What is Win32/RiskWare.Chindo.Y infection?
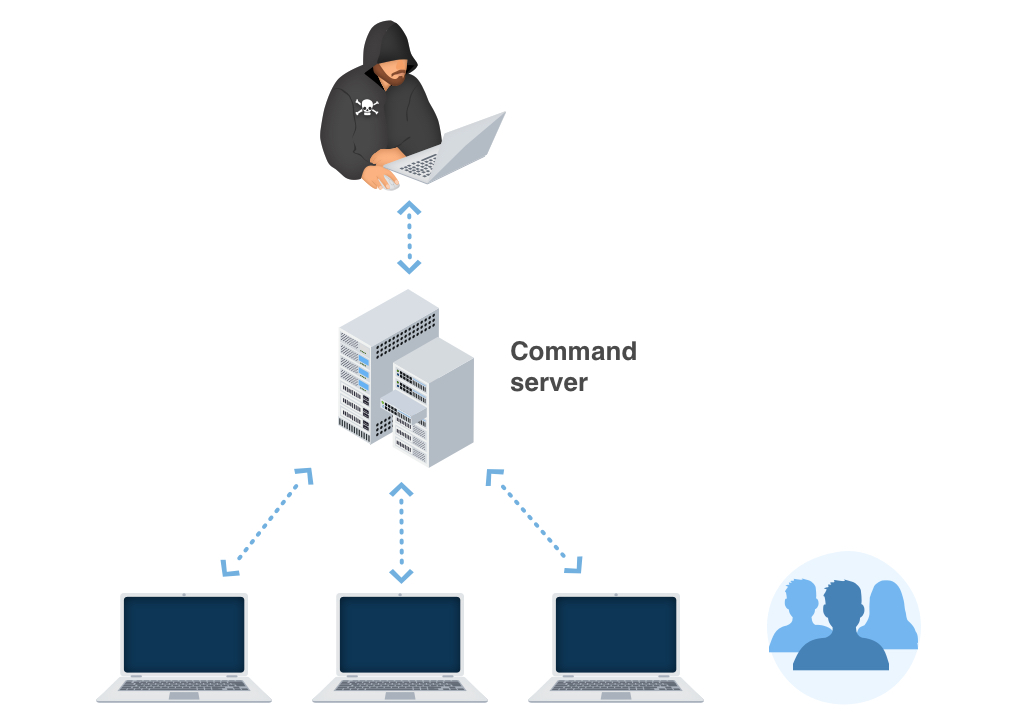
In this post you will certainly find about the interpretation of Win32/RiskWare.Chindo.Y as well as its adverse impact on your computer. Such ransomware are a type of malware that is elaborated by on the internet frauds to require paying the ransom by a sufferer.
In the majority of the cases, Win32/RiskWare.Chindo.Y ransomware will instruct its sufferers to launch funds transfer for the function of counteracting the changes that the Trojan infection has actually introduced to the target’s device.
Win32/RiskWare.Chindo.Y Summary
These modifications can be as adheres to:
- Unconventionial language used in binary resources: Chinese (Simplified);
- Installs itself for autorun at Windows startup;
- Attempts to modify proxy settings;
- Ciphering the documents found on the victim’s hard disk — so the sufferer can no longer use the data;
- Preventing normal access to the sufferer’s workstation;
Related domains:
| z.whorecord.xyz | Ransomware.Cerber.Gen |
| app.baidu2019.top | Ransomware.Cerber.Gen |
| a.tomx.xyz | Ransomware.Cerber.Gen |
Win32/RiskWare.Chindo.Y
The most common channels where Win32/RiskWare.Chindo.Y are infused are:
- By methods of phishing emails;
- As a repercussion of individual ending up on a source that organizes a destructive software;
As quickly as the Trojan is efficiently infused, it will certainly either cipher the information on the target’s computer or prevent the device from working in an appropriate manner – while likewise putting a ransom money note that states the requirement for the victims to effect the repayment for the objective of decrypting the papers or bring back the documents system back to the initial problem. In many instances, the ransom note will certainly come up when the client reboots the PC after the system has actually already been harmed.
Win32/RiskWare.Chindo.Y circulation networks.
In different corners of the globe, Win32/RiskWare.Chindo.Y expands by leaps and bounds. Nonetheless, the ransom money notes and methods of extorting the ransom money amount might vary relying on particular local (regional) setups. The ransom money notes and methods of obtaining the ransom money amount may vary depending on certain local (regional) settings.
For instance:
Faulty notifies about unlicensed software application.
In certain areas, the Trojans often wrongfully report having actually identified some unlicensed applications allowed on the victim’s device. The sharp then requires the customer to pay the ransom money.
Faulty statements regarding prohibited web content.
In countries where software program piracy is less prominent, this approach is not as efficient for the cyber frauds. Alternatively, the Win32/RiskWare.Chindo.Y popup alert may wrongly claim to be stemming from a law enforcement organization and will certainly report having situated child pornography or various other unlawful information on the gadget.
Win32/RiskWare.Chindo.Y popup alert might falsely assert to be obtaining from a regulation enforcement establishment and also will certainly report having located kid porn or various other illegal information on the device. The alert will likewise include a need for the user to pay the ransom money.
Technical details
File Info:
crc32: DDDBB16Emd5: 59fe8811d865066b4b0c30f60cdbf82cname: 59FE8811D865066B4B0C30F60CDBF82C.mlwsha1: 0cdf010dcc3e9f9766cb4a28142b5076b9bf7b6bsha256: d7728d494a960d7722d580eb660fd708ec7d82216547d29c540994099ecb14a5sha512: 032a0cb7ea06c64793b3bf20556bba6cb9f536dfdef4d5539a2f795768007e379c4353bd2f932cdbfd5fcf1509ec6cdd83efaa0731091246b5ab2135eacafda0ssdeep: 6144:x5yHlLFyMEJ6pLjevXR9qZLMoTJ4HoLb:VHpR9qfNDtype: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
0: [No Data]
Win32/RiskWare.Chindo.Y also known as:
| GridinSoft | Trojan.Ransom.Gen |
| Bkav | W32.AIDetect.malware2 |
| K7AntiVirus | Riskware ( 0055e3f21 ) |
| Lionic | Trojan.Win32.Generic.4!c |
| Elastic | malicious (high confidence) |
| DrWeb | Trojan.Baidu.1852 |
| Cylance | Unsafe |
| Alibaba | Trojan:Win32/Fsysna.0f7a2c7f |
| K7GW | Riskware ( 0055e3f21 ) |
| Cybereason | malicious.dcc3e9 |
| Symantec | ML.Attribute.HighConfidence |
| ESET-NOD32 | a variant of Win32/RiskWare.Chindo.Y |
| APEX | Malicious |
| Avast | FileRepMalware |
| Kaspersky | Trojan.Win32.Fsysna.hubp |
| NANO-Antivirus | Riskware.Win32.Chindo.enmxqo |
| Tencent | Malware.Win32.Gencirc.114b5f87 |
| BitDefenderTheta | Gen:NN.ZexaF.34170.rCW@aSyPFdbj |
| VIPRE | Trojan.Win32.Generic!BT |
| McAfee-GW-Edition | BehavesLike.Win32.Backdoor.dm |
| FireEye | Generic.mg.59fe8811d865066b |
| Webroot | Ransomware.Cerber.Gen |
| Microsoft | PUA:Win32/Presenoker |
| ZoneAlarm | Trojan.Win32.Fsysna.hubp |
| AhnLab-V3 | Malware/Gen.Generic.C1613710 |
| McAfee | Artemis!59FE8811D865 |
| MAX | malware (ai score=99) |
| Panda | Trj/GdSda.A |
| Yandex | Trojan.GenAsa!wablgeaC5dE |
| Ikarus | PUA.RiskWare.Chindo |
| MaxSecure | Trojan.Malware.300983.susgen |
| Fortinet | W32/Malicious_Behavior.VEX |
| AVG | FileRepMalware |
| Paloalto | generic.ml |
How to remove Win32/RiskWare.Chindo.Y virus?
Unwanted application has ofter come with other viruses and spyware. This threats can steal account credentials, or crypt your documents for ransom.
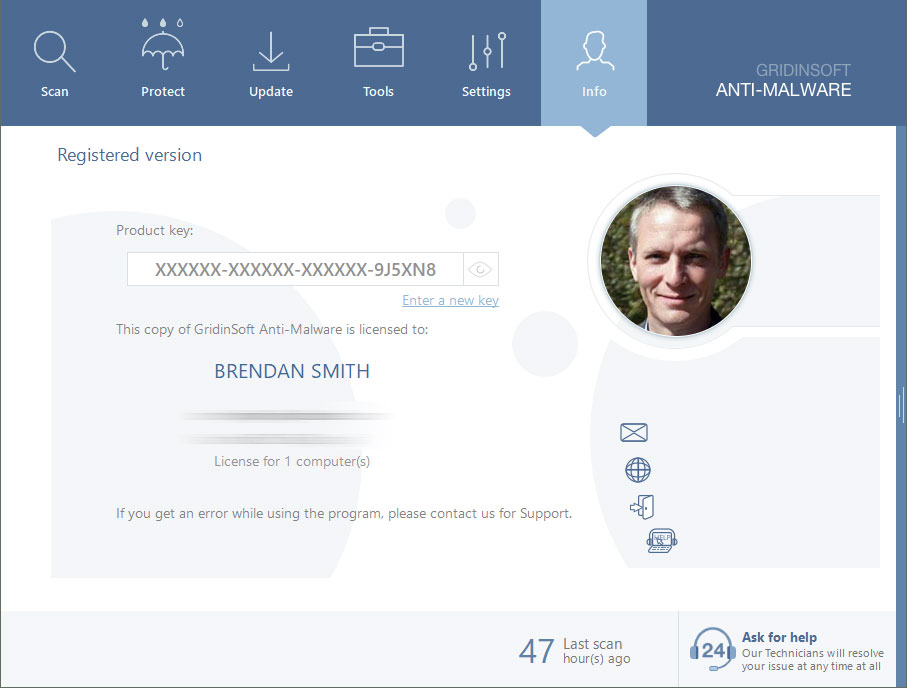
Reasons why I would recommend GridinSoft1
Run the setup file.


Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.

Click on “Clean Now”.

Are Your Protected?
If the guide doesn’t help you to remove Win32/RiskWare.Chindo.Y you can always ask me in the comments for getting help.


Leave a Comment