If you see the message reporting that the Exploit:JS/CVE-2014-0322.A was identified on your computer, or in times when your computer system functions as well slow as well as offer you a lot of frustrations, you absolutely comprise your mind to scan it for CVE-2014-0322 as well as tidy it in a proper method. Now I will show to you how to do it.
Most of Exploit:JS/CVE-2014-0322.A are used to make a profit on you. The organized crime clarifies the variety of unsafe programs to steal your credit card information, online banking qualifications, as well as other data for deceptive objectives.
Kinds of viruses that were well-spread 10 years ago are no more the resource of the trouble. Presently, the trouble is extra obvious in the areas of blackmail or spyware. The problem of fixing these problems requires new softwares as well as different techniques.
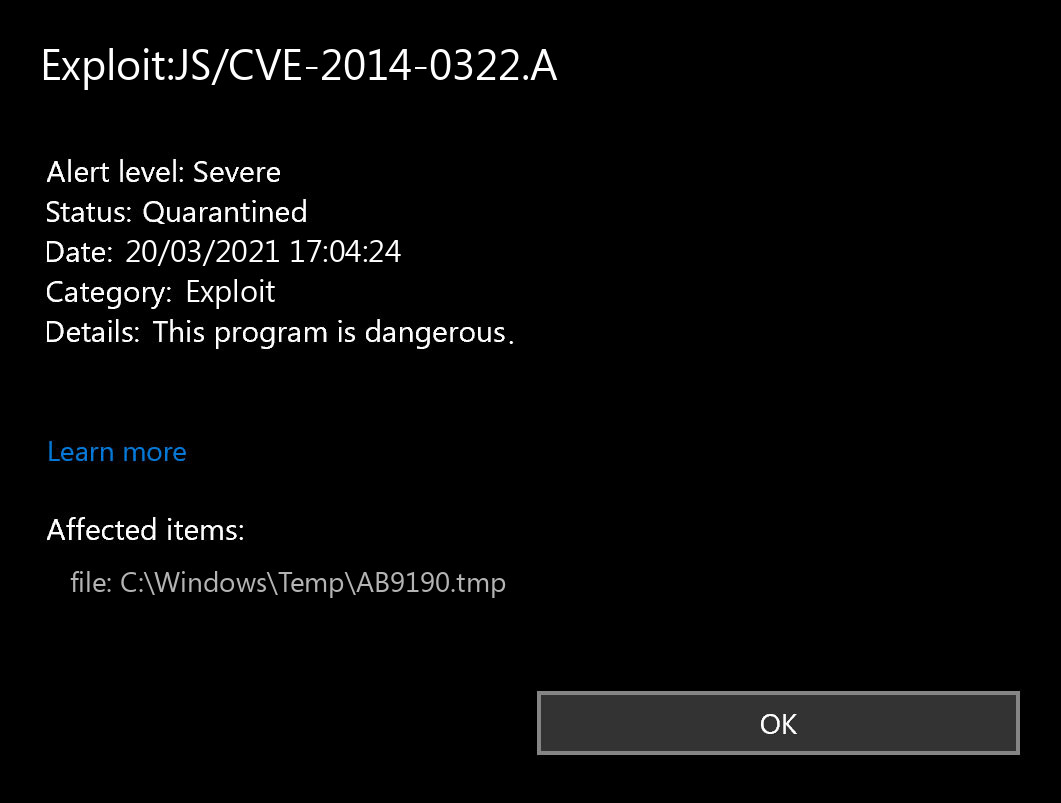
Does your antivirus regularly report about the “CVE-2014-0322”?
If you have seen a message suggesting the “Exploit:JS/CVE-2014-0322.A found”, then it’s a piece of great information! The infection “Exploit:JS/CVE-2014-0322.A” was found as well as, probably, removed. Such messages do not mean that there was an actually active CVE-2014-0322 on your gadget. You might have just downloaded a documents which contained Exploit:JS/CVE-2014-0322.A, so your anti-virus software application instantly erased it before it was released and also created the troubles. Additionally, the destructive manuscript on the infected web site could have been found and avoided prior to creating any kind of troubles.
To put it simply, the message “Exploit:JS/CVE-2014-0322.A Found” throughout the common use of your computer does not mean that the CVE-2014-0322 has completed its mission. If you see such a message after that it could be the proof of you going to the contaminated web page or filling the malicious documents. Attempt to prevent it in the future, however do not worry excessive. Explore opening up the antivirus program as well as inspecting the Exploit:JS/CVE-2014-0322.A detection log file. This will certainly offer you even more info about what the specific CVE-2014-0322 was identified and what was specifically done by your antivirus software application with it. Naturally, if you’re not positive sufficient, describe the hand-operated check– at any rate, this will be practical.
How to scan for malware, spyware, ransomware, adware, and other threats.
If your system works in a very lagging means, the websites open in an unusual way, or if you see ads in the position you’ve never expected, it’s possible that your system obtained infected as well as the virus is currently active. Spyware will track all your activities or redirect your search or home pages to the places you do not intend to see. Adware may infect your browser and also even the whole Windows OS, whereas the ransomware will certainly try to block your system and demand a remarkable ransom money quantity for your own data.
How to scan your PC for Exploit:JS/CVE-2014-0322.A?
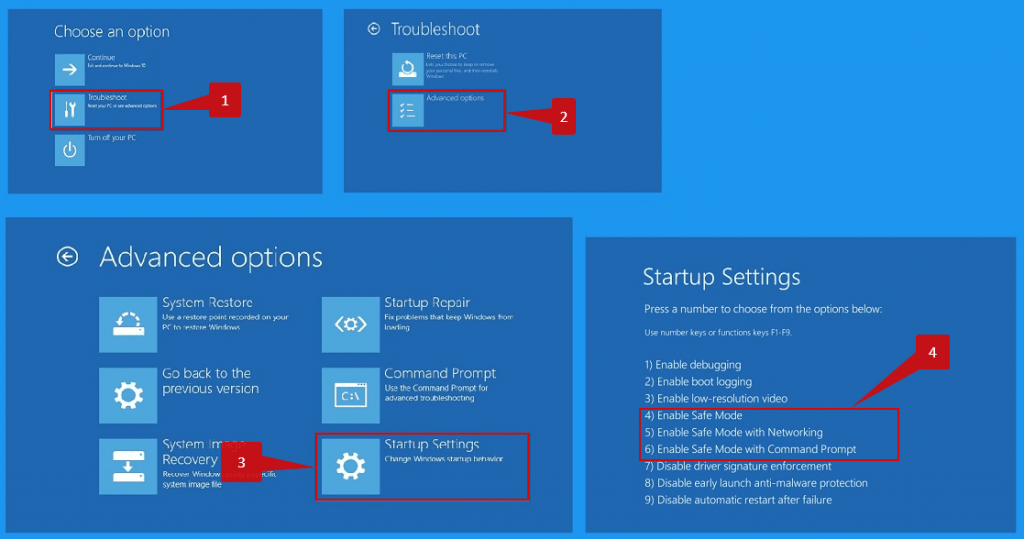
Use Safe Mode to fix the most complex Exploit:JS/CVE-2014-0322.A issues.
It’s not sufficient to simply use the antivirus for the security of your PC. You need to have much more extensive antivirus app. Not all malware can be detected by regular antivirus scanners that primarily look for virus-type dangers. Your system might have lots of “trash”, for instance, toolbars, internet browser plugins, unethical internet search engines, bitcoin-miners, and also other kinds of unwanted software used for generating income on your lack of experience. Be cautious while downloading programs online to stop your device from being loaded with unwanted toolbars as well as other scrap information.


Leave a Comment