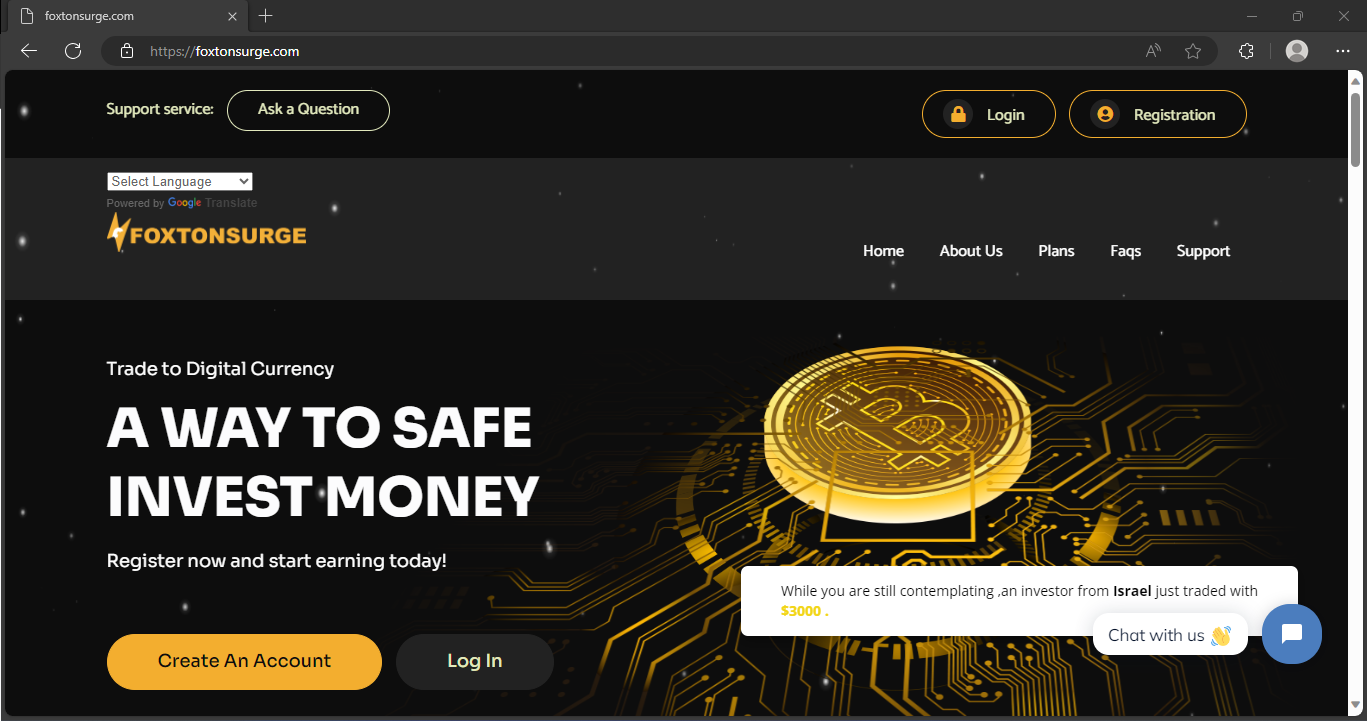
Recently, Foxtonsurge.com website popped up, promoting itself as a platform where you can securely keep cryptocurrency and other assets. I managed to gather reliable proof that clearly confirms it is, actually, a fraudulent platform.
Despite what Foxtonsurge site states, they won’t ever return your money. Even though the numbers displayed in the “member area”, there is no possibility to take out even a penny. All pledges regarding crypto incentives are hollow as well.
Foxtonsurge Scam Overview
The main feature that Foxtonsurge attempts to provide is a secure and user-friendly crypto wallet service. The site promises crypto exchange services, tools for controlling wallets, transfers, dashboards, and similar stuff. In truth, they endeavor to emulate the functionality of a crypto marketplace, like Binance or Coinbase. However, it in actuality only serves as a shell needed to lull the vigilance.
First and foremost, Foxtonsurge reproduces the layout of multiple similar websites. There are quite a few examples, like Delta, Criuspro or Crezominers. They are completely identical in terms of visual elements, with slight discrepancies in the site header. Other details, and at times even crypto wallet addresses, are matching. Probably, all these scam online platforms are managed by a single team of swindrels.
Cryptocurrency Scam Summary
| Website | Foxtonsurge.com |
| Hosting | AS22612 Namecheap, Inc. United States, Phoenix |
| IP Address | 66.29.141.3 |
| Threat Type | Scam/Fraud |
| Scam Type | Fraudulent offers of cryptocurrency services |
How the Foxtonsurge Scam Works?
Foxtonsurge is yet another webpage within a extensive network of associated crypto deceptive webpages. The managers employ different brand names and websites, like Foxtonsurge.com, to capture victims. Nonetheless, these false sites have in common matching website designs, terms of service, and About information. This reveals their sources as parts of the equal criminal network, which endorses the similar mode of scam under different appearances. The fraudsters simply replicate the identical fraudulent website under diverse names to deceive users into thinking they are joining a new opportunity. However, in actuality, it’s the identical group of fraudsters orchestrating the deceptive pledges and efforts to grab deposited funds. The operators skillfully make use of psychological maneuvers and enticing offers to execute their unscrupulous plans.
Step 1: Spreading
To initiate the scam, criminals set up and fill accounts on well-liked social media platforms. They primarily focus on Facebook, Instagram, Twitter, and TikTok. Subsequently, the promotional campaign commences. Using bots and paid ads (when achievable), scam actors intensify the exposure of their deceptive activities to possible victims. This strategy permits them to create a wide net and engage with their targeted viewers. This audience commonly consists of cryptocurrency enthusiastic individuals seeking prospects to generate profits.
Users get an encouragement to register, attracted by the promise of obtaining crypto rewards valued at thousands of dollars, all for free. To increase the appeal of the offer, fake suggestions of cooperation with a celebrity are added. As you may guess, these claims are completely baseless.
Step 2: Gaining Traffic
Individuals who show interest go to Foxtonsurge.com via links present in ads or robotic posts. The website uses captivating visuals, design aspects that appear authentic, and assertions of holding a official license, all aimed to project an initial perception of credibility.
Step 3: Data Gathering
To redeem their prizes, users need to actively create an profile on Foxtonsurge and get instructions to submit sensitive and personal data throughout the registration process. This includes linking their cryptocurrency wallets, revealing email addresses, specifying phone numbers, sending in identification papers, and the like.
Step 4: Requesting funds
Once registered, users notice substantial amounts of cryptocurrency, valued at thousands of dollars, within their Foxtonsurge wallets. Nonetheless, as it usually happens with such bonuses, you are unable to withdraw them prior to topping up your account. Usually, a payment of $100 is asked to withdraw the sign-up bonus. This stipulation serves as the trap that ultimately results to the money loss.
Step 5: Disappear
Signs of Scam
I gathered several facts that point at the scammy nature of the Foxtonsurge.com. Actually, there are a lot of scams that fall under the same points, so they are pretty much universal.
- Cryptocurrency-Only Transactions. Foxtonsurge.com insists on cryptocurrency payments exclusively, excluding conventional methods like bank transfers. This strategy ensures anonymity for the scam and eliminates any possibility of seeking refunds.
- Dubious Company Credentials. Foxtonsurge arouses suspicion by failing to provide critical information about ownership, location, and legal registration. The lack of valid contact details and the recent creation of domain and social media profiles cast doubt on its legitimacy.
- Baseless Hype Generation. Foxtonsurge resorts to fabricating non-existent achievements, such as contracts with Coinbase or endorsements from Elon Musk, to manipulate emotions and enhance the perception of potential returns, enticing victims to invest more.
- Fictitious Celebrity Association. Foxtonsurge employs a deceptive tactic by falsely associating itself with well-known figures like Elon Musk, Jeff Bezos, Mr. Beast, and Mark Zuckerberg. Additionally, the scam falsely claims partnerships with established entities like Coinbase, Binance, or MetaMask to bolster its false credibility.
- Potential Ponzi-Like Model. The scam operates on a pyramid-style referral system disseminated through social media, benefiting only initial participants and relying on later investments to sustain the illusion.
- Unrealistic Profit Promises. Promising improbable returns of 50-100-200%, Foxtonsurge capitalizes on the desire for high profits. However, the tumultuous nature of the cryptocurrency market renders such gains implausible, solidifying Foxtonsurge.com as a definite scam.
What Should I do as a Victim?
If you had to deal with Foxtonsurge site and fell victim to that scam, there are still some steps to take. They will make further scam attempts harder, and also boost the knowledge about that scam among folks.
- Report the scam to authorities. Search for local authorities responsible for financial frauds, and also notify wallet providers and social networks via their tech support. It is essential to make the further operations of these scammers much harder.
- Tell your close friends. That step is similar to reporting to the authorities, and has similar effects. By posting info about scam crypto service, you decrease the pool of people they can fool.
- Get evidence. Screenshot or save all the information related to the website. URL, screenshot of a main page, login window, EULA, account top-up menu, wallet addresses – all these things may be useful for authorities to find the scammers.
- Check whether you can ask for a refund. As I’ve said above, crypto payments do not fall under refund policies in most banks. Nonetheless, in some circumstances, it is still possible. Never lose hope until you actually confirm it is gone.
- Make your mistake your lesson. Financial losses are always a reason for frustration, but let’s imagine it was a pay for scam revealing courses. Remember the key features of these crypto scam sites, the way they attract people and what they promise. In the future, you will easily recognize a trap of spending no money.
Scan your system for possible malware infections
Beware of cross scams! Scam actors can use your trust to make you download some stuff or interact with certain documents. It may be a trap that installs malware to your system. There are no moral barriers or limits for these scoundrels.
Throughout the duration of the scam, fraudsters may reach out to you with specific documents. Alternatively, they may propose you to deploy “cryptocurrency wallet applications” or “browser extensions” to facilitate access to your cryptocurrency funds. As we earlier determined, these deceivers have no plan of returning your capital. So, what do these emails and browser plugins represent? Correct – that is another side of the deceptive plan designed to entice you into deliberately running harmful software onto your system.
Both extensions and files included to emails can function as a carrier for different malicious software. In this situation, I foresee the presence of spyware and stealers among all kinds of threats. While it is not obligatory for scammers to distribute malware, the probability is always significant. As noted, their conscience is of negligible importance, and their dignity is already severely tarnished. They have nothing to lose and strive to boost gains.
Frequently asked questions
- Contact your bank or card provider and ask about chargeback options.
- Save screenshots, receipts, tracking numbers, and emails as evidence.
- Change reused passwords and enable two-factor authentication on important accounts.
- Watch for follow-up phishing emails pretending to offer refunds or delivery updates.