Prime Stealer is a sophisticated cyber threat that stealthily infiltrates systems through deceptive emails, malicious websites, and compromised downloads. It specializes in harvesting a wide array of sensitive data, including browser and cryptocurrency details and Discord information.
Its ability to adapt and avoid detection and its persistence techniques make it a formidable and dangerous malware in today’s digital landscape.
Prime Stealer Overview
Prime is malware that is designed to steal sensitive information from Windows users. It adeptly extracts a wide range of data, such as browser history, cryptocurrency details, Discord data, system information, and more. This nefarious information stealer severely threatens the security and privacy of those it targets.
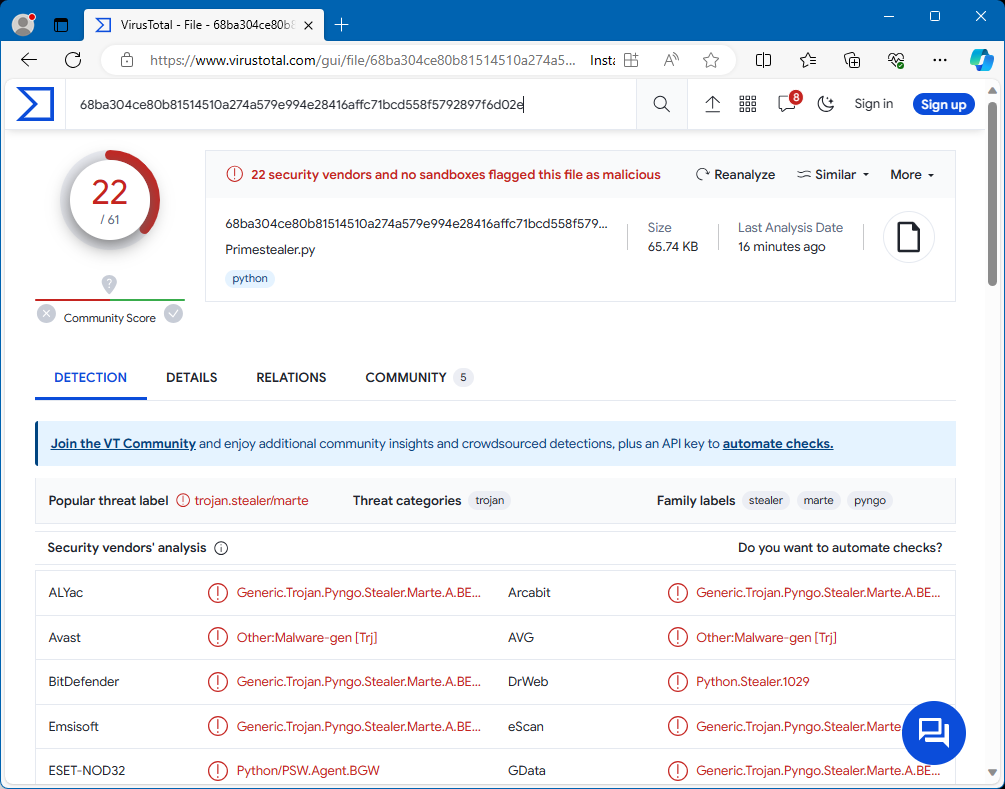
Prime Stealer detections on VirusTotal
| Name | Prime information stealer |
| Threat Type | Information stealer |
| Detection | Trojan:Python/Multiverze (Microsoft) |
| Damage | Stolen passwords and banking information, identity theft, the victim’s computer added to a botnet. |
| Similar Behaviror | Enigma Stealer, S1deload Stealer |
Technical Analysis
Prime stealer primarily targets Discord, gathering sensitive details, including Nitro subscription status, badges, billing information, email addresses, phone numbers, and a comprehensive list of friends on the platform. It also mines user’s browser data, extracting cookies, saved passwords, and specific information from popular platforms like Roblox. This is done across Chrome, Edge, Brave, Opera GX, and other browsers.
In the cryptocurrency sphere, Prime infiltrates and extracts information from browser extensions such as MetaMask, Phantom, Trust Wallet, Coinbase Wallet, and Binance Wallet, targeting cryptocurrency-related data. It also targets specific cryptocurrency software applications, including Exodus Wallet and Atomic Wallet. Prime’s capabilities extend to Application Data, infiltrating and extracting details from platforms like Steam, Riot Games, Telegram, and Discord. Discord injection uses a technique to actively intercept and send tokens, passwords, and email information during various user actions like logging in or modifying account details.
For System Information, Prime gathers user-specific details, system specifications, disk information, and network configuration and employs anti-debugging measures to operate undetected. To avoid detection, Prime checks if it’s running in a VirusTotal sandbox environment and adapts to evade analysis. Finally, Prime ensures its persistence in the compromised system. It places a stub in the AppData directory. It adds entries to the startup registry, enabling it to persist through system reboots.
Spreading Methods
Cyber attackers frequently use seemingly legitimate emails to lure users into clicking on links or downloading attachments that secretly contain malware. When opened, these attachments exploit software vulnerabilities or execute harmful scripts, resulting in malware, like Prime, infiltrating the user’s system.
Malware often also spreads through malicious websites and online ads. Users might accidentally visit compromised websites or click on deceptive ads that appear legitimate. Additionally, using pirated software, engaging in P2P networks, neglecting software updates, and connecting infected USB drives are common ways computers get infected.


Leave a Comment