You need to delete the viruses from your computer first of all
Otherwise, it will lock your PC or damage your files. In case your current anti-virus does not remove such malicious items, it can be deleted with GridinSoft Anti-Malware.
Hakbit stands for yet another Ransomware that has been actively attacking many PCs to target several groups of users. It attacks home computers primarily, even though the business ones are not an exception either. Even though the majority of its victims are the residents of the United States of America and Europe, it can hit the devices anywhere in the world as long as the user is not cautious enough. What is special regarding Hakbit is that it shows its requirement by amending the user’s desktop wallpaper. It also displays a QR code. The code once scanned, displays the attackers’ Bitcoin wallet addresses. In case the Hakbit attacks you, and your data is locked, Emsisoft has published a cost-free Decryptor for Hakbit.
Hakbit Ransomware Decryptor
The Hakbit Decryptor Tool is absolutely cost-free, and you can download it via the official webpage. Based on the information from Emsisoft, Hakbit applies AES-256 encryption algorithm and modifies the documents by means of adding the extension “.crypted”. It also tries to amend its name to a legitimate system file, for instance, lsass.exe, svchst.exe, crcss.exe, chrome32.exe, firefox.exe, calc.exe. In case the user opens any of these documents, it will begin locking down the data and then modify the wallpaper to show the notification demanding for the ransom to be paid in favor of the frauds.
The decryption utility can assist you in recovering all your locked data. The developers have elaborated a detailed user tutorial if you believe it quite complicated to follow.
How to decrypt files crypted by Hakbit?
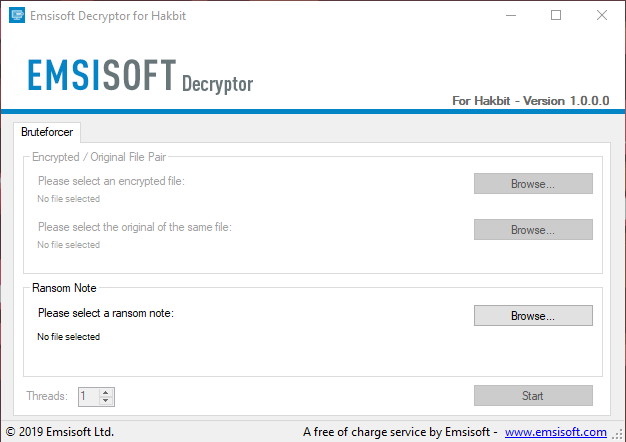
Keep in mind that this procedure implies the implementation of two phases. The first phase locates the key, whereas the second phase lies in applying the key to decrypting the documents.
1. Locate Hakbit Decryption key
- The first milestone is to find the ransom statement. The document is titled HELP_ME_RECOVER_MY_FILES.txt. The document can be found in your primary (system) partition.
- Once you launch the program, select the Start button so the program can find out the decryption key.
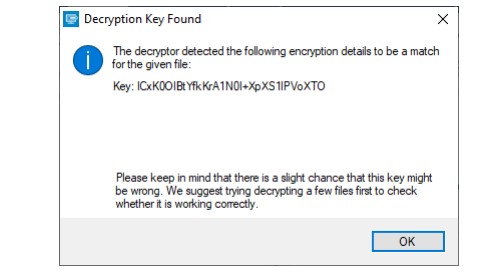
- As soon as the key is located, it will show the alert proving this fact. If you would like to, take note of the key and store it in a safe place.
2. Restore files modified by Hakbit
- Furthermore, you must choose the file or specify a location which has been modified, and a location to save the document once it has been successfully restored.
- Select the start button to start the restoration procedure.
- The decryptor will show the reconstructed encryption information as soon as the recovery procedure has been successfully accomplished.
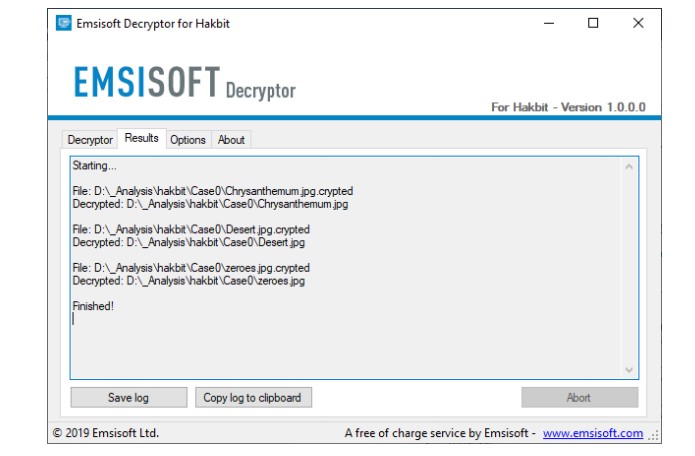
The Hakbit decryptor will inform you once the decryption process is finished. If you require the report
for your personal records, you can save it by clicking the Save log button. You can also copy it straight to your clipboard to paste it into emails or forum posts if you are asked to.
Available Hakbit decryptor options
The decryptor currently implements “Keep encrypted files” options:
Since the ransomware does not save any information about the unencrypted files, the Hakbit decryptor can not guarantee that the decrypted files is identical to the one that was previously encrypted. Therefore, the Hakbit decryptor by default will opt on the side of caution and not remove any encrypted files after they have been decrypted.
If you want the Hakbit decryptor to remove any encrypted files after they have been processed, you can disable this option. Doing so may be necessary if your disk space is limited.
I would suggest you copy the documents into an external drive instead of storing it on the same device. Ransomware is the main reason why you should enable Tamper Protection in place to everyone in Windows 10 through Microsoft Security. Microsoft also suggests OneDrive Personal Vault to assist you in defending the data on the cloud.


try DJVU Decryptor
hai this is kamalakar i can resolve .mbed file extension. u can send me on email – [email protected]
send me note and 2 r 3 files in i can restore data and i can send ur email. Is “Hakbit Ransomware Decryptor” able to decrypt .MBED ransomware?
please inform
i can’t Find Ransom Note or HELP_ME_RECOVER_MY_FILES.txt
but i know the key
fnolkcepCAnpUwqrVBxbuTM173fPmvhVRYJlajMX noos files
i choose File _readme.txt for Ransom Note
but the Program Gave
File not supported
and the Key
fnolkcepCAnpUwqrVBxbuTM173fPmvhVRYJlajMX
and my encrypted File with noos extension
how to get back with systemid because i lost windows after attacking this ransomware mosk extension
Starting ….
File: D:\100CANON\IMG_4844.JPG.mosk
Error: Unable to decrypt file with ID: UVfrncvDFGZFNm2yNUUtlAmM1BRbIvzZaLG7FFUC
File: D:\100CANON\IMG_4845 – Copy.JPG.mosk
Error: Unable to decrypt file with ID: UVfrncvDFGZFNm2yNUUtlAmM1BRbIvzZaLG7FFUC
File: D:\100CANON\IMG_4845.JPG.mosk
Error: Unable to decrypt file with ID: UVfrncvDFGZFNm2yNUUtlAmM1BRbIvzZaLG7FFUC
finished
Dear Writer..
A lot of information but it results without solution. As I see, the cybercriminals are using ms windows files and tools, so they did left the doors open to them and the ms winfows SHOULD give the solution and remedies.
How it is possible that law enforcement agencies do not get the traces since the crminals ask money living back such footprints?!
Funny and dramatic Stories
Hi any one help me
recently (15-02-2020) In my seagate external harddisk attacked .rooe rasomware virus.
How to decrypte my all photos and videos and documents.
please help me.
Hi.. Do you know of any tools to decrypt my files affected with the .jope ransomware? Thanks
Hi.. Do you know of any tools to decrypt my files affected with the lezpransomware? Thanks