Agent Racoon, a potent backdoor malware exploiting the .NET framework, spreads through undisclosed means, likely employing phishing and social engineering tactics.
Agent Racoon establishes communication with a Command and Control server via the DNS protocol. Operating with scheduled tasks, it executes commands, uploads/downloads files, and has been observed in attacks targeting governmental and non-profit entities.
Agent Racoon Overview
Agent Racoon, a malevolent program crafted with the .NET framework, falls into the backdoor category. Malware in this class aims to breach targeted systems by creating a covert entry point. Typically, such programs play a crucial role in the initial stages of multi-step infections. Unveiled in July 2022, the first instances of Agent Racoon traced back to a C&C (Command and Control) domain registered in August 2020.
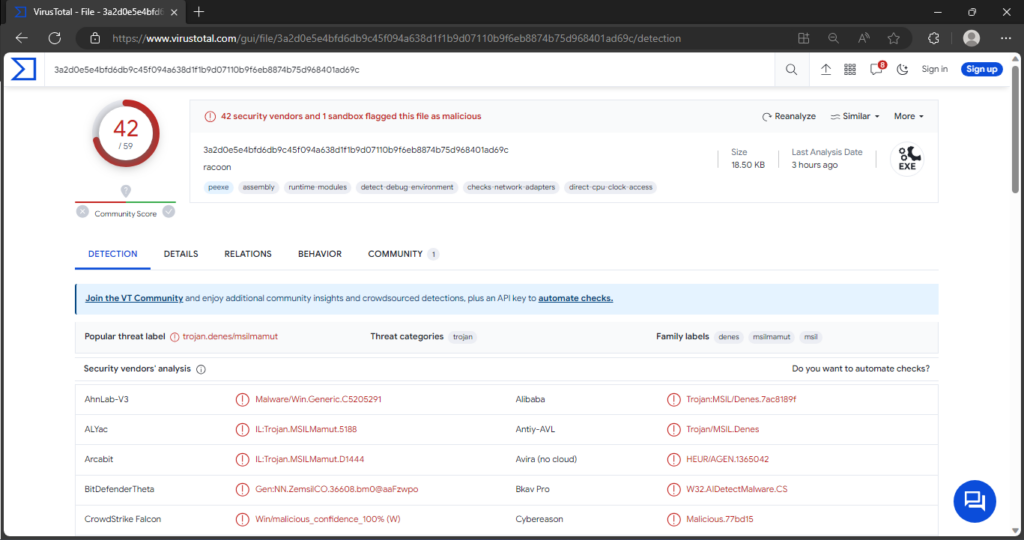
Agent Racoon on Tirus Total site
This backdoor, in conjunction with other malicious software, has been identified in assaults against organizations in the Middle East, Africa, and the United States. Notably, Agent Racoon featured prominently in infections directed at governmental entities and non-profit organizations. Indications point to the possibility of these attacks being orchestrated by a state-backed threat actor.
| Name | Agent Racoon |
| Threat Type | Trojan, backdoor |
| Payload | Ntospy, Mimilite (custom Mimikatz) |
| Distribution methods | Infected email attachments, malicious online advertisements, social engineering, software ‘cracks’ |
| Detection | Microsoft (Trojan:MSIL/Tnega!MTB) |
| Damage | Stolen passwords and banking information, identity theft, the victim’s computer added to a botnet. |
Technical Analysis of Agent Racoon
In the technical examination of Agent Racoon, this backdoor emerges as a pivotal component geared towards priming compromised systems for subsequent infections. To establish communication with its Command and Control (C&C) server, Agent Racoon tactically exploits the Domain Name System (DNS) protocol. Operating primarily through scheduled tasks, it refrains from employing specific persistence-ensuring techniques. Notably, the utilization of communication loops during C&C server interactions serves as a potential anti-detection measure, simultaneously reducing the risk of network jamming and activity spikes.
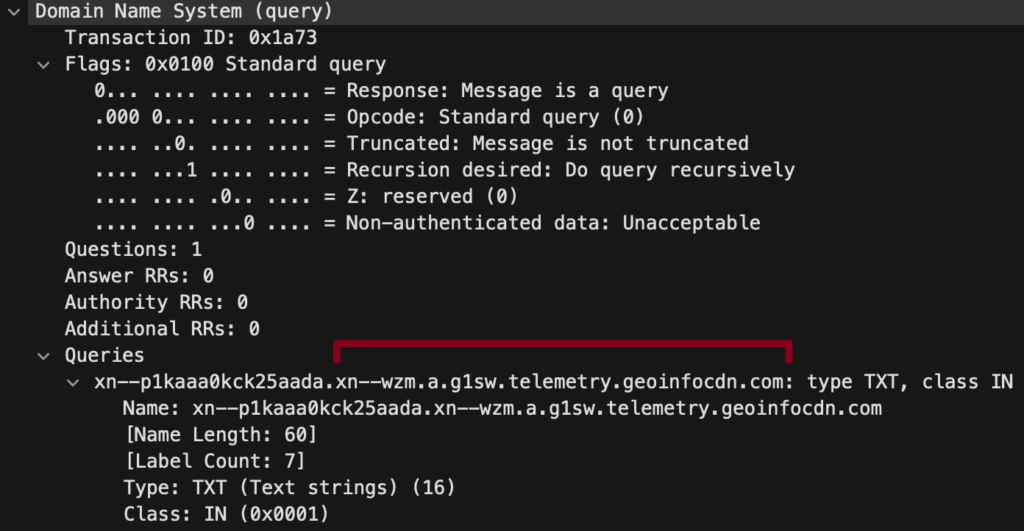
DNS query sample
Agent Racoon’s functionality extends to executing commands, along with the capability to upload and download files. The former facilitates the infiltration of additional malicious content, while the latter enables data exfiltration. In documented instances of Racoon attacks, Ntospy and Mimilite, a streamlined variant of Mimikatz, were deployed for credential theft. These attacks featured supplementary anti-detection tactics, incorporating the use of temporary folders and a tool designed to eradicate infection artifacts post-assault. Some malicious programs adopted disguises as Microsoft updates to further obfuscate their presence.
Spreading methods
The spreading methods of Agent Racoon are deliberately concealed, heightening its sophistication. And while specific details are unavailable, the malware likely employs common vectors associated with malicious software:
- Phishing and Social Engineering. Potential use of deceptive tactics to trick users into unknowingly downloading and executing the malware.
- DNS Protocol Communication. Establishment of communication channels through the Domain Name System (DNS) protocol for covert interactions.
- Concealing itself within diverse file formats, such as archives (ZIP, RAR), executables (.exe, .run), documents (PDF, Microsoft Office), and JavaScript.
- Ability to self-spread through local networks and removable storage devices like USB flash drives and external hard drives.
- Utilization of stealthy drive-by downloads and leveraging dubious download channels, potentially exploiting unofficial file-hosting sites or Peer-to-Peer networks.
How to remove the Agent Racoon Virus from my PC?
While manual removal of the threat is technically possible, I strongly discourage this method. In its pursuit of establishing persistence, Malware generates numerous instances of itself, making it exceedingly difficult to trace all its components manually. Consequently, manual removal can be time-consuming and often yield minimal to no results. Below, I have assembled a guide outlining the most effective removal practices for Agent Racoon Virus.


Leave a Comment