Researcher and programmer David Buchanan demonstrated that Twitter images can hide up to 3MB of data, such as ZIP or mp3.
For example, user can upload images modified with steganography. That is, up to 3 MB of data can be placed inside the pictures. As it turns out, the social network does not clean up the images properly.David Buchanan has attached examples of such images to his posts, in which he hid the ZIP archive with the source code and the MP3 file (the 6 KB image below in the screenshot contains the full archive).
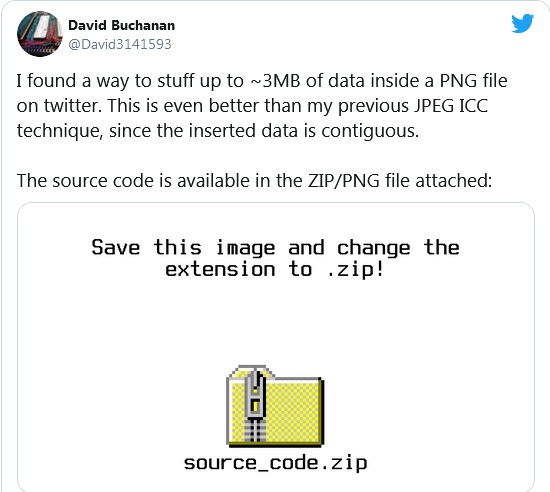
Although these PNG files posted on Twitter look like ordinary images at a glance, simply uploading and changing their extension is enough to get different content.
The image posted on the Twitter server (https://pbs.twimg.com/media/Ewo_O6zWUAAWizr?format=png&name=large) has a size of 2.5 MB and actually contains an mp3 file with the track Never Gonna Give You Up by Rick Astley.
The researcher has already published on GitHub the source code for creating such files: tweetable-polyglot-png.
The fact that Twitter is not always able to remove extraneous information from images opens up opportunities for attackers to abuse the platform. For example, a PNG file can contain malicious code that makes it easier to manage malware and is necessary for C&C needs. On the other hand, blocking image traffic from Twitter and the pbs.twimg.com domain completely could affect legitimate operations.
The researcher says that he already tried to inform Twitter developers about a similar issue with JPEG files, but then he was told that this is not a security-related bug. Therefore, Buchanan decided not to notify the company about a similar problem with PNG files.
Let me remind you that I also wrote that Attackers used Twitter API to match phones to usernames.


Leave a Comment