What is Trojan:Win32/CoinMiner!MTB?
In this post you will find regarding the meaning of Trojan:Win32/CoinMiner!MTB and its adverse influence on your computer. Such malware are a type of malware that is elaborated by on the internet scams to require paying the ransom by a sufferer.
In the majority of the situations, Trojan:Win32/CoinMiner!MTB infection will certainly advise its victims to launch funds transfer for the purpose of neutralizing the modifications that the Trojan infection has introduced to the victim’s gadget.
Trojan:Win32/CoinMiner!MTB Summary
These modifications can be as follows:
- Reads data out of its own binary image. The trick that allows the malware to read data out of your computer’s memory.
Everything you run, type, or click on your computer goes through the memory. This includes passwords, bank account numbers, emails, and other confidential information. With this vulnerability, there is the potential for a malicious program to read that data.
- Drops a binary and executes it. Trojan-Downloader installs itself to the system and waits until an Internet connection becomes available to connect to a remote server or website in order to download additional malware onto the infected computer.
- Uses Windows utilities for basic functionality;
- Attempts to disable Windows Defender;
- Uses suspicious command line tools or Windows utilities;
- Ciphering the documents found on the sufferer’s hard disk — so the target can no longer utilize the information;
- Preventing routine access to the target’s workstation. This is the typical behavior of a virus called locker. It blocks access to the computer until the victim pays the ransom.
Similar behavior
Related domains
| z.whorecord.xyz | W32/MSIL_Ransom.D.gen!Eldorado |
| a.tomx.xyz | W32/MSIL_Ransom.D.gen!Eldorado |
Trojan:Win32/CoinMiner!MTB
One of the most regular channels whereby Trojan:Win32/CoinMiner!MTB Trojans are infused are:
- By ways of phishing e-mails;
- As an effect of customer winding up on a resource that hosts a destructive software program;
Trojan:Win32/CoinMiner!MTB distribution channels.
Faulty informs regarding unlicensed software application.
In specific locations, the Trojans commonly wrongfully report having actually found some unlicensed applications allowed on the sufferer’s gadget.
Faulty declarations concerning unlawful content.
In countries where software program piracy is less popular, this technique is not as efficient for the cyber scams. Additionally, the Trojan:Win32/CoinMiner!MTB popup alert may incorrectly declare to be originating from a law enforcement organization and will report having situated kid pornography or various other unlawful data on the tool.
Trojan:Win32/CoinMiner!MTB popup alert may incorrectly assert to be acquiring from a regulation enforcement institution and will certainly report having located kid pornography or other unlawful data on the gadget.
Technical details
File Info:
crc32: F6BBDA36md5: ab0901b904ec91c70625bc93ba3a509dname: sensation.exesha1: 9310d50b123b7245916127eece4c3a9768a68046sha256: d45d0d5e2c5adfeccc6b476a651590b3f6d328593f3b0e9496e7d7afd75957d8sha512: d768cf84a0cc29221d9ff1d36300fc8afa95048161e85ebba1e779941e503fcb26ae6fffab82fa2d280add95e0515c11e05191715e9a05e1d3dbdc65ef6b5d47ssdeep: 12288:shqxSLo5C1Ps4Xh5HBxCnzT798Bx3L/Dp2+/x/HFM:sHLmCiIh5vQyFhx/HFMtype: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
0: [No Data]
Trojan:Win32/CoinMiner!MTB also known as:
| FireEye | Generic.mg.ab0901b904ec91c7 |
| CAT-QuickHeal | Trojan.WacatacFC.S12096267 |
| McAfee | Artemis!AB0901B904EC |
| Malwarebytes | Trojan.Dropper |
| Zillya | Trojan.Fsysna.Win32.19923 |
| K7AntiVirus | Trojan ( 0055e7d41 ) |
| Alibaba | Backdoor:MSIL/CoinMiner.967db111 |
| K7GW | Trojan ( 0055e7d41 ) |
| CrowdStrike | win/malicious_confidence_80% (W) |
| Symantec | Trojan.Gen.MBT |
| APEX | Malicious |
| Paloalto | generic.ml |
| GData | Win32.Trojan.Agent.VYS0M4 |
| Kaspersky | Trojan.Win32.Agent.xaeags |
| BitDefender | Gen:Variant.Razy.574046 |
| MicroWorld-eScan | Gen:Variant.Razy.574046 |
| Endgame | malicious (high confidence) |
| Comodo | Malware@#nrs45f0rv75z |
| F-Secure | Heuristic.HEUR/AGEN.1121262 |
| DrWeb | Trojan.DownLoader30.48710 |
| TrendMicro | Coinminer.MSIL.CRYSAN.SM |
| Emsisoft | Gen:Variant.Razy.574046 (B) |
| Ikarus | Trojan.BAT.KillAV |
| Cyren | W32/MSIL_Ransom.D.gen!Eldorado |
| Avira | sensationmc.exe |
| MAX | malware (ai score=84) |
| Microsoft | Trojan:Win32/CoinMiner!MTB |
| Arcabit | Trojan.Razy.D8C25E |
| ZoneAlarm | Trojan.Win32.Agent.xaeags |
| AhnLab-V3 | Malware/Win32.Coinminer.C4153441 |
| Cylance | Unsafe |
| Panda | Trj/CI.A |
| ESET-NOD32 | BAT/KillAV.NEY |
| TrendMicro-HouseCall | Coinminer.MSIL.CRYSAN.SM |
| Rising | Backdoor.MinerMon!1.BE28 (CLOUD) |
| Fortinet | BAT/KillAV.NEY!tr |
| BitDefenderTheta | Gen:NN.ZemsilF.34130.zm0@a4mWPXf |
| AVG | Script:SNH-gen [Trj] |
| Cybereason | malicious.b123b7 |
| Avast | Script:SNH-gen [Trj] |
| Qihoo-360 | HEUR/QVM10.1.629B.Malware.Gen |
How to remove Trojan:Win32/CoinMiner!MTB Virus?
Unwanted application has ofter come with other viruses and spyware. This threats can steal account credentials.
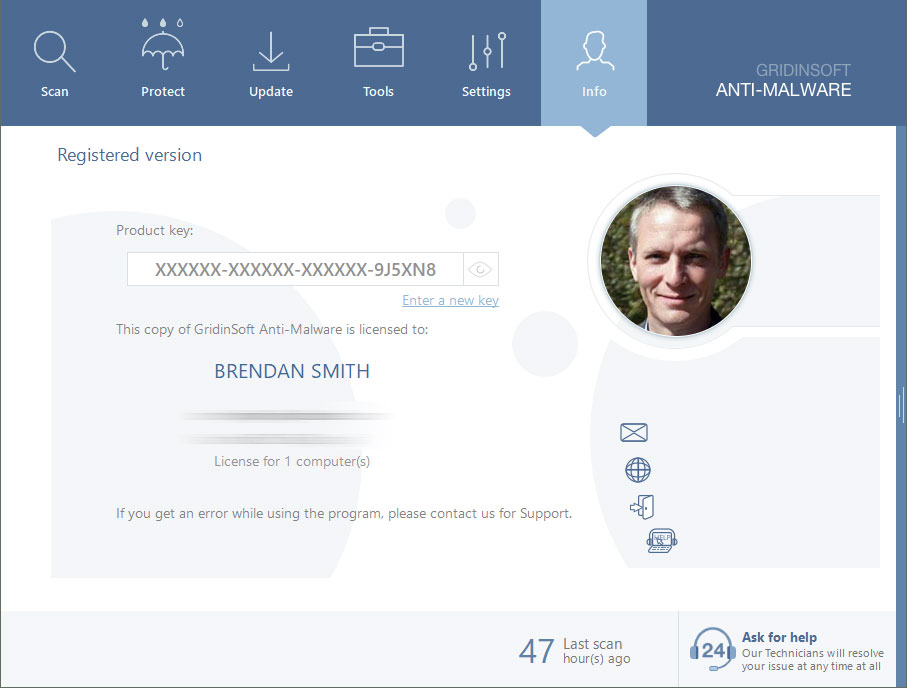
Reasons why I would recommend GridinSoft1
Run the setup file.


Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.

Click on “Clean Now”.

Are Your Protected?
If the guide doesn’t help you to remove Trojan:Win32/CoinMiner!MTB you can always ask me in the comments for getting help.


Leave a Comment