In May, JBS Foods was forced to temporarily suspend production at several sites as it was hacked, as it turned out, company paid the extortionists a ransom of $11 million.
The incident affected several JBS manufacturing facilities in various countries, including the United States, Australia and Canada.Today, JBS is the world’s largest supplier of beef and poultry, as well as the second largest producer of pork. The company operates in the USA, Australia, Canada, Great Britain and so on, serving clients from 190 countries.
Soon, the American authorities and the FBI reported that the responsibility for this attack most likely lay with the Russian-speaking hack group REvil (aka Sodinokibi).
In a new statement released last night, JBS officials said they paid the ransomware of $11 million to prevent hacker-stolen data from leaking out and to address potential technical issues.
Bleeping Computer journalists report that in early June, they had at their disposal the logs of correspondence between representatives of JBS and REvil discussing the ransom payments. Previously, the publication was sure that this was JBS negotiations, but then we did not manage to conduct an independent verification and confirm the authenticity of the logs.
Now the publication says that at the beginning of the negotiations, the ransom demand was $22.5 million, and the hackers warned that they would “leak” all the stolen data if they did not receive the money.
Before further negotiations, a JBS spokesperson asked the hackers to reveal the data stolen during the attack. But the REvil members seemed to realize that the attack on JBS had attracted worldwide attention, and the hackers refused to reveal any stolen information until payment was made.
In turn, the JBS employees explained that they only need the decryptor to decrypt two specific databases, since other information is already being restored from backups. As a result, after a series of offers and counter-offers, JBS and REvil agreed on a ransom of $ 11 million, and the payment in bitcoins was transferred on the same day, June 1, 2021.
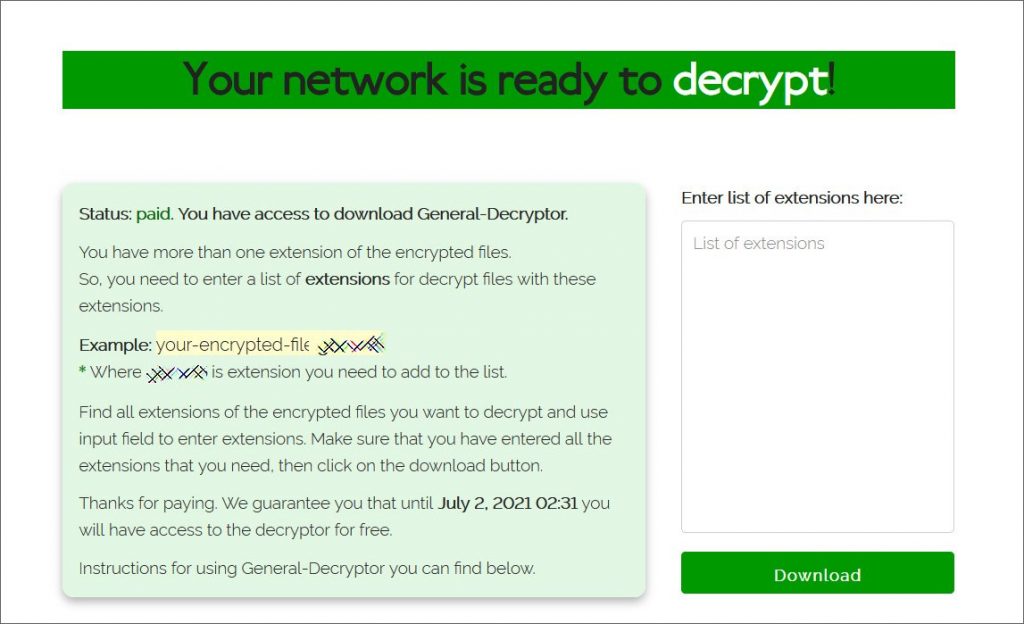
After the ransomware received the payment, they provided the victims with the data decryption tool shown in the screenshot below.
Journalists regret to note that the payment of such a large ransom, both in this case and in the recent case with the Colonial Pipeline company, only demonstrates to criminals that critical infrastructure is a tasty morsel, and in the future, we will surely face other targeted attacks of this kind.


Leave a Comment