Trojan IRC/Backdoor.sd is a detection that scammers use in the web browser scam. They display a McAfee scan page on the website, claiming that your system has several dangerous viruses. In reality, their intention is solely to coerce you into purchasing the McAfee license.
Most frequently, the page containing the fake McAfee scam featuring the Win32Hoax.Renos.HX detection is a result of adware activity. This page often obstructs any input from you, compelling you to engage with its contents. The interaction there is quite limited – the primary goal of the scammers is to make you buy the McAfee antivirus license.
Trojan IRC/Backdoor.sd Overview
The Trojan IRC/Backdoor.sd detection you can see in the lower right side is shown to you by Microsoft Defender. That anti-malware application is quite OK at scanning, but prone to be mainly unreliable. It is defenseless to malware attacks, it has a glitchy interface and problematic malware removal capabilities. Thus, the pop-up which says about the IRC/Backdoor is simply an alert that Defender has actually found it. To remove it, you will likely need to make use of another anti-malware program.
The adware inducing the display of this fraudulent page is exceptionally malicious. This malware deluges you with an excessive number of advertisements. Have you ever encountered doorway sites? They’re rife with nothing but incessant banners – incessantly blinking, shoddily designed, and bearing peculiar information. Adware subjects every site you access to the same treatment. This malware cunningly generates revenue for its developers. You view the banners – they reap profits. Furthermore, these banners frequently harbor deceitful and explicit content. Penis enlargement solicitations, advertisements for pornography sites, and offers to acquire an iPhone for $50 – all these are par for the course with adware.
Threat Summary:
| Name | McAfee Fake Scan Results |
| Cause | Adware activity |
| Other symptoms | Display advertisements in the browser, which are not related to the sites the affected users are visiting. |
| Damage | Scam forces you to buy a license for McAfee |
| Similar | Wodpw Co In, Gleemsub Notification Removal, 2lovers Online Notification, Sisbeensaw.live Notification, Stormhammer Top Notification, Curvyalpaca Cc Ads, News Gesoxu Ads, Alukizeiasnin Popup |
| Fix Tool | See If Your System Has Been Affected by Look2me adware |
Is Trojan IRC/Backdoor.sd dangerous?
Adware like one that causes the appearance of Trojan IRC/Backdoor.sd is not something contrasty, compared to other advertising malware. However, as it was mentioned, the banners it reveals to you are quite often full of fraudulent content. Even if you can identify fraud from adware – do you really like looking at ads for free? Specifically ones that cover your web browser window and disturb you from your working process? It seems that we already know the reply.
How did I get this virus?
It is difficult to line the origins of malware on your PC. Nowadays, things are mixed, and distribution ways chosen by adware 5 years ago can be utilized by spyware nowadays. However, if we abstract from the exact distribution tactic and will think about why it works, the explanation will be really uncomplicated – low level of cybersecurity awareness. People press on ads on odd sites, open the pop-ups they receive in their web browsers, call the “Microsoft tech support” assuming that the weird banner that says about malware is true. It is necessary to know what is legitimate – to avoid misconceptions when trying to identify a virus.
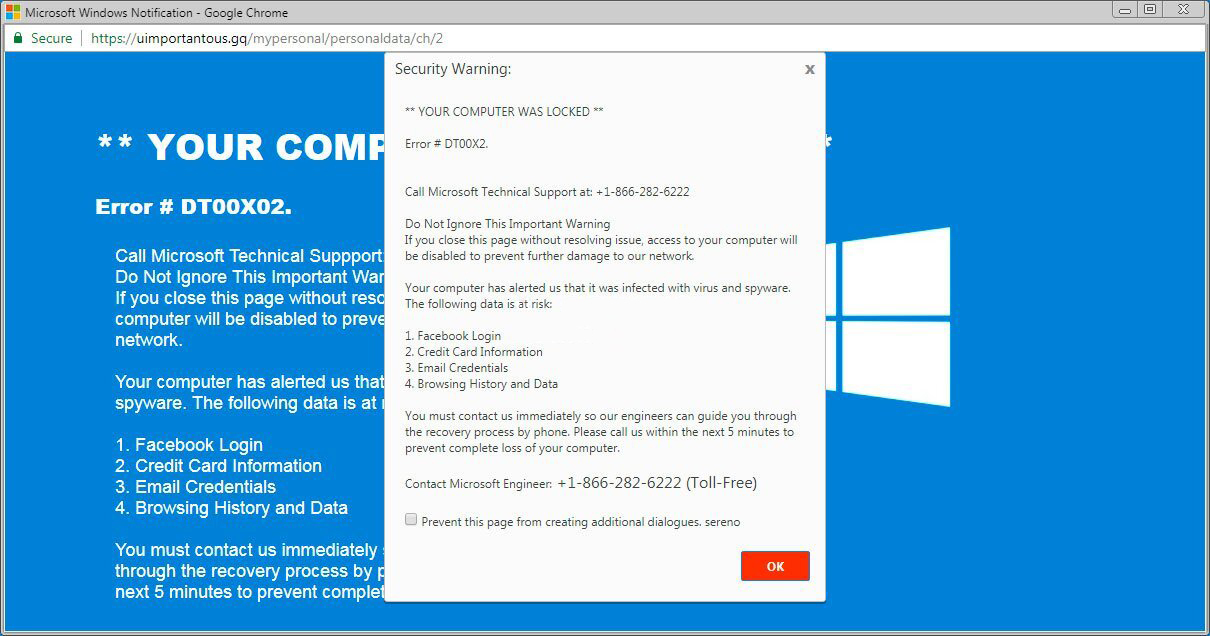
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most widespread ways of malware distribution – lure emails and also injection into a hacked program. While the first one is not so easy to stay away from – you must know a lot to understand a fake – the 2nd one is very easy to solve: just don’t utilize hacked programs. Torrent-trackers and other providers of “free” applications (which are, actually, paid, but with a disabled license checking) are really a giveaway point of malware.
References
- Official Microsoft guide for hosts file reset.



Leave a Comment