Recently, Bupbit.com site appeared, promoting itself as a platform where you can safely store cryptocurrency and other assets. I managed to gather reliable supporting information that clearly confirms it is, actually, a scam service.
Despite what Bupbit site says, they won’t ever pay off your capital. Despite the money displayed in the “member area”, there is no possibility to withdraw even a cent. All commitments regarding crypto bonuses are hollow as well.
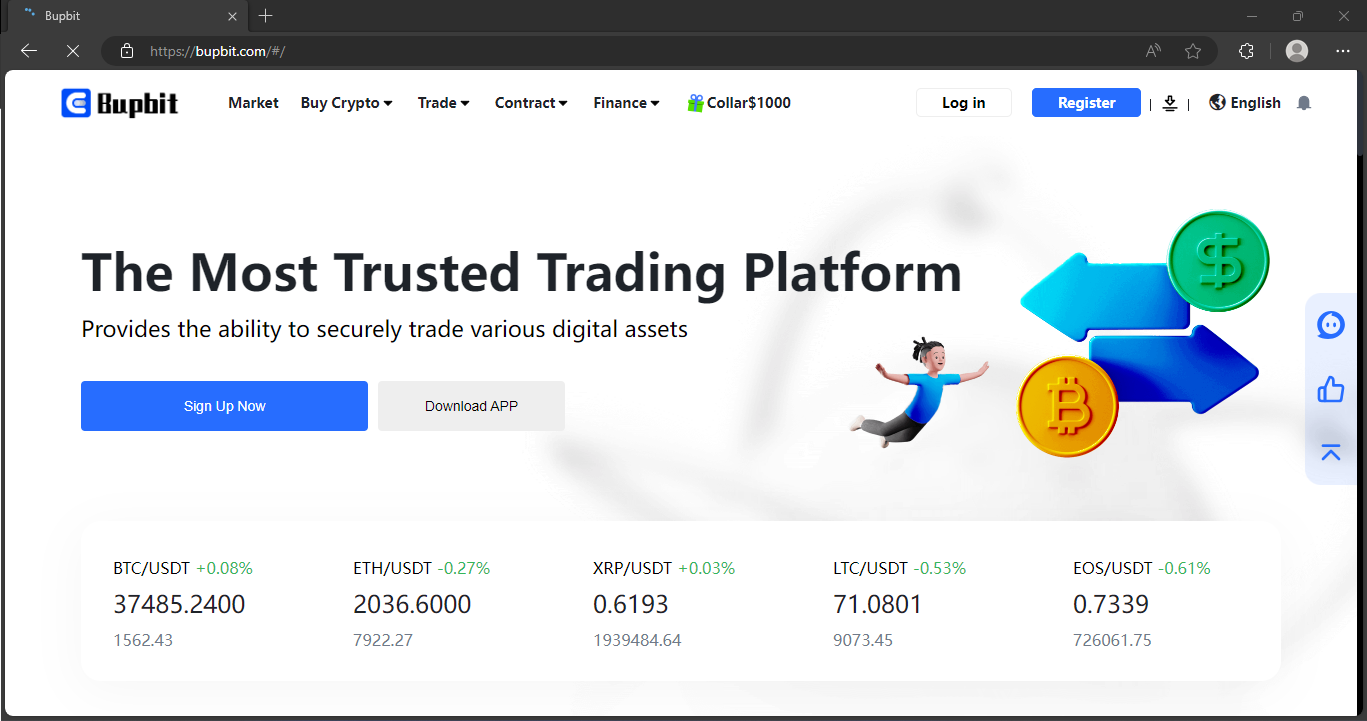
Bupbit Scam Overview
The primary offering that Bupbit aims to provide is a protected and convenient cryptocurrency wallet service. The site promises exchange facilities, tools for handling wallets, transfers, dashboards, and similar stuff. In reality, they endeavor to emulate the functionality of a crypto exchange, akin to Binance or Coinbase. However, it actually solely serves as a cover intended to deceive the cautious.
First and foremost, Bupbit mimics the layout of multiple similar online platforms. There are quite a few examples, like Pbsx, Kinemarket or Haxitradings. They are totally identical in terms of graphic elements, with minor discrepancies in the webpage header. Other particulars, and sometimes even crypto wallet addresses, are matching. Most likely, all these scam sites are operated by the same gang of fraudsters.
Cryptocurrency Scam Summary
| Website | Bupbit.com |
| Hosting | AS13335 Cloudflare, Inc. United States, San Francisco |
| IP Address | 104.21.32.113 |
| Threat Type | Scam/Fraud |
| Scam Type | Fraudulent offers of cryptocurrency services |
How the Bupbit Scam Works?
Bupbit is yet another online platform within a extensive network of interconnected crypto scam platforms. The administrators employ diverse brand names and sites, like Bupbit.com, to ensnare victims. Nevertheless, these fraudulent sites possess the same designs, terms of service, and About information. This reveals their sources as parts of the same criminal network, which promotes the identical mode of scam under diverse disguises. The scammers merely duplicate the same fraudulent site under different names to fool users into believing they are joining a new platform. However, in actuality, it’s the identical group of swindlers orchestrating the fraudulent promises and undertakings to seize deposited cryptocurrency. The administrators cleverly employ psychological tactics and appealing propositions to execute their deceitful plans.
Step 1: Spreading
To start the scam, criminals set up and fill accounts on well-liked social media platforms. They mainly focus on Facebook, Instagram, Twitter, and TikTok. Subsequently, the promotional campaign starts. Utilizing bots and sponsored promotions (when achievable), scam actors increase the presence of their scam activities to potential victims. This tactic allows them to cast an extensive net and connect with their focused audience. The latter usually comprises of cryptocurrency enthusiastic individuals seeking chances to generate profits.
Step 2: Gaining Traffic
Users who express interest go to Bupbit.com via links featured in advertisements or robotic posts. The site employs captivating visuals, design features that appear genuine, and claims of having a official license, all intended to project an initial perception of trustworthiness.
Step 3: Data Gathering
To claim their rewards, users are required to deliberately sign up on Bupbit and receive guidance to provide sensitive and personal data during the registration procedure. This comprises linking their cryptocurrency wallets, providing email addresses, specifying phone numbers, sending in identification papers, and the like.
Step 4: Requesting funds
Once registered, users observe considerable amounts of cryptocurrency, valued at thousands of dollars, within their Bupbit wallets. Nonetheless, as is common with such rewards, you can’t withdraw them ahead of topping up your account. Typically, a payment of $100 is required to access the sign-up bonus. This stipulation serves as the trap that ultimately leads to the money loss.
Step 5: Disappear
The instant the payment is made, the deceivers halt all communication. They go ahead to block users, delete accounts, and disappear with both the submitted money and essential personal data. The fabricated rewards continue to be perpetually uncredited, as they lack actual existence. They operate purely as a deceptive strategy. This technique forms the foundation for the scammers’ capacity to mislead victims and embezzle hard-earned funds through their deceptive web crypto scam.
Signs of Scam
I gathered several facts that point at the scammy nature of the Bupbit.com. Actually, there are a lot of scams that fall under the same points, so they are pretty much universal.
- False Celebrity Sponsorship. Bupbit often resorts to fake endorsements from celebrities such as Elon Musk, Jeff Bezos, Mr. Beast, and Mark Zuckerberg. This fraudulent tactic extends to claiming partnerships with reputable companies like Coinbase, Binance, or MetaMask, despite lacking any genuine affiliations.
- Cryptocurrency-Only Payments. Bupbit.com exclusively accepts payments in cryptocurrencies, rejecting traditional bank transfers and other methods. This approach not only masks the company’s identity but also eliminates the possibility of seeking refunds.
- Dubious Company Information. Bupbit raises suspicion by withholding essential ownership, location, and registration details. Furthermore, the absence of legitimate contact information and the recent establishment of domain and social media pages intensify skepticism.
- Unsubstantiated Hype. Bupbit.com employs groundless hype tactics, fabricating events like securing contracts with Coinbase or receiving endorsements from Elon Musk. These manipulative techniques aim to instill false confidence and encourage further investments.
- Potential Pyramid Scheme. The scam relies on a structure resembling a Ponzi scheme, leveraging a referral system spread through social media. However, only initial participants benefit, often at the expense of subsequent investors.
- Implausible Claims. Promising returns of 50-100-200%, Bupbit preys on the desire for quick profits. Yet, the volatile nature of the cryptocurrency market makes such gains highly unlikely, definitively labeling Bupbit as a scam.
What Should I do as a Victim?
If you had to deal with Bupbit site and fell victim to that scam, there are still some steps to take. They will make further scam attempts harder, and also boost the knowledge about that scam among folks.
- Report the scam to authorities. Search for local authorities responsible for financial frauds, and also notify wallet providers and social networks via their tech support. It is essential to make the further operations of these scammers much harder.
- Tell your close friends. That step is similar to reporting to the authorities, and has similar effects. By posting info about scam crypto service, you decrease the pool of people they can fool.
- Get evidence. Screenshot or save all the information related to the website. URL, screenshot of a main page, login window, EULA, account top-up menu, wallet addresses – all these things may be useful for authorities to find the scammers.
- Check whether you can ask for a refund. As I’ve said above, crypto payments do not fall under refund policies in most banks. Nonetheless, in some circumstances, it is still possible. Never lose hope until you actually confirm it is gone.
- Make your mistake your lesson. Financial losses are always a reason for frustration, but let’s imagine it was a pay for scam revealing courses. Remember the key features of these crypto scam sites, the way they attract people and what they promise. In the future, you will easily recognize a trap of spending no money.
Scan your system for possible malware infections
Beware of cross scams! Scam actors can use your trust to make you download some stuff or interact with certain documents. It may be a trap that installs malware to your system. There are no moral barriers or limits for these scoundrels.
Throughout the duration of the fraud, its actors may contact you with specific files. Alternatively, they may suggest you to install “cryptocurrency wallet applications” or “browser extensions” to streamline access to your cryptocurrency savings. As we previously figured out, these scoundrels have no intent of giving back your money. So, what do these email messages and browser extensions represent? You guessed – that is another side of the fraudulent scheme designed to entice you into willingly installing destructive applications onto your device.
Both add-ons and attachments included to emails can function as a shell for various malicious code. In this scenario, I foresee the presence of spyware and stealers among all kinds of malware. While it is not obligatory for scammers to distribute malware, the chance is always significant. As stated, their ethics is of negligible importance, and their dignity is already deeply compromised. They have no scruples to lose and strive to boost gains.
Frequently asked questions
- Contact your bank or card provider and ask about chargeback options.
- Save screenshots, receipts, tracking numbers, and emails as evidence.
- Change reused passwords and enable two-factor authentication on important accounts.
- Watch for follow-up phishing emails pretending to offer refunds or delivery updates.