What is Trojan:Win32/Wacatac.D!ml infection?
In this article you will certainly find concerning the definition of Trojan:Win32/Wacatac.D!ml as well as its negative influence on your computer. This virus can be correctly identified as spyware – virus that steals your credentials, information about your PC and installed programs.
In the majority of the situations, Trojan:Win32/Wacatac.D!ml infection will not try to show its presence in your system. The more time that virus will be active, the more data it will steal from the user’s PC.
Trojan:Win32/Wacatac.D!ml Summary
These alterations can be as follows:
- A process attempted to delay the analysis task.;
- Attempts to connect to a dead IP:Port (1565 unique times);
- A process created a hidden window;
- Drops a binary and executes it. Trojan-Downloader installs itself to the system and waits until an Internet connection becomes available to connect to a remote server or website in order to download additional malware onto the infected computer.
- The binary likely contains encrypted or compressed data. In this case, encryption is a way of hiding virus’ code from antiviruses and virus’ analysts.
- HTTP traffic contains suspicious features which may be indicative of malware related traffic;
- Performs some HTTP requests;
- Uses Windows utilities for basic functionality;
Trojan:Win32/Wacatac.D!ml visible effects
After being successfully injected, Wacatac Trojan changes your hosts file. This file contains the data about priority DNS addresses for specified websites. Trojan adds anti-malware forums, anti-malware software vendors sites, and advisory sites, like this one, to the hosts, specifying DNS-address of 127.0.0.1 (the address of your PC in the local network). Hence, every time you’d try to open these sites, your browser will try to connect to 127.0.0.1 and show that there is no connection to the server.
Here is the list of the websites which are usually added to the hosts file by Wacatac Trojan :
- kaspersky.com
- bleepingcomputer.com
- howtofix.guide
- malwarebytes.com
- norton.com
- mcafee.com
Fortunately, hosts file may be easily fixed manually. It is located at %SystemRoot%\drivers\etc\ and may be opened with a Notepad.
This malware can also disable Windows updates. The mechanism is the same as for anti-malware sites: Wacatac adds a Microsoft update server to the host’s file, and then your PC will not have the ability to connect to this server and get any updates.
The trojan-activity may be spotted in the Task Manager. Wacatac Trojan runs the following processes :
- “%User Temp%\2ce0441691b70fb6a6a53618c1e7590c54f00a10.exe”
- %System%\lsass.exe
- %Windows%\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe
All these processes consume a lot of your PC’s resources, so you will find them easily in Task Manager. And they are quite hard to stop: every time you try to stop them with the proper Task Manager button, they will disappear for several seconds, then appear again.
The reason for such immortality is that Wacatac Trojan creates several scripts, which are tracking the correct execution of mentioned processes. And these scripts are hidden somewhere deep in your file system. Every time one of the processes disappears, these scripts start again. That’s why it’s better to use the method we are offering below than to try to deal with Wacatac by yourself.
In process of it’s activity, Wacatac connects to “http://{BLOCKED}x.com/deal/five/fre.php.”. We have no information about this URL’s purpose, but it looks like the Trojan collects some of your data and then sends it to this website.
Trojan:Win32/Wacatac.D!ml creates several additional folders in your file system. These folders are usually located through Windows files on the C disc, so it can be quite hard to find them, especially considering the usual amount of folders created by Windows.
The Wacatac Trojan can also delete some of your system files! The most frequent action is lastgood.tmp file removal. This file is created by Windows every time you are installing the program, which changes the system files (i.e., registry or so) and contains the backup of system files changed. If something goes wrong, your system will perform self-repairing using this file. And since the Wacatac Trojan deleted this file, no restoration appears to be available.
Registry editing usually contains of creating the additional entry to the RunOnce key. After this operation, Wacatac Trojan will launch together with your system, regardless of the trojan’s manual launch. The malware, which is launching in such a way, maybe stopped only with safe mode launch with command prompt support.
Besides the RunOnce key, Wacatac also changes the following registry key :
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\Dnscache Type = "16"
The profit which trojan gets by editing this key is unknown. However, the possible effects for the Windows functionality are unknown, too.
Any registry changes are dangerous at all if a professional user does not implement them. And these changes may be especially dangerous if malicious programs do them. Trojan’s target is not only your data: it also tries to create chaos and make it impossible to do any actions on your PC. So, it may break your registry purposely.
Trojan:Win32/Wacatac.D!ml has several habits that are more typical for browser hijacker than for trojan. Wacatac usually changes your browser settings, setting your homepage to Yahoo, for example, and redirecting your search queries to the doorway websites.
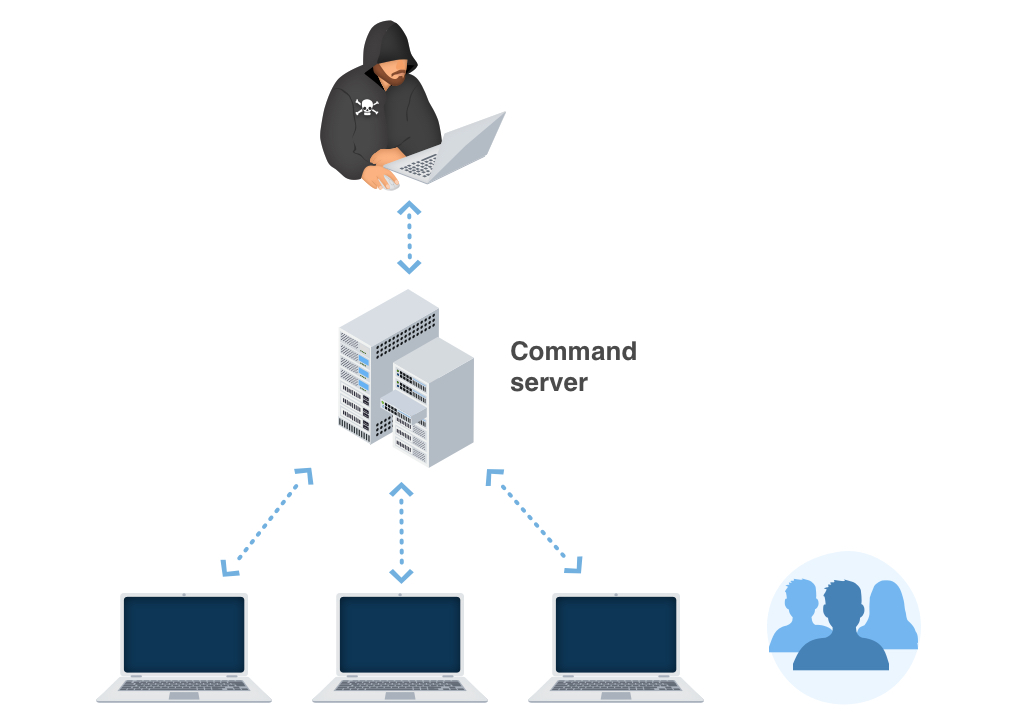
Trojan:Win32/Wacatac.D!ml distribution networks.
The biggest share of Trojan:Win32/Wacatac.D!ml virus distribution is after these methods:
- Email spam
- Unlicensed software usage
- Malvertising on the Web
For example:
Popular ways of the Trojan:Win32/Wacatac.D!ml injection
You can get the Trojan:Win32/Wacatac.D!ml on your PC in different ways. But one of the most popular ways of Wacatac injection is crackware. No one can warrant that the user who cracked the program hasn’t added any additional and undeclared programs to the installation file.
Besides an injection as a pack with crack, Trojan:Win32/Wacatac.D!m can also arrive in your system after other malware dropped a file. This file is run autonomously. Hence the Wacatac trojan will get to your PC without any signs.
We also got several reports about Wacatac injection from doorway/advertisement website. Adware, which is guilty of this website’s opening, may show you the ad that has a link to Wacatac Trojan downloading. All these actions look easy to avoid, but these advertisements may appear every moment, overlaying all other windows, so you can just misclick and start downloading an unwanted application.
Due to the statistic, there is one adware that will surely show you an ad with the link to Wacatac downloading. We are talking about Uwasson adware. That is the “classic” adware, which changes your search engine, opens additional windows with advertisements, and redirects your search query to the doorway websites.
Faulty notifies about unlicensed software.
In certain areas, the Trojans usually wrongfully report having detected some unlicensed applications allowed on the victim’s gadget. The sharp after that demands the customer to pay the ransom.
Faulty declarations regarding prohibited content.
In countries where software piracy is much less preferred, this technique is not as reliable for cyber frauds. Additionally, the Trojan:Win32/Wacatac.D!ml popup alert may incorrectly claim to originate from a law enforcement organization and report having situated kid pornography or other prohibited data on the device.
Trojan:Win32/Wacatac.D!ml popup alert might incorrectly claim to be deriving from a regulation enforcement organization and also will report having located youngster porn or various other unlawful information on the device. The alert will likewise consist of a requirement for the individual to pay the ransom.
Technical details
File Info:
crc32: 166ADDAFmd5: 01a9b1f9a9db526a54a64e39a605dd30name: c.datsha1: a436e3f5a9ee5e88671823b43fa77ed871c1475bsha256: 9a1365c42f4aca3e9c1c5dcf38b967b73ab56e4af0b4a4380af7e2bf185478bcsha512: 5e9bb40b47c3a1a036ede25b3d1b7bbb4da2f048145fa1f3aaeccca11df88c108429b5bb859ab6da888c9e8ee6da2b1040d7341426e5776dbf5c3fa8ab9dd90fssdeep: 49152:HukzsCYr5TZNnFiL/FUEA0x2YBp4j8VThthc48Lezv:Ok4CwJsL/HAFYBp4jMM48Letype: MS-DOS executable, MZ for MS-DOSVersion Info:
0: [No Data]
Trojan:Win32/Wacatac.D!ml also known as:
| GridinSoft | Trojan.Ransom.Gen |
| Bkav | W32.AIDetectVM.malware |
| MicroWorld-eScan | Dropped:Trojan.GenericKD.32937697 |
| FireEye | Generic.mg.01a9b1f9a9db526a |
| CAT-QuickHeal | Trojan.Agent |
| ALYac | Trojan.Ransom.Satan |
| Cylance | Unsafe |
| AegisLab | Trojan.Win32.Eb.4!c |
| Sangfor | Malware |
| K7AntiVirus | Trojan ( 004f40381 ) |
| BitDefender | Dropped:Trojan.GenericKD.32937697 |
| K7GW | Trojan ( 004f40381 ) |
| Cybereason | malicious.5a9ee5 |
| TrendMicro | TROJ_GEN.R002C0WAD20 |
| BitDefenderTheta | Gen:NN.ZexaF.34082.koqaaevOgYoi |
| Symantec | Trojan.Gen.2 |
| ESET-NOD32 | a variant of Win64/Riskware.Mimikatz.B |
| TrendMicro-HouseCall | TROJ_GEN.R002C0WAD20 |
| Avast | Win32:Malware-gen |
| GData | Dropped:Trojan.GenericKD.32937697 |
| Kaspersky | Trojan.Win32.Eb.acs |
| Alibaba | Trojan:Win32/Mimikatz.f53cba30 |
| APEX | Malicious |
| Rising | Trojan.Eb!8.10DCC (CLOUD) |
| Ad-Aware | Dropped:Trojan.GenericKD.32937697 |
| Sophos | Mal/Generic-S |
| F-Secure | Trojan.TR/Crypt.XPACK.Gen |
| DrWeb | BackDoor.Siggen2.2089 |
| Invincea | heuristic |
| McAfee-GW-Edition | BehavesLike.Win32.VTFlooder.vc |
| CMC | Virus.Win32.Sality!O |
| Emsisoft | Dropped:Trojan.GenericKD.32937697 (B) |
| SentinelOne | DFI – Malicious PE |
| Cyren | W32/Trojan.CHUK-0891 |
| Jiangmin | Trojan.Crypmod.vn |
| Avira | TR/Crypt.XPACK.Gen |
| MAX | malware (ai score=85) |
| Endgame | malicious (high confidence) |
| Arcabit | Trojan.Generic.D1F696E1 |
| ZoneAlarm | Trojan.Win32.Eb.acs |
| Microsoft | Trojan:Win32/Wacatac.D!ml |
| Acronis | suspicious |
| McAfee | Artemis!01A9B1F9A9DB |
| VBA32 | Trojan.Eb |
| Malwarebytes | Trojan.MalPack.MPRESS |
| Panda | Trj/CI.A |
| Tencent | Win32.Trojan.Eb.Eer |
| Fortinet | Riskware/Mimikatz |
| AVG | Win32:Malware-gen |
| Paloalto | generic.ml |
| CrowdStrike | win/malicious_confidence_100% (W) |
| Qihoo-360 | Win32/Trojan.113 |
How to remove Trojan:Win32/Wacatac.D!ml virus?
Unwanted application has ofter come with other viruses and spyware. This threats can steal account credentials, or crypt your documents for ransom.
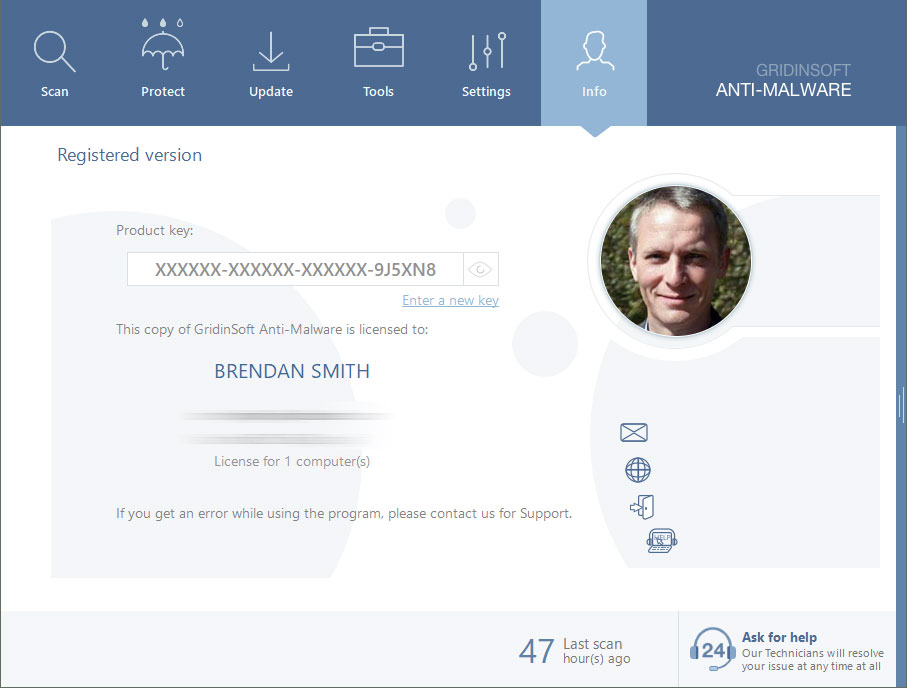
Reasons why I would recommend GridinSoft1
The is an excellent way to deal with recognizing and removing threats – using Gridinsoft Anti-Malware. This program will scan your PC, find and neutralize all suspicious processes.2.
Download GridinSoft Anti-Malware.
You can download GridinSoft Anti-Malware by clicking the button below:
Run the setup file.
When the setup file has finished downloading, double-click on the install-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about to allow GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for Trojan:Win32/Wacatac.D!ml files and other malicious programs. This process can take 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in the right corner.

Are Your Protected?
GridinSoft Anti-Malware will scan and clean your PC for free in the trial period. The free version offer real-time protection for first 2 days. If you want to be fully protected at all times – I can recommended you to purchase a full version:
If the guide doesn’t help you to remove Trojan:Win32/Wacatac.D!ml, you can always ask me in the comments to get help.
User Review
( votes)References
- GridinSoft Anti-Malware Review from HowToFix site: https://howtofix.guide/gridinsoft-anti-malware/
- More information about GridinSoft products: https://gridinsoft.com/comparison