The Payuranson virus falls under the Skynet ransomware family. Malware of this type encrypts all the data on your computer (photos, text files, excel sheets, audio files, videos, etc) and adds its extra extension to every file, creating the SkynetData.txt text files in every directory which contains the encrypted files.
What is Payuranson virus?
☝️ Payuranson is a Skynet family ransomware-type infection.
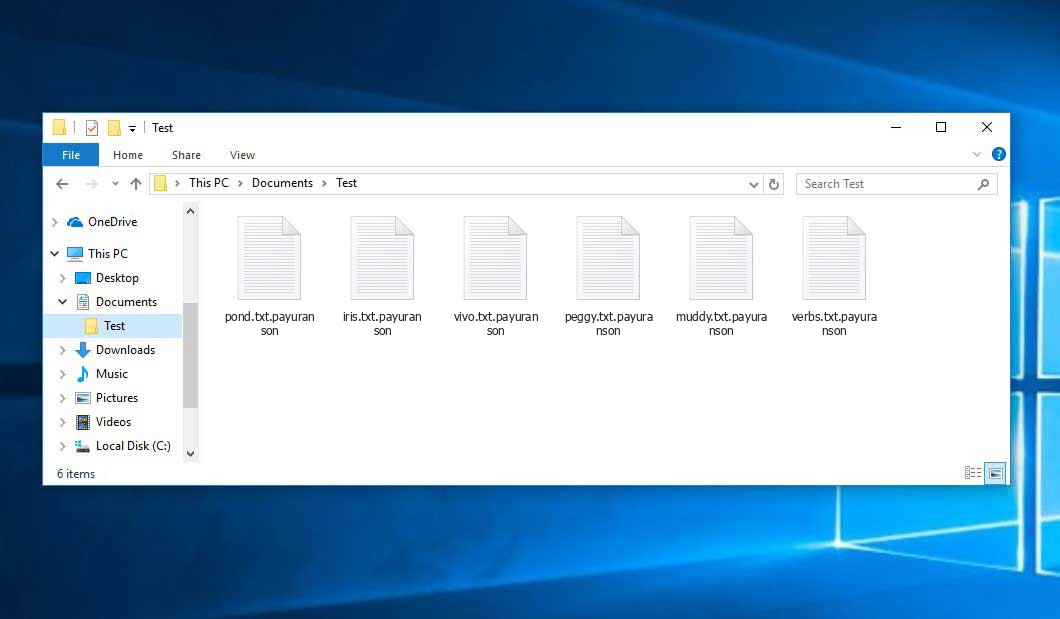
Payuranson adds its specific .payuranson extension to the title of each encoded file. For example, a file entitled “photo.jpg” will be renamed to “photo.jpg.payuranson”. Likewise, the Excel sheet named “table.xlsx” will be changed to “table.xlsx.payuranson”, and so on.
In every directory with the encrypted files, a SkynetData.txt file will be created. It is a ransom money memo. It contains information on the ways of paying the ransom and some other information. The ransom note usually contains instructions on how to buy the decryption tool from the tamperers. You can get this decoding tool after contacting [email protected] via email. That is how they do it.
Payuranson Overview:
| Name | Payuranson Virus |
| Ransomware family1 | Skynet ransomware |
| Extension | .payuranson |
| Ransomware note | SkynetData.txt |
| Ransom | $130 |
| Contact | [email protected] |
| Detection | Trojan:Win32/Vundo.OL Virus Removal, Trojan:Win32/Coroxy.SA Virus Removal, Trojan:Win32/Stealerc.AMBH!MTB Virus Removal |
| Symptoms | Your files (photos, videos, documents) have a .payuranson extension and you can’t open them. |
| Fix Tool | See If Your System Has Been Affected by Payuranson virus |
The SkynetData.txt file accompanying the Payuranson malware provides the following frustrating information:
------------------------ ALL YOUR FILES ARE ENCRYPTED ------------------------ ----> Оставайтесь сосредоточенными. <---- Все ваши файлы зашифрованы Ваш компьютер заражен вирусом-вымогателем. Ваши файлы зашифрованы, и вы не будете сможете расшифровать их без нашей помощи. Что я могу сделать, чтобы восстановить файлы? Вы можете купить наше программное обеспечение для дешифрования, это программное обеспечение позволит вам восстановить все ваши данные и удалить программы-вымогатели с вашего компьютера. Цена программного обеспечения составляет 130 долларов США (0,0027 BTC). может быть произведена только в биткойнах. Как оплатить, где я могу получить биткойны? Покупка биткойнов варьируется от страны к стране, лучше всего выполнить быстрый поиск в Google. Сами узнайте, как купить биткойн. Многие из наших клиентов отмечают, что эти сайты работают быстро и надежно: Коинмама — hxxps://www.coinmama.com Битпанда — hxxps://www.bitpanda.com BTC : 19DpJAWr6NCVT2oAnWieozQPsRK7Bj83r4 ETH : 0x55069B5317529E07ccABAaA5AaE22a9bfa1C3E12 Для подтверждения покупки свяжитесь с администратором по электронной почте или в Telegram: Электронная почта — [email protected] ТЛГ - @payurransom ---------------------------------------------- ----> Stay focused. <---- All your files have been encrypted Your computer has been infected with a ransomware virus. Your files have been encrypted and you won\'t be be able to decipher them without our help. What can I do to recover my files? You can buy our decryption software, this software will allow you to recover all your data and delete the ransomware from your computer. The price of the software is $130 (0.0027 BTC). Payment can only be made in Bitcoin. How to pay, where can I get Bitcoin? Buying Bitcoin varies from country to country, it\'s best to do a quick Google search. Yourself to find out how to buy Bitcoin. Many of our customers have reported these sites to be fast and reliable: Coinmama - hxxps://www.coinmama.com Bitpanda - hxxps://www.bitpanda.com BTC : 19DpJAWr6NCVT2oAnWieozQPsRK7Bj83r4 ETH : 0x55069B5317529E07ccABAaA5AaE22a9bfa1C3E12 To confirm your purchase, please contact the administrator via email or Telegram: Email - [email protected] TLG - @payurransom ---------------------------------------------- ----> Restez concentré. <---- Tous vos fichiers ont été cryptés Votre ordinateur a été infecté par un virus ransomware. Vos fichiers ont été cryptés et vous ne le serez pas pouvoir les décrypter sans notre aide. Que puis-je faire pour récupérer mes fichiers ? Vous pouvez acheter notre logiciel de décryptage, ce logiciel vous permettra de récupérer toutes vos données et de supprimer les ransomware depuis votre ordinateur. Le prix du logiciel est de 130 $ ( 0,0027 BTC). Le paiement peut être effectué uniquement en Bitcoin. Comment payer, où puis-je obtenir du Bitcoin ? L\'achat de Bitcoin varie d\'un pays à l\'autre, il est préférable de faire une recherche rapide sur Google. Vous-même pour découvrir comment acheter du Bitcoin. Beaucoup de nos clients ont signalé que ces sites étaient rapides et fiables : Coinmama - hxxps://www.coinmama.com Bitpanda - hxxps://www.bitpanda.com BTC : 19DpJAWr6NCVT2oAnWieozQPsRK7Bj83r4 ETH : 0x55069B5317529E07ccABAaA5AaE22a9bfa1C3E12 Pour confirmer votre achat, veuillez contacter l\'administrateur via mail ou Telegram : Mail - [email protected] TLG - @payurransom
In the image below, you can see what a folder with files encrypted by the Payuranson looks like. Each filename has the ".payuranson" extension added to it.
How did my machine catch Payuranson ransomware?
There is a huge number of possible ways of ransomware infiltration.
Nowadays, there are three most exploited ways for criminals to have the Payuranson virus working in your system. These are email spam, Trojan injection and peer-to-peer file transfer.
- Another thing the hackers might try is a Trojan virus scheme. A Trojan is an object that gets into your computer disguised as something different. For example, you download an installer of some program you need or an update for some service. But what is unpacked turns out to be a harmful program that encodes your data. Since the update package can have any title and any icon, you have to make sure that you can trust the source of the stuff you're downloading. The optimal thing is to trust the software companies' official websites.
- As for the peer-to-peer networks like torrents or eMule, the danger is that they are even more trust-based than the rest of the Web. You can never know what you download until you get it. Our suggestion is that you use trustworthy resources. Also, it is reasonable to scan the directory containing the downloaded files with the antivirus as soon as the downloading is done.
How do I get rid of ransomware?
It is crucial to note that besides encrypting your files, the Payuranson virus will probably deploy Vidar Stealer on your computer to get access to credentials to various accounts (including cryptocurrency wallets). The mentioned spyware can derive your logins and passwords from your browser's auto-filling cardfile.
How do I avert ransomware injection?
Payuranson ransomware has no endless power, so as any similar malware.
You can armour yourself from its attack taking several easy steps:
- Never open any letters from unknown mailboxes with unknown addresses, or with content that has nothing to do with something you are expecting (can you win in a lottery without participating in it?). In case the email subject is likely something you are waiting for, check all elements of the questionable email with caution. A fake letter will always contain mistakes.
- Never use cracked or untrusted software. Trojans are often shared as a part of cracked software, possibly under the guise of “patch” to prevent the license check. But potentially dangerous programs are difficult to tell from reliable ones, as trojans sometimes have the functionality you need. Try to find information on this program on the anti-malware forums, but the best solution is not to use such software.
Frequently Asked Questions
🤔 How can I open ".payuranson" files?Are the ".payuranson" files accessible?
There's no way to do it, unless the files ".payuranson" files are decrypted.
🤔 The encrypted files are very important to me. How can I decrypt them quickly?
If the “.payuranson” files contain some really important information, then you probably have them backed up. In case you haven't, there is still a chance that you do have a Restore Point from some time ago to roll back the whole system to the moment when it had no virus yet, but already had your files. All other solutions require time.
🤔 What actions should I take if the Payuranson ransomware has blocked my PC and I can't get the activation code.
🤔 What can I do right now?
Many of the encrypted files might still be within your reach
- If you exchanged your important files by email, you could still download them from your online mailbox.
- You may have shared images or videos with your friends or relatives. Just ask them to give those pictures back to you.
- If you have initially downloaded any of your files from the Internet, you can try doing it again.
- Your messengers, social media pages, and cloud disks might have all those files as well.
- Maybe you still have the needed files on your old computer, a notebook, phone, memory stick, etc.
USEFUL TIP: You can use file recovery utilities2 to retrieve your lost information since ransomware encrypts the copies of your files, removing the authentic ones. In the tutorial below, you can learn how to recover your files with PhotoRec, but remember: you won't be able to do it before you remove the virus with an anti-malware program.


Leave a Comment