What is Agent Tesla Malware?
In this article you will locate the meaning of Trojan:Win32/AgentTesla!ml (Agent Tesla Malware) as well as its unfavorable impact on your computer. “AgentTesla ml” virus can be correctly identified as spyware that steals your credentials, information about your PC, and installed programs.
Trojan:Win32/AgentTesla!ml Summary
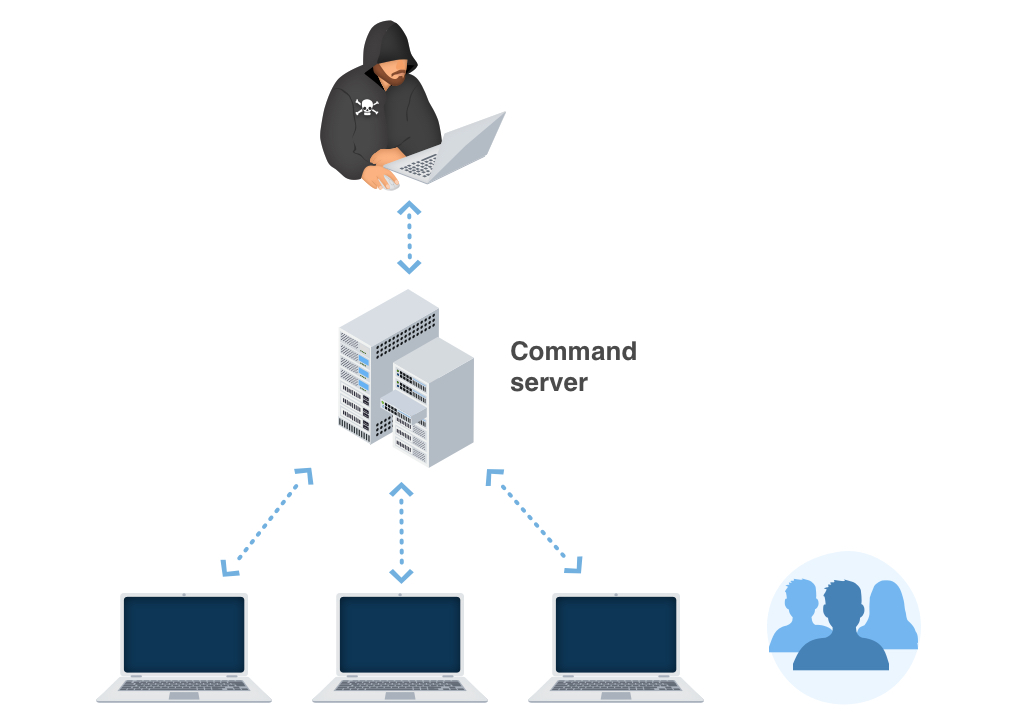
The AgentTesla ml virus can be classified as spyware. That sort of virus tracks various parts of a victim’s activity and collects sensitive data. In the future, crooks can sell that data (passwords, personal conversations, important files) on Darknet or use it to blackmail the victim. There were a lot of cases when Trojan:Win32/AgentTesla!ml was distributed together with ransomware. While the virus-crypto was doing its job, spyware collected every valuable information from the computer. If the damaged computer was connected to the network, AgentTesla!ml also tried to get the passwords of other computers in that network. In doing so, viruses can spread through the whole corporate network. Besides the usual ransom for file decryption, fraudsters will also ask you to pay to avoid publishing the information stolen by AgentTesla trojan.
As you can see, the danger of “AgentTesla ml” cannot be underestimated. People often ignore notifications from anti-malware programs, thinking there is nothing to worry about. However, a spyware hazard can touch anyone, regardless of the factors. Careful network browsing can decrease the risks of malware appearance, but anti-malware software will multiply those risks to zero.
Similar behavior
Related domains
| z.whorecord.xyz | Ransom.Wannacry |
| a.tomx.xyz | Ransom.Wannacry |
Typical ways of Trojan:Win32/AgentTesla!ml distribution
The biggest share of Trojan:Win32/Wacatac.D!ml virus distribution is after these methods:
Email spamming became a prevalent malware distribution method since the users do not raise suspicion on notifications from DHL or Amazon about the incoming delivery. However, it is pretty easy to distinguish the nasty email from the original one. One sent by cybercriminals has a strange sender address – something like [email protected]. At the same time, the actual email address has a specific domain name (@amazon.com or @dhl.us) and can also be seen on the official website in the “Contact us” tab.
Malicious advertisements on the web are an old-timer of malware distribution. The advice to stop clicking the blinking advertisements on untrustworthy websites exists as long as the ads are on the Internet. You can also install ad-blocking plugins for your web browser – they will deal with any ads. However, if they are generated by adware already present on your PC, ad blockers will be useless.
Software bundling is widespread among virus developers. Users who hack the programs to make them usable without purchasing a license approve any offer to include another program in the pack because they are gaining money in such a way. Check precisely the installation window for signs like “Advanced installation settings” or so. The ability to switch off the malware installation often hides under such items.
Trojan:Win32/AgentTesla!ml effects.
In different edges of the world, victims of the Trojan:Win32/AgentTesla!ml say about different signs of virus activity. Nonetheless, the typical sign of the fact that spyware infected your PC is that your social network accounts are stolen, and you see that
AgentTesla!ml activity is quite hard to detect. And it is not a thing you need to wonder about – viruses like this one must stay undetected to be more effective and bring more effects. All changes it does are far away from the places where the user works. Group Policies, notifications settings, registry, Task Scheduler – these parts of the operating system are visited only when something goes wrong. Users get the fact that something is wrong only after the successful virus activity.
It is quite hard to detect the changes done in the registry and Group Policies because of the huge amount of entries in these system elements. But the notifications settings, especially Task Scheduler, are elementary to control. If you see that the programs you are used to receiving notifications have stopped sending them to you or several programs added to the list, it is better to raise suspicion. The scheduler is a rare-used application, so if you had nothing scheduled and now see that something appeared in it, you must scan your system. Read the guide below.
Technical details
File Info:
crc32: 7B1738FAmd5: bc14d13f1d7d4299cb07aff24b039b07name: Ordem de Compra.exesha1: 91d3595692f85beb86cbd70f89c0327c1484d423sha256: 03f5b9544b3bb2db290e54dfe203f425374d973ac225df52a7cb29adc7998726sha512: 85081d8863bdbaf8ea7f85f9e69f0c8ea9d7aa3c6bd3f144f421b6ef86302c6ce5a6dd96e87dc95e4b4d7e581ff969c1d98854f6d0b5963d67dcfbad9edf3a47ssdeep: 12288:hjLGEbvQe+5cZO6OCAq2iNoRLgIRLu8lVY+96xZXgOCxAumyVnQWiEyJTwVdRDJ:hjt1KtL3lVYpxZXgOCxJHQttTwfNtype: PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS WindowsVersion Info:
Translation: 0x0000 0x04b0LegalCopyright: AsIaNHaWk xa9 2013Assembly Version: 3.0.0.0InternalName: NeRx.exeFileVersion: 3.0.0.0CompanyName: AsIaNHaWkx2122 CreationsLegalTrademarks: Comments: This Software is designed for Non-Commercial use, In which you can add employer's all description for generating their payslip by their name as well as id'sProductName: Payroll Management SystemProductVersion: 3.0.0.0FileDescription: PAYROLL MANAGEMENT SOFTWAREOriginalFilename: NeRx.exe
Trojan:Win32/AgentTesla!ml also known as:
| Elastic | malicious (high confidence) |
| MicroWorld-eScan | Trojan.GenericKD.44129001 |
| FireEye | Trojan.GenericKD.44129001 |
| CAT-QuickHeal | Backdoor.MSIL |
| McAfee | RDN/Generic.dx |
| Cylance | Unsafe |
| Sangfor | Malware |
| CrowdStrike | win/malicious_confidence_100% (W) |
| BitDefender | Trojan.GenericKD.44129001 |
| K7GW | Trojan ( 0052eef11 ) |
| K7AntiVirus | Trojan ( 0052eef11 ) |
| TrendMicro | TROJ_GEN.R022C0DJM20 |
| Cyren | W32/MSIL_Kryptik.BYH.gen!Eldorado |
| Symantec | Ransom.Wannacry |
| APEX | Malicious |
| Avast | Win32:PWSX-gen [Trj] |
| ClamAV | Win.Dropper.Formbook-9781805-0 |
| Kaspersky | HEUR:Backdoor.MSIL.Androm.gen |
| Alibaba | Trojan:Win32/starter.ali1000139 |
| AegisLab | Trojan.MSIL.Androm.m!c |
| Ad-Aware | Trojan.GenericKD.44129001 |
| Emsisoft | Trojan.GenericKD.44129001 (B) |
| Comodo | Malware@#15oyehidxjvow |
| F-Secure | Trojan.TR/AD.Swotter.ugxgd |
| DrWeb | Trojan.PackedNET.424 |
| VIPRE | Trojan.Win32.Generic!BT |
| Invincea | Mal/Generic-R + Troj/Kryptik-MA |
| McAfee-GW-Edition | RDN/Generic.dx |
| Sophos | Troj/Kryptik-MA |
| Jiangmin | Backdoor.MSIL.duhx |
| MaxSecure | Trojan.Malware.300983.susgen |
| Avira | TR/AD.Swotter.ugxgd |
| MAX | malware (ai score=84) |
| Antiy-AVL | Trojan/Win32.Formbook |
| Microsoft | Trojan:Win32/AgentTesla!ml |
| Arcabit | Trojan.Generic.D2A15AE9 |
| ZoneAlarm | HEUR:Backdoor.MSIL.Androm.gen |
| GData | Trojan.GenericKD.44129001 |
| Cynet | Malicious (score: 90) |
| AhnLab-V3 | Trojan/Win32.RL_AgentTesla.C4207999 |
| BitDefenderTheta | Gen:NN.ZemsilF.34590.Zm0@aGNFkJe |
| ALYac | Trojan.Agent.FormBook |
| Malwarebytes | Trojan.Injector |
| Panda | Trj/GdSda.A |
| Zoner | Trojan.Win32.96428 |
| ESET-NOD32 | Win32/Formbook.AA |
| TrendMicro-HouseCall | TROJ_GEN.R022C0DJM20 |
| Yandex | Trojan.Igent.bUE6WP.18 |
| Ikarus | Trojan.MSIL.Inject |
| eGambit | Unsafe.AI_Score_66% |
| Fortinet | MSIL/Kryptik.YHG!tr |
| AVG | Win32:PWSX-gen [Trj] |
| Paloalto | generic.ml |
| Qihoo-360 | Generic/Backdoor.9cf |
How to remove AgentTesla!ml virus?
Unwanted applications has often come with other viruses and spyware. This threat can steal account credentials or crypt your documents for ransom.
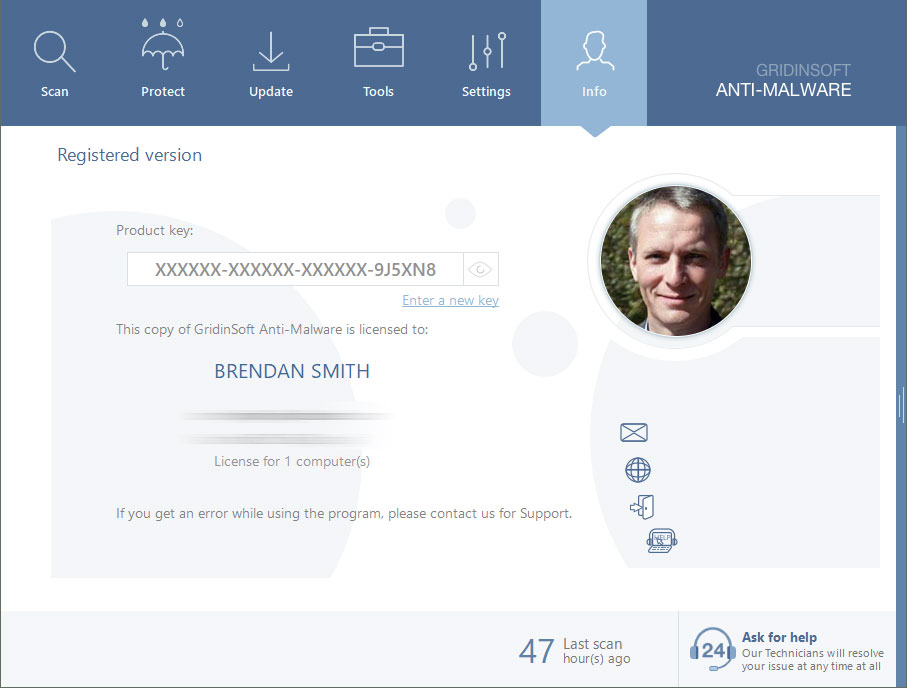
Reasons why I would recommend GridinSoft1
Run the setup file.


Press the “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.

Click on “Clean Now”.

Are Your Protected?
If the guide doesn’t help you remove AgentTesla ml, you can always ask me in the comments for help.


duh
Is this really the virus Gridinsoft finds?
Yes, yes…it is.