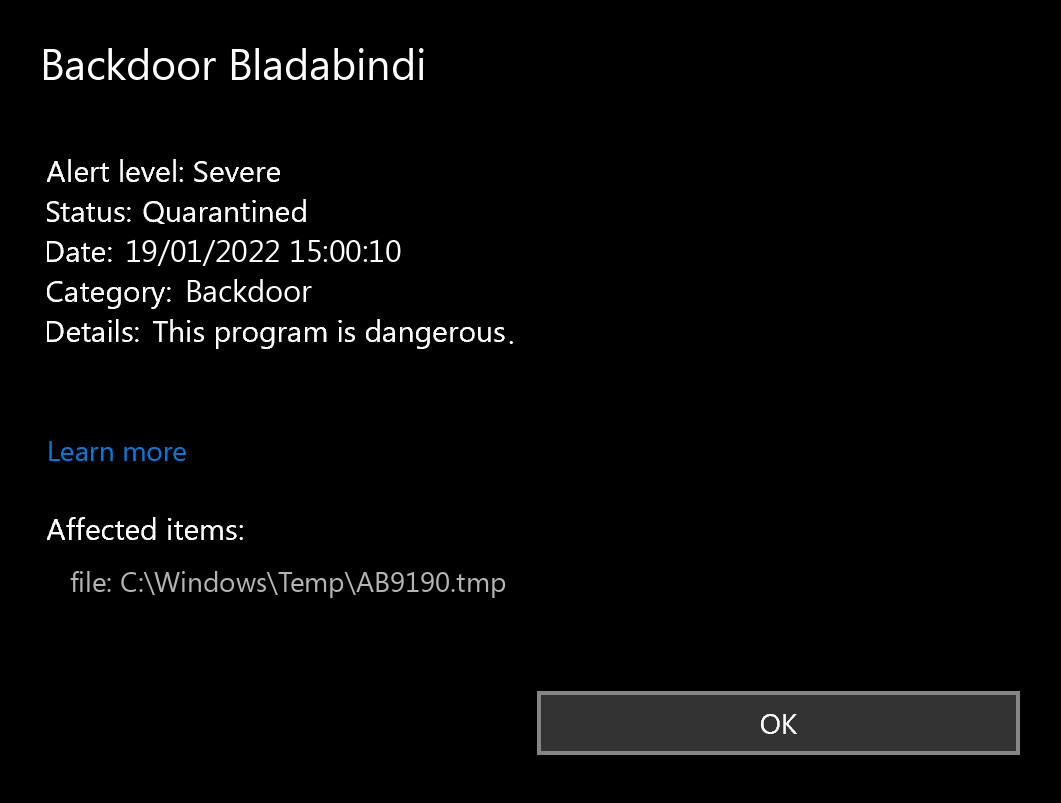
If you spectate the notification of Backdoor Bladabindi detection, it looks like that your system has a problem. All malicious programs are dangerous, without any exceptions. Bladabindi gives the criminals access to your computer, or even adds it to the botnet.
What does the pop-up with Backdoor Bladabindi detection mean?
The Backdoor Bladabindi detection you can see in the lower right side is shown to you by Microsoft Defender. That anti-malware program is good at scanning, however, prone to be basically unstable. It is defenseless to malware invasions, it has a glitchy interface and bugged malware clearing features. For this reason, the pop-up which states about the Bladabindi is just an alert that Defender has identified it. To remove it, you will likely need to make use of a separate anti-malware program.
The exact Backdoor Bladabindi virus is a really nasty thing. This malware is developed to be a stealthy intruder, which serves as a remote-access tool. When you grant someone remote access willingly, it is alright, but Bladabindi will not ask you if you wish to provide it. After connecting to your system, crooks are able to do whatever they want – snatching your files, reading your messages, gathering personal info, and so on. Backdoors commonly carry a supplementary stealer – the virus that is designed to collect all available information about you. Nevertheless, a lot more prevalent use of the backdoors is establishing the botnet. After that, the network of infected systems can be used to conduct DDoS attacks or to inflate the survey results on various sites.
Backdoor Summary:
| Name | Bladabindi Backdoor |
| Detection | Backdoor Bladabindi |
| Damage | Gain access to the operating system to perform various malicious actions. |
| Similar | Bifrose, Ircbot, Patched, Win64 Sandcat, Msil Turtleloader, Blacknet, Xtrat, Bulord |
| Fix Tool | See If Your System Has Been Affected by Bladabindi backdoor |
Shortly about backdoors
Is Backdoor Bladabindi dangerous?
As I have actually pointed out, non-harmful malware does not exist. And Backdoor Bladabindi is not an exclusion. This backdoor does not deal much damage exactly after it launches. Nevertheless, it will likely be a very unpleasant surprise when a random forum or site in the Internet will not let you in, since your IP-address is banned after the DDoS attack. However, even if it is not critical for you – is it nice in any way to realize that someone can easily access your PC, check out your discussions, open your documents, as well as spectate what you do?
Complexity of the modern malware must make the users concerned about their security. Thoughts like “oh, it is just a backdoor, it cannot critically damage my system” are reckless. Bladabindi backdoor can easily be used as a downloader trojan, bringing much more dangerous malware to your system. The presence of this malware is even worse if you have it on your office PC – it exposes the whole corporate network to a significant danger.
Backdoor Bladabindi actions
After the successful injection, Bladabindi makes the following actions on the computer:
The spyware that is often present as a supplement to the Backdoor Bladabindi malware will be just one more reason to remove it as fast as you can. Nowadays, when users’ data is valued incredibly high, it is too illogical to give the crooks such an opportunity. Even worse if the spyware will somehow handle to thieve your banking information. Seeing 0 on your savings account is the most awful headache, in my point of view.
How did I get this virus?
It is not easy to trace the sources of malware on your computer. Nowadays, things are mixed up, and spreading tactics utilized by adware 5 years ago may be used by spyware these days. However, if we abstract from the exact spreading method and will think about why it works, the explanation will be pretty simple – low level of cybersecurity understanding. People click on ads on odd websites, click the pop-ups they receive in their web browsers, call the “Microsoft tech support” assuming that the weird banner that says about malware is true. It is essential to understand what is legitimate – to avoid misconceptions when attempting to identify a virus.
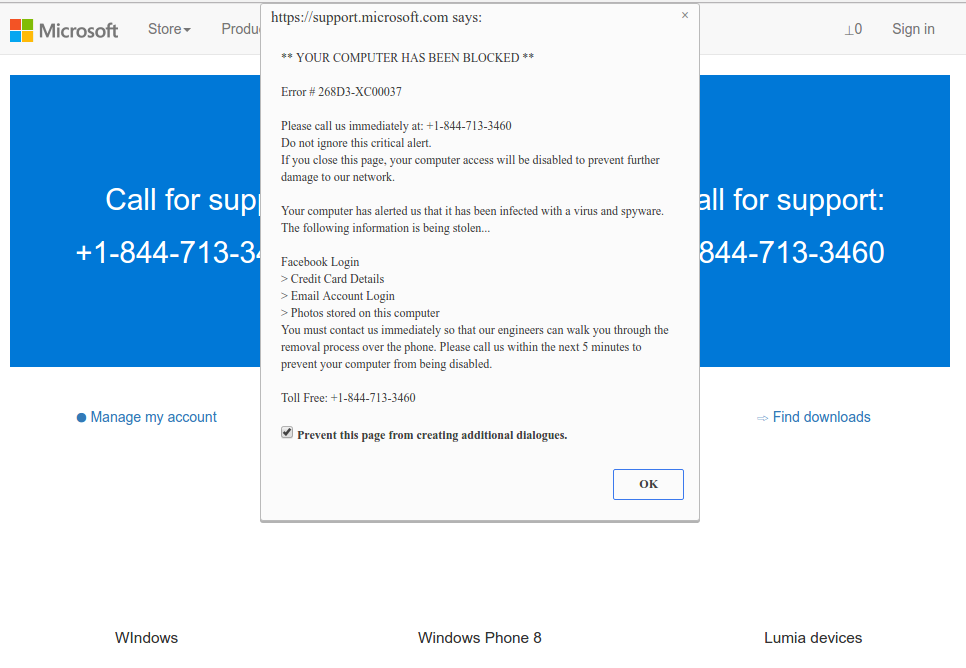
Microsoft Tech Support Scam
Nowadays, there are two of the most extensive methods of malware distribution – lure emails and also injection into a hacked program. At the time of research, Bladabindi has been observed being proliferated by and bundled with Windscribe VPN installers. These bundles with the VPN application were not distributed through official channels (e.g., Windscribe’s website, Google, or Apple stores). Cybercriminals promoted the modified installers through unofficial third-party download sources. While the first one is not so easy to evade – you need to know a lot to recognize a counterfeit – the 2nd one is simple to solve: just don’t utilize cracked applications. Torrent-trackers and various other sources of “free” applications (which are, in fact, paid, but with a disabled license checking) are really a giveaway point of malware. And Backdoor Bladabindi is just one of them.
How to remove the Backdoor Bladabindi from my PC?
References
- Gossip about the backdoor in Intel processors on Reddit.


Leave a Comment