandex | Trojan.GenAsa!ETONJRQzPLk |
| Ikarus | Worm.Win32.AutoRun |
| MaxSecure | Trojan.Malware.300983.susgen |
| Fortinet | W32/Delf.NBX |
| AVG | Win32:Zorex-A [Wrm] |
| Paloalto | generic.ml |


Leave a Comment