TCA.exe process is a Trojan Coin Miner that utilizes the contaminated computer system’s resources to mine digital money without your permission. It can be Monero, Bitcoin, DarkCoin or Ethereum.
About “TCA.exe”
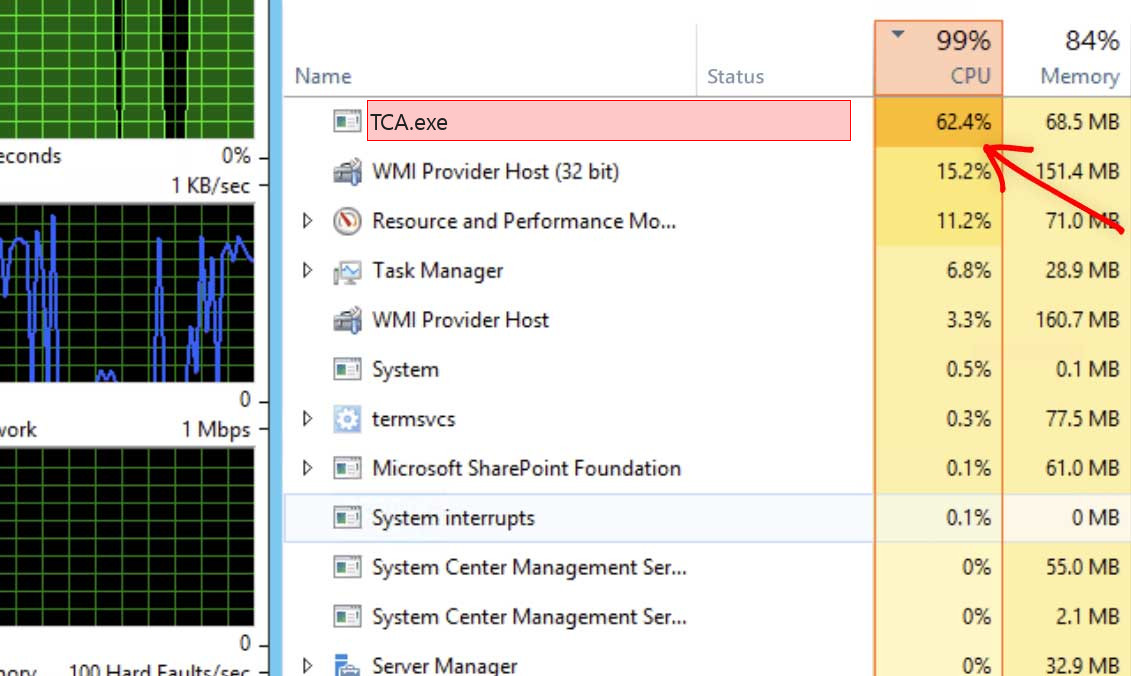
TCA.exe will certainly utilize greater than 70% of your CPU’s power and also graphics cards sources
What this indicates, is that when the miners are running you will discover that your computer system is running slower and video games are stuttering or freezing since the TCA.exe is utilizing your computer’s resources to generate income on their own. This will cause your CPU to perform at really hot temperature levels for extended time periods, which could reduce the life of the CPU.
TCA.exe Technical Summary.
| File Name | TCA.exe |
| Type | Trojan Coin Miner |
| Detection Name | Trojan:Win32/CoinMiner |
| Distribution Method | Software bundling, Intrusive advertisement, redirects to shady sites etc. |
| Similar behavior | Oddbse32, Mipony, Hostdrv32 |
| Removal | Download and install GridinSoft Anti-Malware for automatic TCA.exe removal. |
Besides decreasing your computer, running at peek degree for long times may trigger damages to your maker as well as increase electrical energy expenses.
When a computer is infected with TCA.exe trojan, usual symptoms consist of:
- Very high CPU and also graphics cards use
- Windows lessen and also make best use of gradually, and also programs run slower.
- Programs don’t release as rapidly.
- General slowness when using the PC.
How to detect TCA.exe Coin Miner Trojan?
Unlike ransomware, cryptocurrencies extracting threats are not interfering and also are more likely to continue to be unnoticed by the target.
This signs and symptom alone doesn’t inform the victim what the specific issue is. The user can experience similar problems for a range of factors. Still, TCA.exe malware can be really disruptive since it will hog all readily available computing power and also the sudden change in the means the infected device executes is most likely to make the target try to find services. If the equipment of the affected gadget is effective enough, and the victim does not spot and also get rid of the threat rapidly, the power usage and subsequently the electrical power costs will certainly go up visibly as well.
How to Remove TCA.exe Malware?
Once the target has identified that their trouble is TCA.exe risk, for the common user there are a number of options.
Additionally, if the infected machine doesn’t have essential data or the target has actually supported such data in a clean area, and also the individual has some experience, formatting the hard disk drives might function. This solution may not suffice if the infection has actually penetrated several networks the maker is a part of.
Download Removal Tool.
Reasons why I would recommend GridinSoft1
Run the setup file.


Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.

Click on “Clean Now”.



Leave a Comment