Win32:Malware-gen is a detection used by AVG or Avast Antivirus software to identify malicious files. The antivirus uses various methods to determine if a file is harmful, including comparing its contents to a database of known threats and analyzing its behavior or structure.
Win32:Malware-gen may include Trojans, viruses, and worms. It is difficult to remove because it is often new and evolving, causing various computer problems. Antivirus may identify a file as Win32:Malware-gen if it seems suspicious but doesn’t match any known threat. It means a 32-bit file on your Windows PC could be harmful. It might be a false positive, but the flagged file is usually a virus.
Typically, Win32:Malware-gen is a Trojan Horse that can carry out various tasks, including:
- Downloading, installing, or running malware on the targeted computer.
- Operating as a keylogger to collect sensitive data such as logins, passwords, and credit card information.
- Enabling remote access to the affected computer.
- Displaying aggressive pop-ups, banners, in-text ads, and other forms of advertising that are irritating and potentially malicious.
How to remove the Win32:Malware-gen from my PC?
Manual Win32:Malware-gen Removal
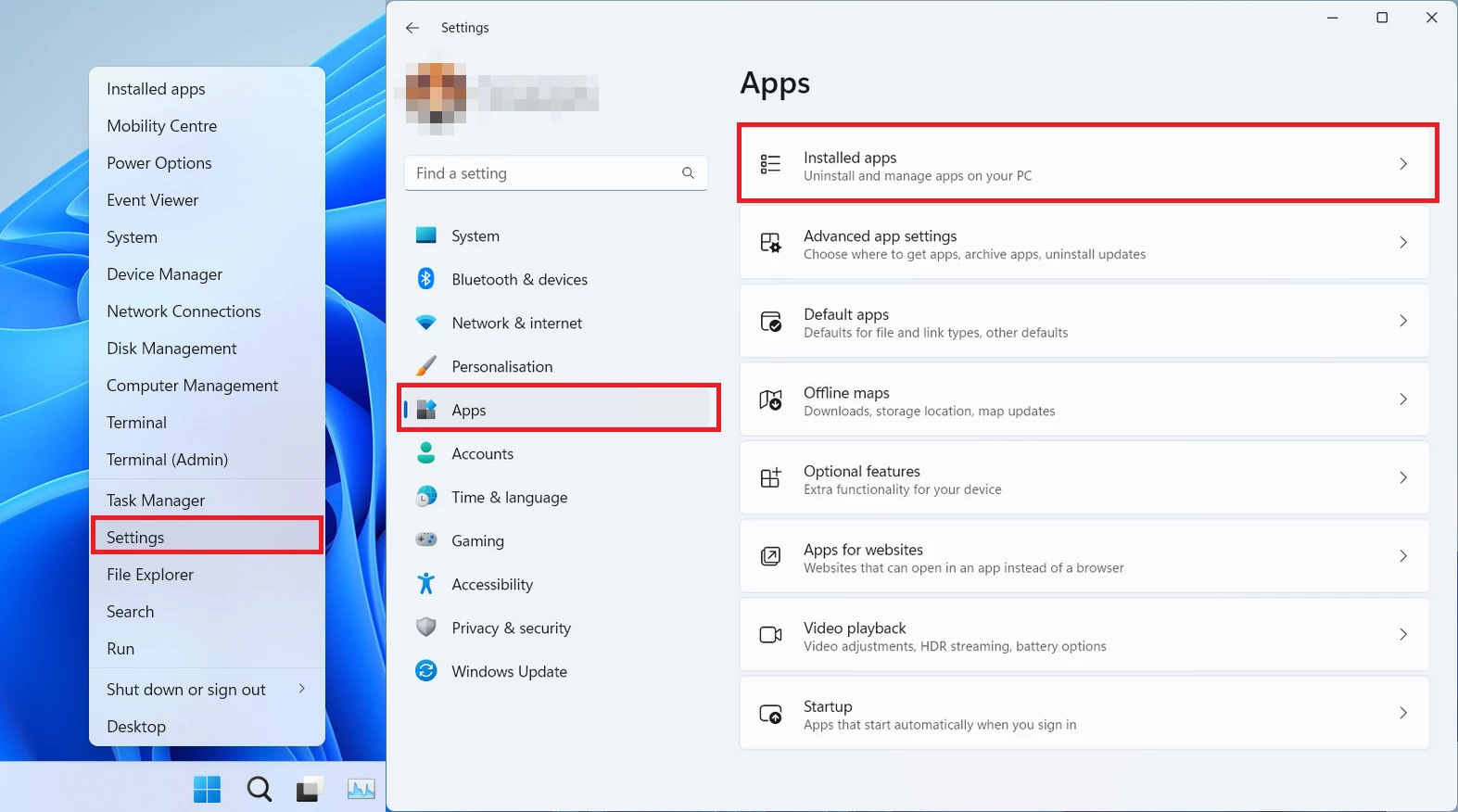
You can remove related app manually, through the system Settings app. Click the Windows button with the right mouse button and find Settings in the appeared list. In Settings, go to Apps → Installed Apps menu.
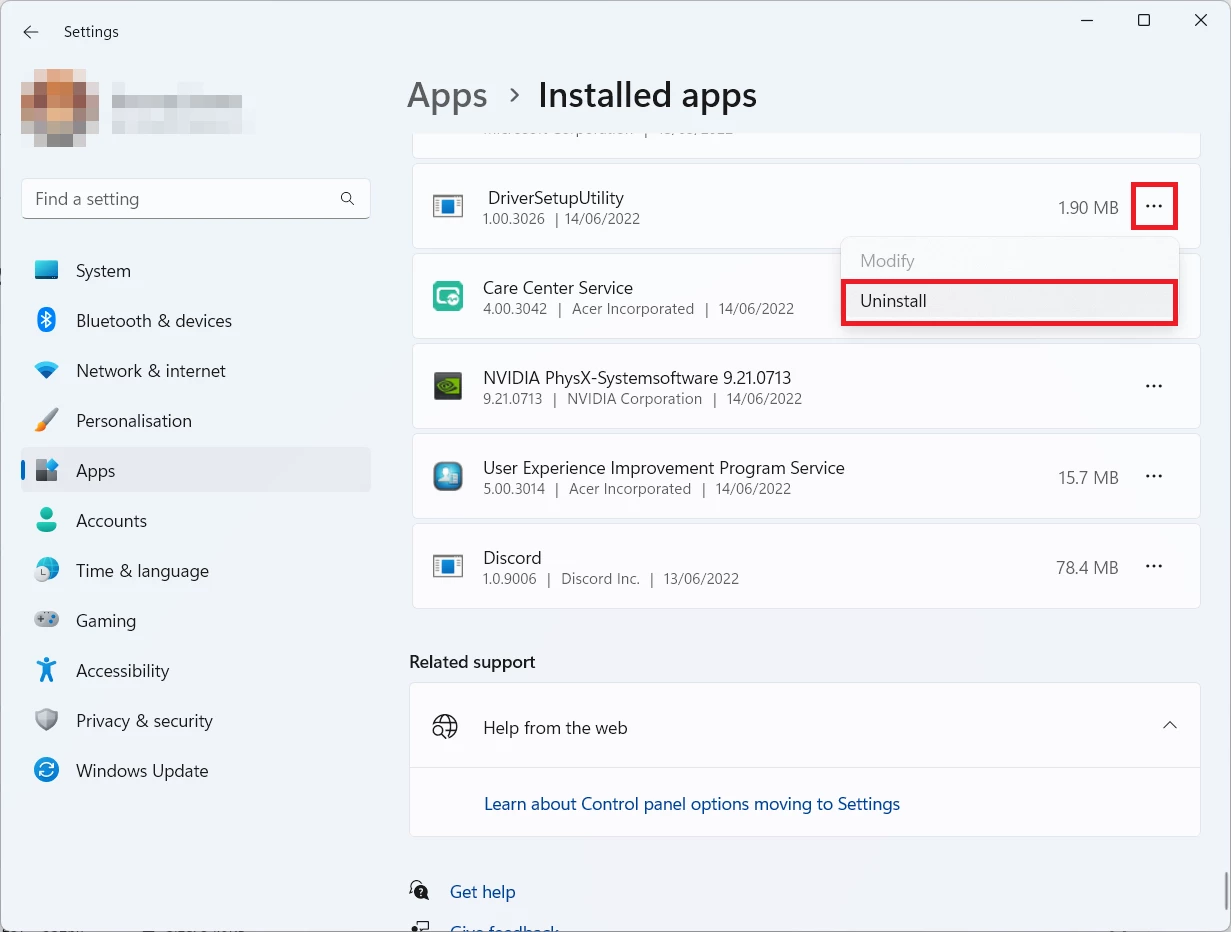
There, find the apps you do not remember installing. If you know a specific one that Avast/AVG is complaining on with the Win32:Malware-gen detection, seek for them. Click the three-dot symbol to the right, and then choose “Uninstall”.
Reset your browser settings
You may see the list of options for each browser. By default, they are set up in a manner that fits the majority of users. Press the “Reset” button (lower right corner). In a minute your browser will be as good as new.
Reset your browsers manually
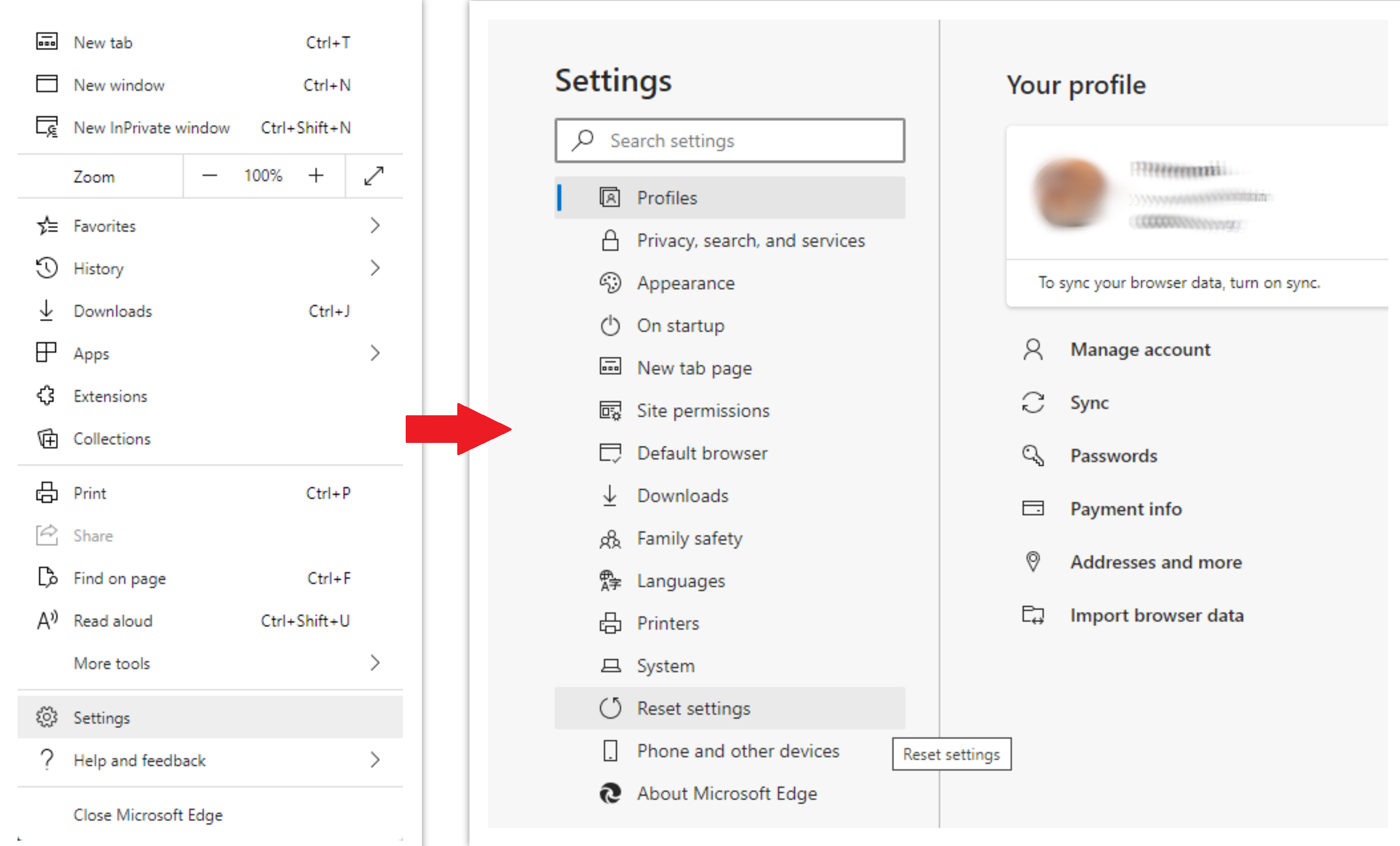
To reset Edge, do the following steps:
- Open “Settings and more” tab in upper right corner, then find here “Settings” button. In the appeared menu, choose “Reset settings” option:
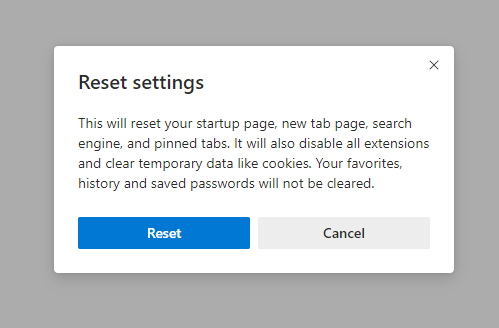
- After picking the Reset Settings option, you will see the following menu, stating about the settings which will be reverted to original:
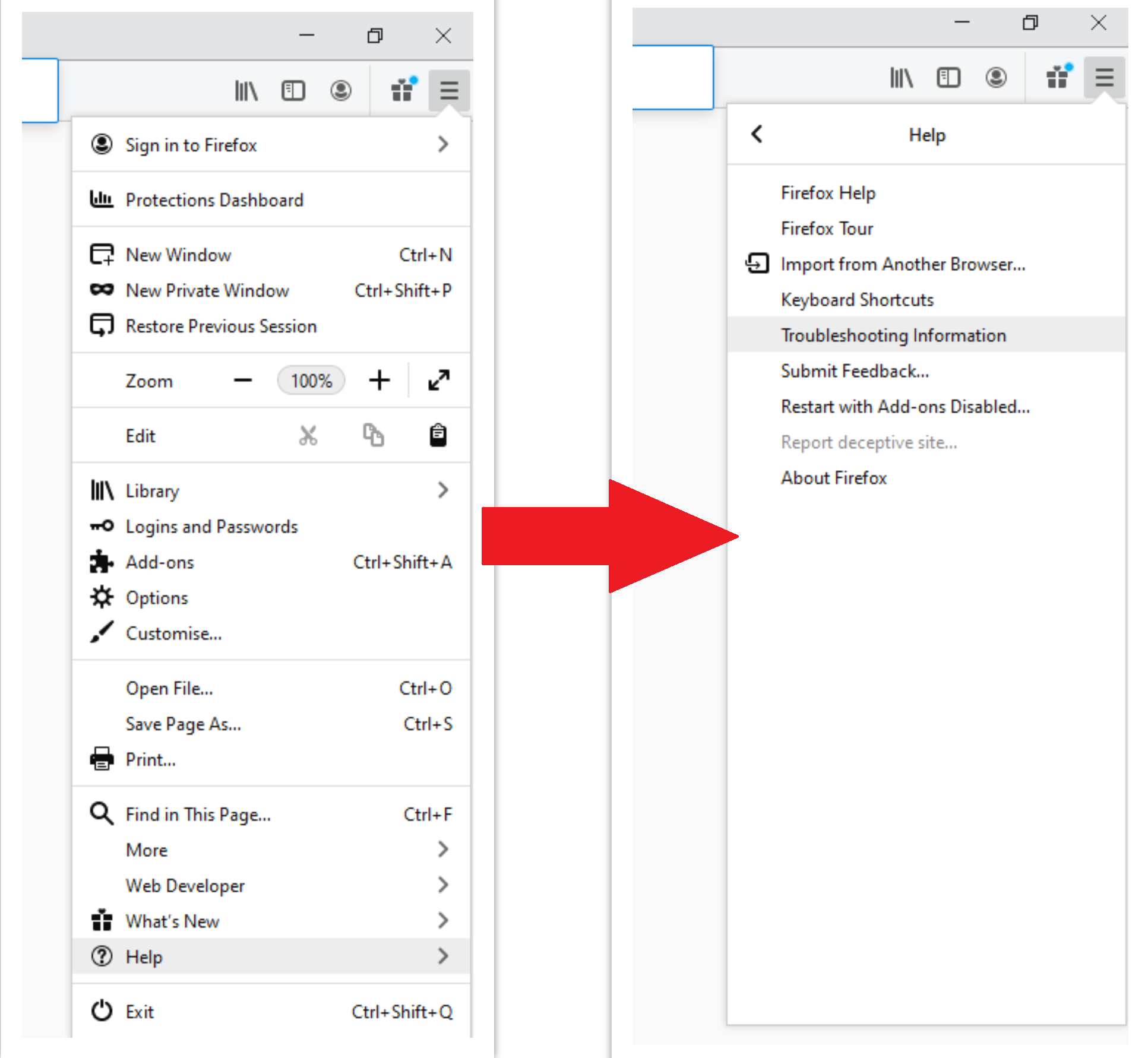
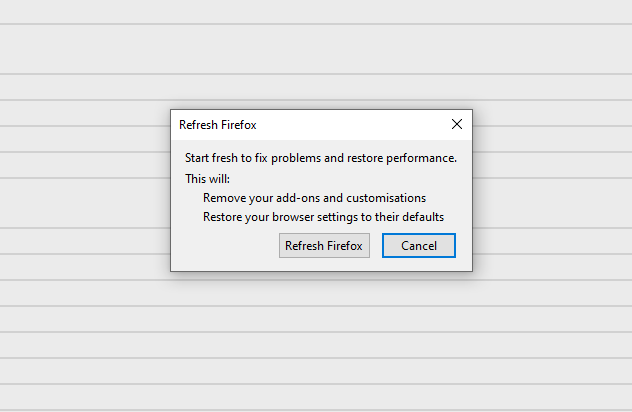
For Mozilla Firefox, do the next actions:
- Open Menu tab (three strips in upper right corner) and click the “Help” button. In the appeared menu choose “troubleshooting information”:
- In the next screen, find the “Refresh Firefox” option:
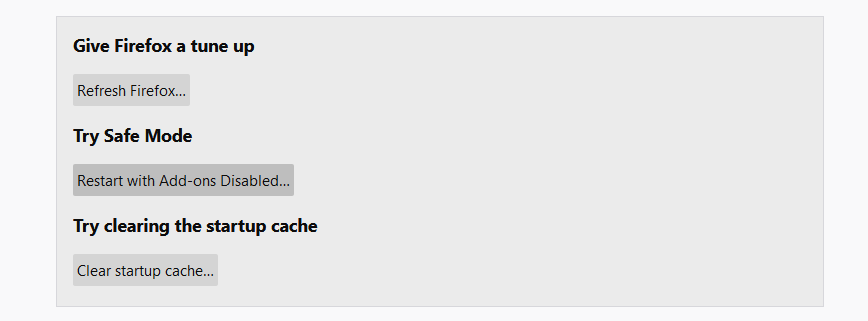
After choosing this option, you will see the next message:
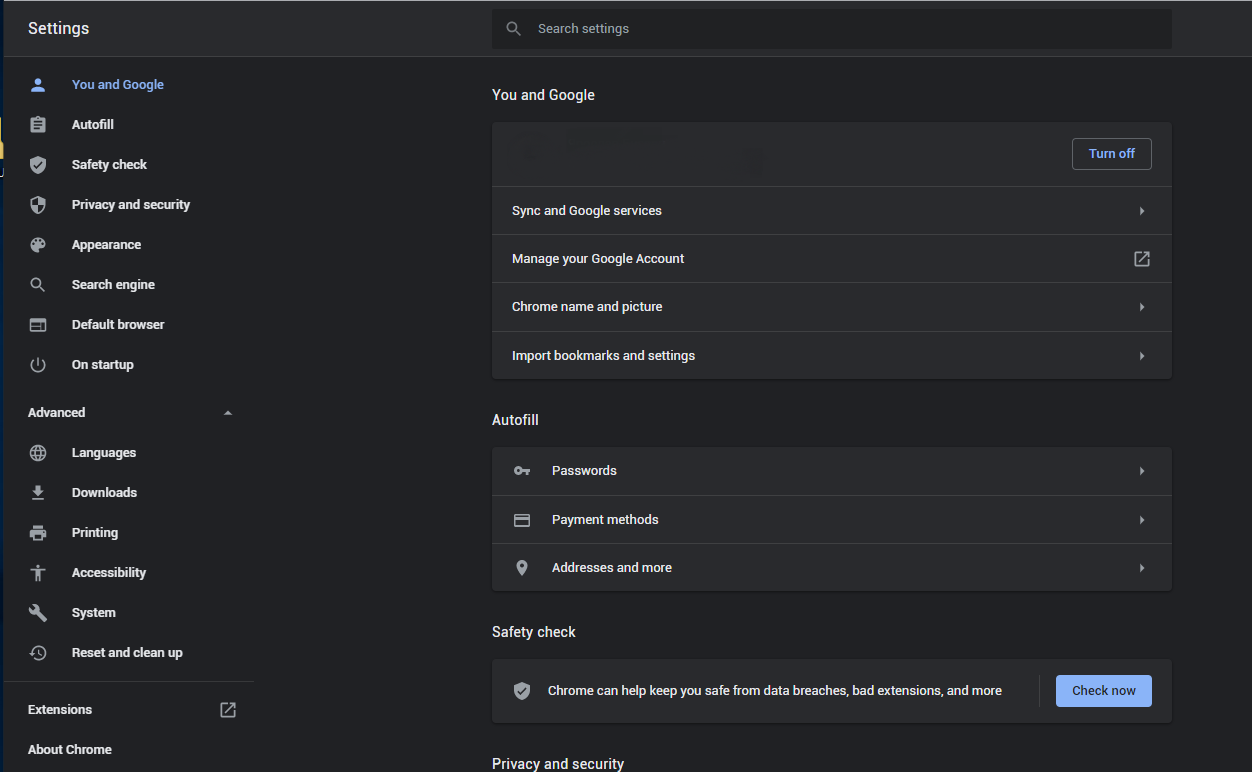
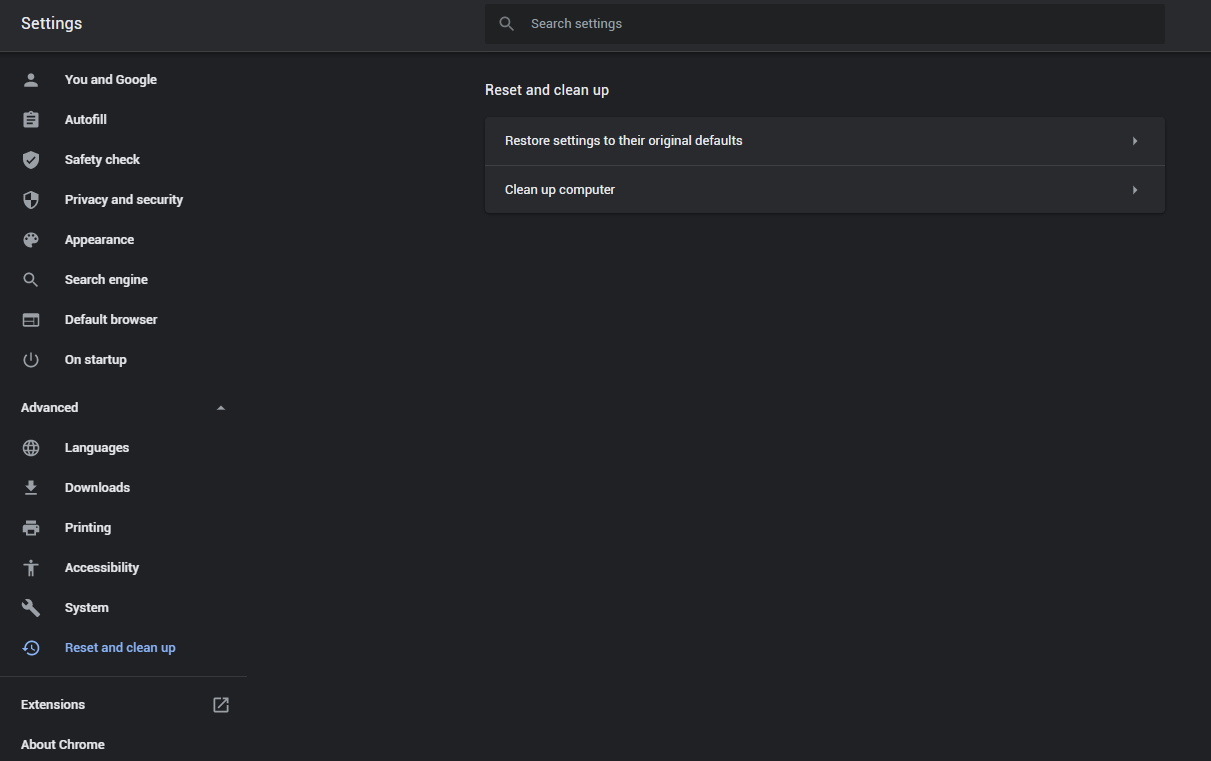
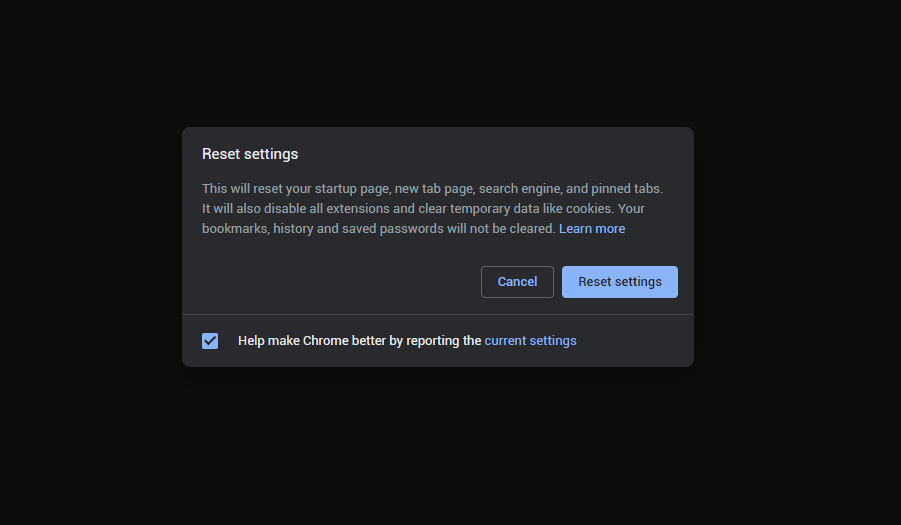
If you use Google Chrome
- Open Settings tab, find the “Advanced” button. In the extended tab choose the “Reset and clean up” button:
- In the appeared list, click on the “Restore settings to their original defaults”:
- Finally, you will see the window, where you can see all the settings which will be reset to default:
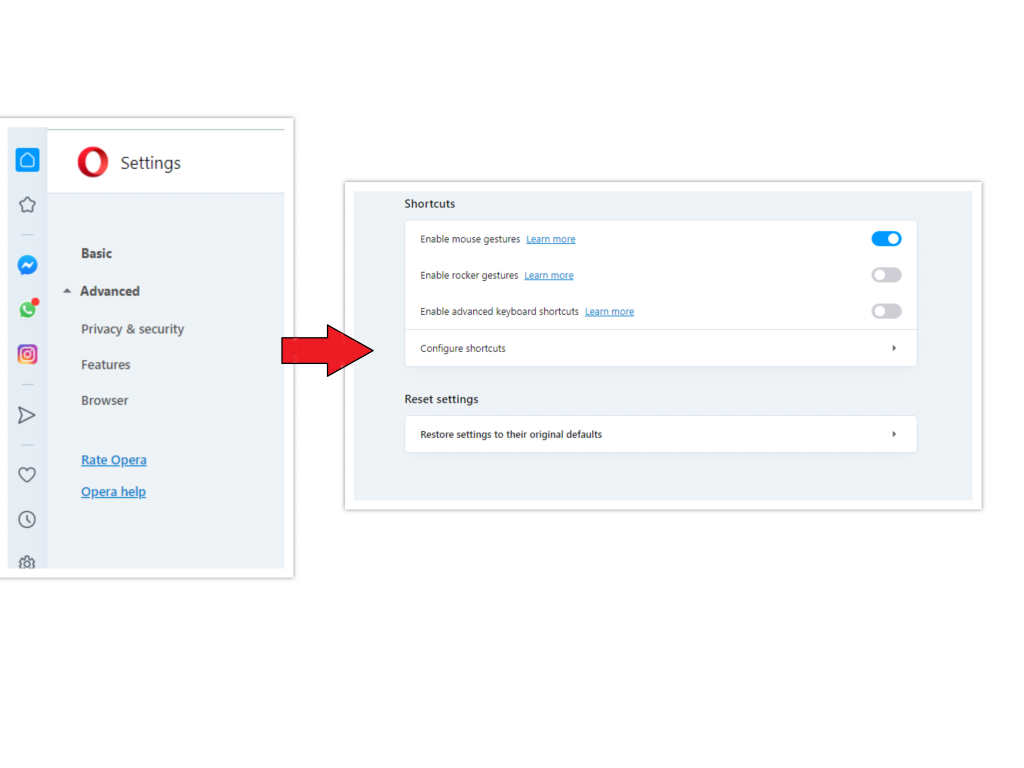
Opera can be reset in the next way
- Open Settings menu by pressing the gear icon in the toolbar (left side of the browser window), then click “Advanced” option, and choose “Browser” button in the drop-down list. Scroll down, to the bottom of the settings menu. Find there “Restore settings to their original defaults” option:
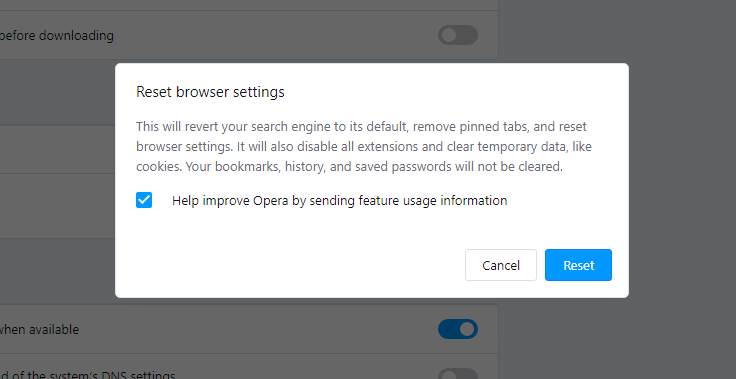
- After clicking the “Restore settings…” button, you will see the window, where all settings, which will be reset, are shown:
When the browsers are reset, you need to ensure that your browser will connect the right DNS while connecting to the web page you need. Create a text file titled “hosts” on your pc’s desktop, then open it and fill it with the following lines1:
# Copyright (c) 1993-2006 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# localhost name resolution is handle within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
Frequently Asked Questions about Win32:Malware-gen
Another detections from Avast & AVG
- Posts not found
References
- Official Microsoft guide for hosts file reset.


Leave a Comment