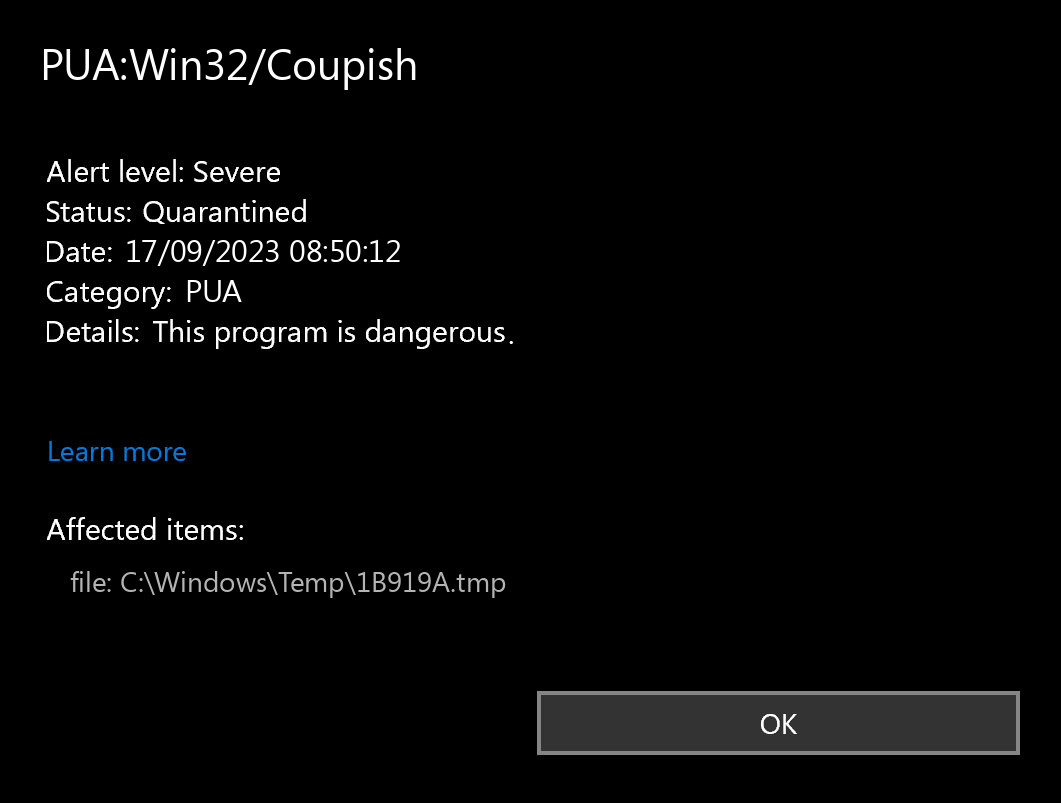
The PUA:Win32/Coupish detection means that your PC has a problem. Giving it a go may lead to some really bad consequences. Unwanted apps are not as outright dangerous as regular viruses, but is still able to create a mess in your system.
Coupish unwanted program can not be called full-size malware. Nonetheless, it has a lot of signals to state that you will not be pleased with the changes this thing brings to your PC. PUAs like that may be just a bothersome thing, either create a severe effect on your system’s performance. Additionally, there are a number of incidents when users report that this program collects user information or other sensitive stuff.
PUA:Win32/Coupish Detection Overview
The PUA:Win32/Coupish detection you can see in the lower right corner is demonstrated to you by Microsoft Defender. That anti-malware application is good at scanning, however, prone to be basically unstable. It is vulnerable to malware attacks, it has a glitchy user interface and problematic malware clearing capabilities. Hence, the pop-up which states about the Coupish is simply an alert that Defender has actually spotted it. To remove it, you will likely need to make use of a separate anti-malware program.
PUA:Win32/Coupish unwanted program is a case in point of PUA, which are quite widespread nowadays. Being free to use, it can offer you “the extended capabilities” for the extra payment. Some instances of this program type can have no useful functionality whatsoever – only the shell with the colorful interface. You can see it promoted as a system optimization tool, driver updater or torrent downloadings tracker. This or another way it does not provide you any kind of actual performance, exposing you to risk instead.
Unwanted Program Summary:
| Name | Coupish PUA |
| Detection | PUA:Win32/Coupish |
| Damage | Coupish is at least useless, or can perform various malicious actions on your PC. |
| Fix Tool | See If Your System Has Been Affected by Coupish exploit |
Is PUA:Win32/Coupish dangerous?
I have actually stated that PUA:Win32/Coupish PUA is not as trustworthy as it claims to be. The “legitimate and helpful” program may abruptly uncover itself as a downloader trojan, spyware, backdoor, or coin miner malware. And you can never figure out what to anticipate even from separate variants of Coupish unwanted program. That still does not mean that you need to panic – possibly, this nasty thing has not succeeded to do bad things to your computer.
The particular damage to your system may be triggered not just because of the malware injection. A considerable share of suspicious programs, like the Coupish app is, is just improperly developed. Possibly, their actions are rather useful than worthless if done on specific system setups, but not on each one. That’s how a simple system optimization app can cause mayhem with continuous BSODs on your system. Any interruptions to the system registry are unsafe, and they are much more dangerous if done with such programs.
How did I get this virus?
It is not easy to trace the origins of malware on your PC. Nowadays, things are mixed, and spreading tactics used by adware 5 years ago may be utilized by spyware these days. However, if we abstract from the exact distribution method and will think of why it has success, the reply will be really uncomplicated – low level of cybersecurity knowledge. Individuals click on advertisements on odd sites, open the pop-ups they get in their browsers, call the “Microsoft tech support” believing that the weird banner that says about malware is true. It is very important to understand what is legitimate – to stay away from misconceptions when trying to figure out a virus.
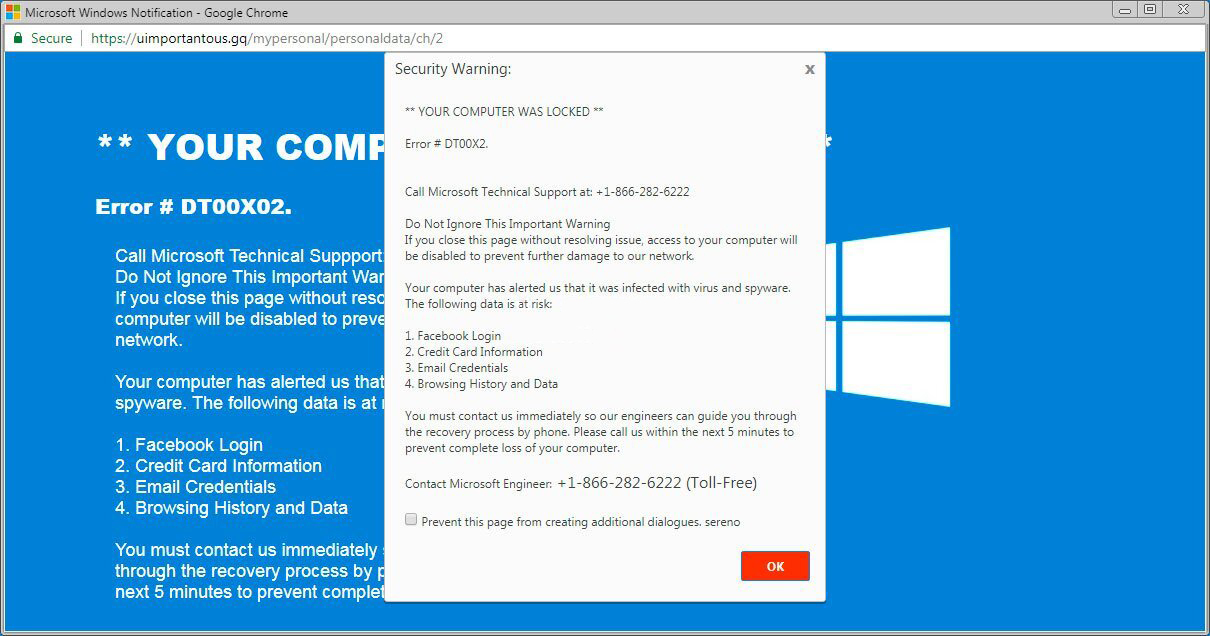
The example of Microsoft Tech support scam banner
Nowadays, there are two of the most widespread ways of malware spreading – bait e-mails and injection into a hacked program. While the first one is not so easy to stay away from – you need to know a lot to recognize a counterfeit – the 2nd one is very easy to solve: just do not utilize hacked applications. Torrent-trackers and various other providers of “totally free” applications (which are, in fact, paid, but with a disabled license checking) are just a giveaway place of malware. And PUA:Win32/Coupish is just one of them.


Leave a Comment