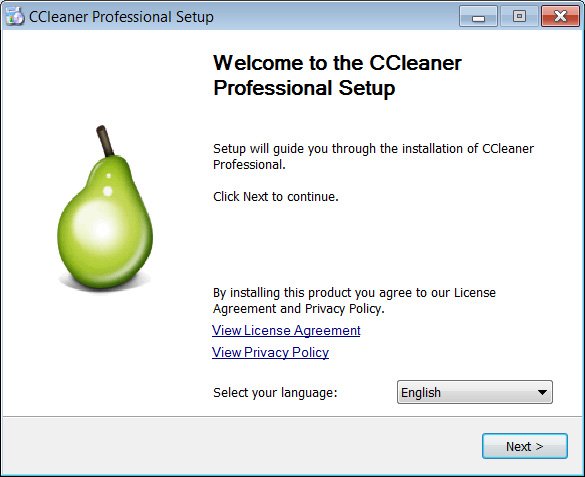
A new family of ransomware called Vovalex will spread through pirated software disguised as popular Windows utilities, such as CCleaner.
The Vovalex ransomware has a special feature that distinguishes it from other malware of this class. In terms of functionality and operating principle, Vovalex is no different from other ransomware: it encrypts the victim’s files and then leaves her with a ransom note. However, researcher Vitaly Kremets, who discovered new ransomware, revealed an interesting feature.
According to the expert, Vovalex may be the first ransomware written in the programming language D. According to the description on the official website, the creators of D (or Dlang) were inspired by C ++. However, D is also known to borrow a number of components from other languages. As a rule, cybercriminals do not use Dlang, but in this case, as Vitaly Kremets suggested, the attackers are most likely trying to bypass detection by antivirus programs.
2021-01-29: 🆕🔥#Vovalex #Ransomware … in #Dlang or 'D'|x64 ~32mb Size
Probably First Documented Ransomware Written in 'D'
Dlang Section Headers with "dmd" Compiler
1⃣._deh
2⃣.dp
3⃣.minfo
4⃣.tpXMR Monero Extortion |🤔D Likely Used to Bypass AV Detection
h/t @malwrhunterteam pic.twitter.com/XBjpsrbMLS— Vitali Kremez (@VK_Intel) January 29, 2021
The MalwareHunterTeam team was the first to stumble upon Vovalex and posted a sample of the Vovalex ransomware on VirusTotal. The guys from BleepingComputer 1 analyzed the sample and came to the conclusion that the ransomware is distributed as an illegal copy of the CCleaner utility for Windows systems. During the startup process, Vovalex opens a legitimate copy of the CCleaner installer and places its copy with an arbitrary file name in the %Temp% directory.
After that, the malware starts encrypting files on the victim’s computer by adding the .vovalex extension to them. The last step is to copy a note with the requirements to the desktop – README.VOVALEX.txt. Attackers ask for 0.5 XMR (Monero cryptocurrency) for a decoder. In dollars, this amount is approximately $69.54.
Here is a summary for the Vovalex:
| Name | Vovalex Virus |
| Contacts | [email protected] |
| Ransomware note | README.VOVALEX.txt |
| Extension | .vovalex |
| Detection | Trojan-Ransom.Vovalex (A), Ransom:Win64/Vovalex.MK!MTB, TrojanRansom.Win64.Vovalex |
| Symptoms | Your files (photos, videos, documents) have a .vovalex extension and you can’t open it. |
| Fix Tool | See If Your System Has Been Affected by Vovalex virus |
References
- Vovalex is likely the first ransomware written in D: bleepingcomputer.com
![]() German
German ![]() Japanese
Japanese ![]() Spanish
Spanish ![]() Portuguese (Brazil)
Portuguese (Brazil) ![]() French
French ![]() Turkish
Turkish ![]() Chinese (Traditional)
Chinese (Traditional) ![]() Korean
Korean ![]() Indonesian
Indonesian


Leave a Comment