Domain owners often park them and use the services of special providers to monetize domains through ad networks while they are not used for their intended purpose. Recently, cybersecurity experts found out that attackers, for example, Emotet malware operators, use parked domains.
Setting up a parking service is simple and only requires domain owners to point their name server (NS) records to the parking service. In turn, parking services will either provide visitors with a list of advertisements or automatically redirect users to advertisers’ web pages.Palo Alto Networks experts say that from March to September 2020, they discovered about 5,000,000 new parked domains, and about 1% of them are used by hackers to spread malware and within phishing campaigns; about 2.6% are now associated with adult content or gambling, and another 30.6% are suspicious.
Such attacks target victims from all over the world, including the United States, Britain, France, Japan, Korea, and Italy.
Emotet botnet operators also use parked domains. Their campaign targets many different industries, from government and education to energy, manufacturing, construction, and telecommunications.
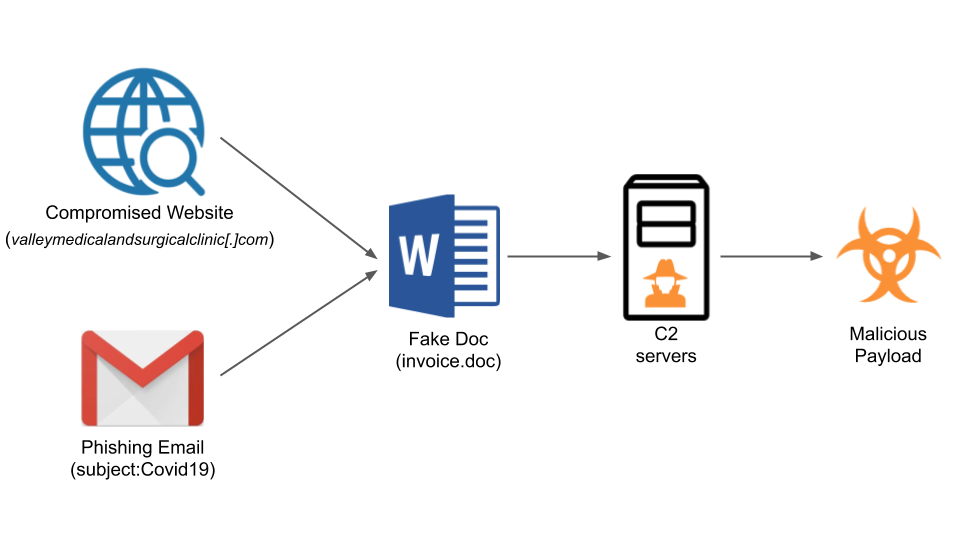
For example, one of the domains used in the attacks, valleymedicalandsurgicalclinic[.]com, was registered on July 8, 2020, and was parked immediately.
Starting on September 14, just two months after registration, this domain became malicious and began spreading various malware. Among other things, it was used to distribute Emotet payloads through phishing emails, which ultimately led to the theft of accounts and complete takeover of infected devices.
Let me also another time warn thar Emotet Trojan Returns in Spam Attacks Dropping Qbot TrickBot.


Leave a Comment