The Shadow virus falls within the ransomware type of infection. Malware of such sort encrypts all user’s data on the computer (images, documents, excel tables, music, videos, etc) and appends its own extension to every file, leaving the readme.txt text files in each folder with the encrypted files.
Shadow virus: what is known so far?
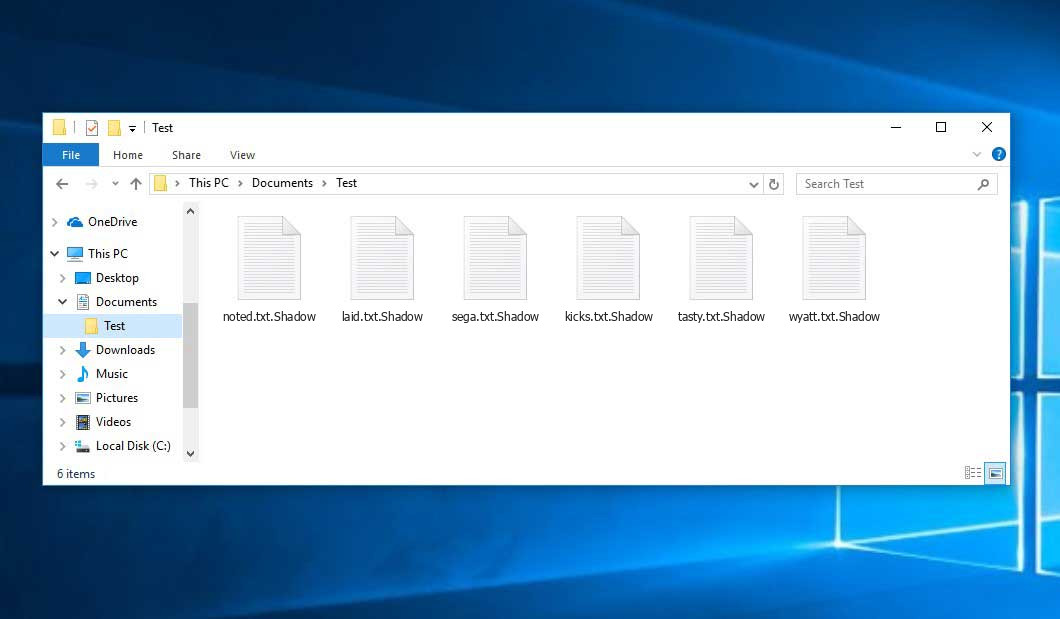
Shadow will add its extra .Shadow extension to every file’s title. For instance, an image entitled “photo.jpg” will be changed to “photo.jpg.Shadow”. In the same manner, the Excel sheet with the name “table.xlsx” will be changed to “table.xlsx.Shadow”, and so forth.
In every folder that contains the encoded files, a readme.txt file will appear. It is a ransom money memo. It contains information about the ways of paying the ransom and some other information. The ransom note most probably contains a description of how to purchase the decryption tool from the tamperers. You can get this decryptor after contacting [email protected], [email protected] via email. That is how they do it.
Shadow Overview:
| Name | Shadow Virus |
| Extension | .Shadow |
| Ransomware note | readme.txt |
| Ransom | $1000 |
| Contact | [email protected], [email protected] |
| Detection | Trojan:Win32/Tnega!MSR Removal, Win32:Adware-DNA [Adw] Virus Removal, Win32:Secat [Trj] Virus Removal |
| Symptoms | Your files (photos, videos, documents) get a .Shadow extension and you can’t open them. |
| Fix Tool | See If Your System Has Been Affected by Shadow virus |
The readme.txt document accompanying the Shadow ransomware provides the following dispiriting information:
ATTENTION! All files on your computer have been seized. All your files have been encrypted and become inaccessible. You must contact us to recover your files. Payment Method: Bitcoin Wallet Address: It will be sent via e-mail and the sent wallet number will be active for 60 minutes. The second wallet number will not be sent. Please note that if you do not pay before the expiration date, your files will be permanently deleted. For any questions or further information you can contact us at the following email address: Email: [email protected] Duration: 72 hours Refund amount: $1000 (#Thousand$#) If you do not receive a response within more than 6 hours, please check your spam folder or write to another e-mail address below. Email: [email protected] There is no alternative solution to recover your files before paying. After sending the specified amount to the specified Bitcoin address, you will receive a decryption program for your files via email. - How will I trust you? + Send us an encrypted junk file to wetransfer.com and we will send it to you decrypted. This process will be done to prove that your files can be decrypted. The file you send must be junk, otherwise we will not decrypt your password. Personel ID: - DİKKAT! Bilgisayarınızdaki tüm dosyalara el konuldu.Tüm dosyalarınız şifrelendi ve erişilemez hale geldi.Dosyalarınızı kurtarmak için bizimle iletişime geçmelisiniz. Ödeme Yöntemi: Bitcoin Cüzdan Adresi: E - posta yoluyla gönderilecek ve gönderilen cüzdan numarası 60 dakika boyunca aktif olacaktır. İkinci cüzdan numarası gönderilmeyecektir. Son kullanma tarihinden önce ödeme yapmazsanız dosyalarınızın kalıcı olarak silineceğini lütfen unutmayın. Herhangi bir sorunuz veya daha fazla bilgi için aşağıdaki e-posta adresinden bizimle iletişime geçebilirsiniz: E - posta: [email protected] Süre: 72 saat Geri ödeme tutarı: 1000 $ (#Bin$#) 6 saatten daha uzun bir süre içinde yanıt alamazsanız lütfen spam klasörünüzü kontrol edin veya aşağıdaki başka mail adresine yazın. Email: [email protected] Ödeme yapmadan önce dosyalarınızı kurtarmanın alternatif bir çözümü yoktur. Belirtilen miktarı belirtilen Bitcoin adresine gönderdikten sonra, e-posta yoluyla dosyalarınız için bir şifre çözme programı alacaksınız. - Sana nasıl güveneceğim? + Wetransfer.com\'a şifreli bir önemsiz dosya gönderin, biz de size şifresi çözülmüş olarak gönderelim. Bu işlem dosyalarınızın şifresinin çözülebileceğini kanıtlamak için yapılacaktır. Göndereceğiniz dosya önemsiz olmalıdır, aksi takdirde şifrenizin şifresini çözemeyiz. Personel ID: -
In the image below, you can see what a directory with files encrypted by the Shadow looks like. Each filename has the “.Shadow” extension added to it.
How did my computer get infected with Shadow ransomware?
There is a huge number of possible ways of ransomware injection.
Nowadays, there are three most popular methods for malefactors to have the Shadow virus settled in your digital environment. These are email spam, Trojan infiltration and peer networks.
- Another option for ransom hunters is a Trojan horse model. A Trojan is an object that gets into your machine disguised as something legal. For example, you download an installer of some program you want or an update for some program. However, what is unboxed turns out to be a harmful agent that encodes your data. Since the installation wizard can have any name and any icon, you have to make sure that you can trust the resource of the stuff you’re downloading. The best thing is to trust the software developers’ official websites.
- As for the peer-to-peer networks like torrents or eMule, the danger is that they are even more trust-based than the rest of the Internet. You can never guess what you download until you get it. Our suggestion is that you use trustworthy websites. Also, it is a good idea to scan the folder containing the downloaded items with the antivirus as soon as the downloading is done.
How do I get rid of ransomware?
It is important to note that besides encrypting your files, the Shadow virus will probably install Vidar Stealer on your PC to get access to credentials to various accounts (including cryptocurrency wallets). The mentioned program can extract your logins and passwords from your browser’s auto-filling cardfile.
How do I avert ransomware injection?
Shadow ransomware has no superpower, neither does any similar malware.
You can armour your computer from its attack within three easy steps:
- Ignore any letters from unknown mailers with strange addresses, or with content that has nothing to do with something you are waiting for (can you win in a lottery without even taking part in it?). If the email subject is more or less something you are waiting for, scrutinize all elements of the suspicious email with caution. A hoax email will surely contain a mistake.
- Avoid using cracked or unknown programs. Trojan viruses are often spreaded as a part of cracked software, most likely under the guise of “patch” preventing the license check. Understandably, untrusted programs are very hard to distinguish from trustworthy software, as trojans sometimes have the functionality you seek. Try to find information about this program on the anti-malware forums, but the best way is not to use such programs at all.
Frequently Asked Questions
🤔 How can I open “.Shadow” files?Are the “.Shadow” files accessible?
Unfortunately, no. You need to decipher the “.Shadow” files first. Then you will be able to open them.
🤔 What should I do to make my files accessible as fast as possible?
If the “.Shadow” files contain some really important information, then you probably have them backed up. In case you haven’t, there is still a chance that you do have a Restore Point from some time ago to roll back the whole system to the moment when it had no virus yet, but already had your files. The rest of the methods require patience.
🤔 What should I do if the Shadow malware has blocked my computer and I can’t get the activation key.
🤔 And what should I do now?
Many of the encrypted files might still be at your disposal
- If you sent or received your critical files through email, you could still download them from your online mailbox.
- You might have shared photographs or videos with your friends or family members. Just ask them to post those images back to you.
- If you have initially got any of your files from the Web, you can try doing it again.
- Your messengers, social media pages, and cloud storage might have all those files too.
- It might be that you still have the needed files on your old PC, a notebook, mobile, external storage, etc.
USEFUL TIP: You can employ file recovery utilities1 to retrieve your lost information since ransomware encodes the copies of your files, removing the original ones. In the tutorial below, you can see how to recover your files with PhotoRec, but be advised: you won’t be able to do it before you remove the ransomware itself with an antivirus program.
I need your help to share this article.
It is your turn to help other people. I have written this guide to help users like you. You can use the buttons below to share this on your favorite social media Facebook, Twitter, or Reddit.
Brendan SmithReferences
- Here’s the list of Top 10 Data Recovery Software Of 2024.


Leave a Comment