The Trojan:Win32/RedLine.MB!MTB alert is detected by Microsoft Defender’s machine learning system. It identifies a malicious program that aims at various unwanted operations within your computer.
Trojan:Win32/RedLine.MB!MTB activity usually results in losing access to your social media accounts and exposing your identity. Moreover, some samples are also able to deliver other malware to the system. Don’t ignore these alerts and take action to protect your computer from harm.
Spyware Summary:
| Name | Redline Spyware |
| Detection | Trojan:Win32/RedLine.MB!MTB |
| Damage | Steal personal data contained in the attacked system. |
| Similar | Trojan:MSIL/Redline.RA!MTB |
| Fix Tool | See If Your System Has Been Affected by Redline Spyware |
How to remove the Trojan:Win32/RedLine.MB!MTB from my PC?
While manual removal of the threat is technically possible, I strongly discourage this method. In its pursuit of establishing persistence, Malware generates numerous instances of itself, making it exceedingly difficult to trace all its components manually. Consequently, manual removal can be time-consuming and often yield minimal to no results. Below, I have assembled a guide outlining the most effective removal practices for Trojan:Win32/RedLine.
Manual Trojan:Win32/RedLine.MB!MTB Removal
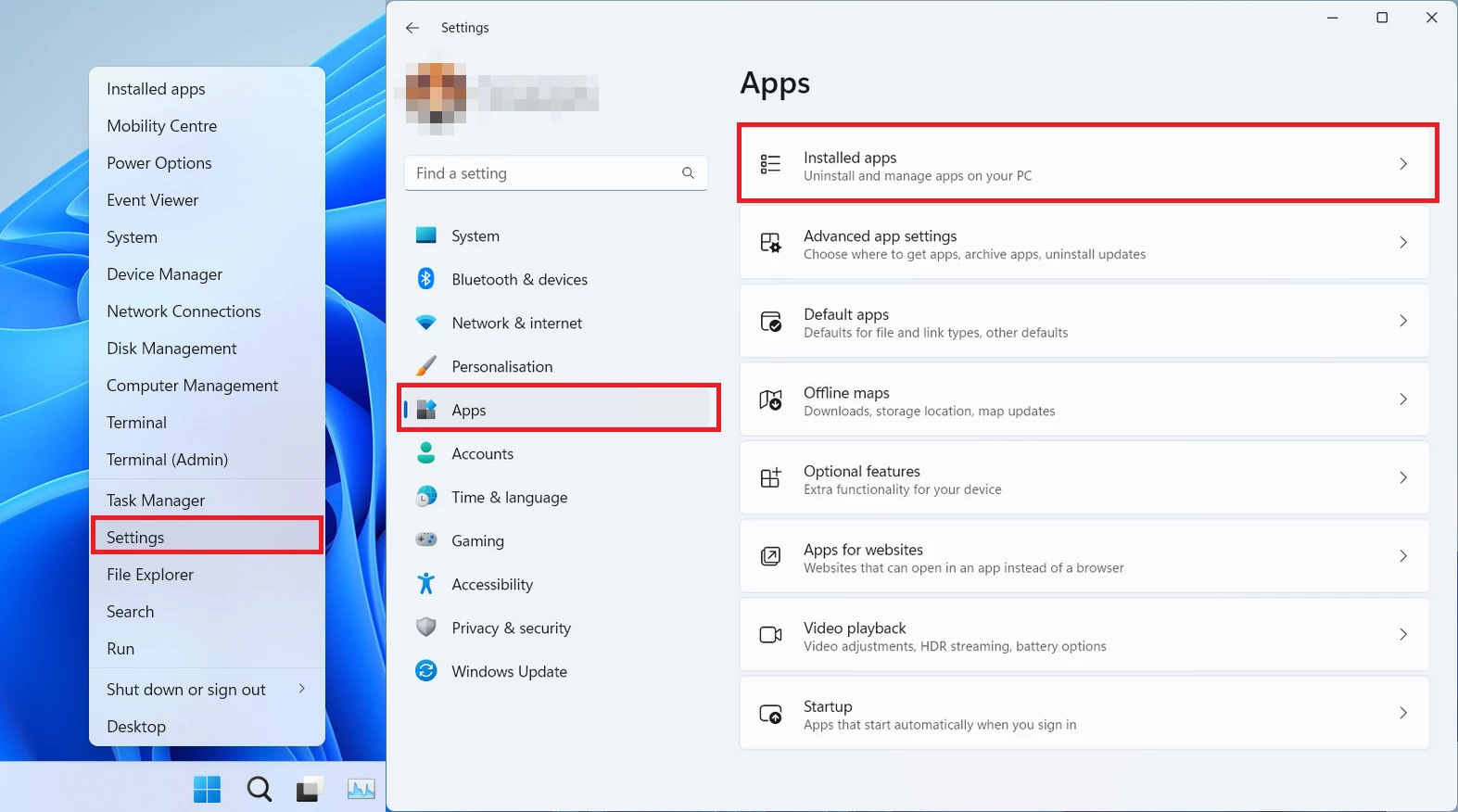
You can remove Trojan:Win32/RedLine.MB!MTB manually, through the system Settings app. Click the Windows button with the right mouse button and find Settings in the appeared list. In Settings, go to Apps → Installed Apps menu.
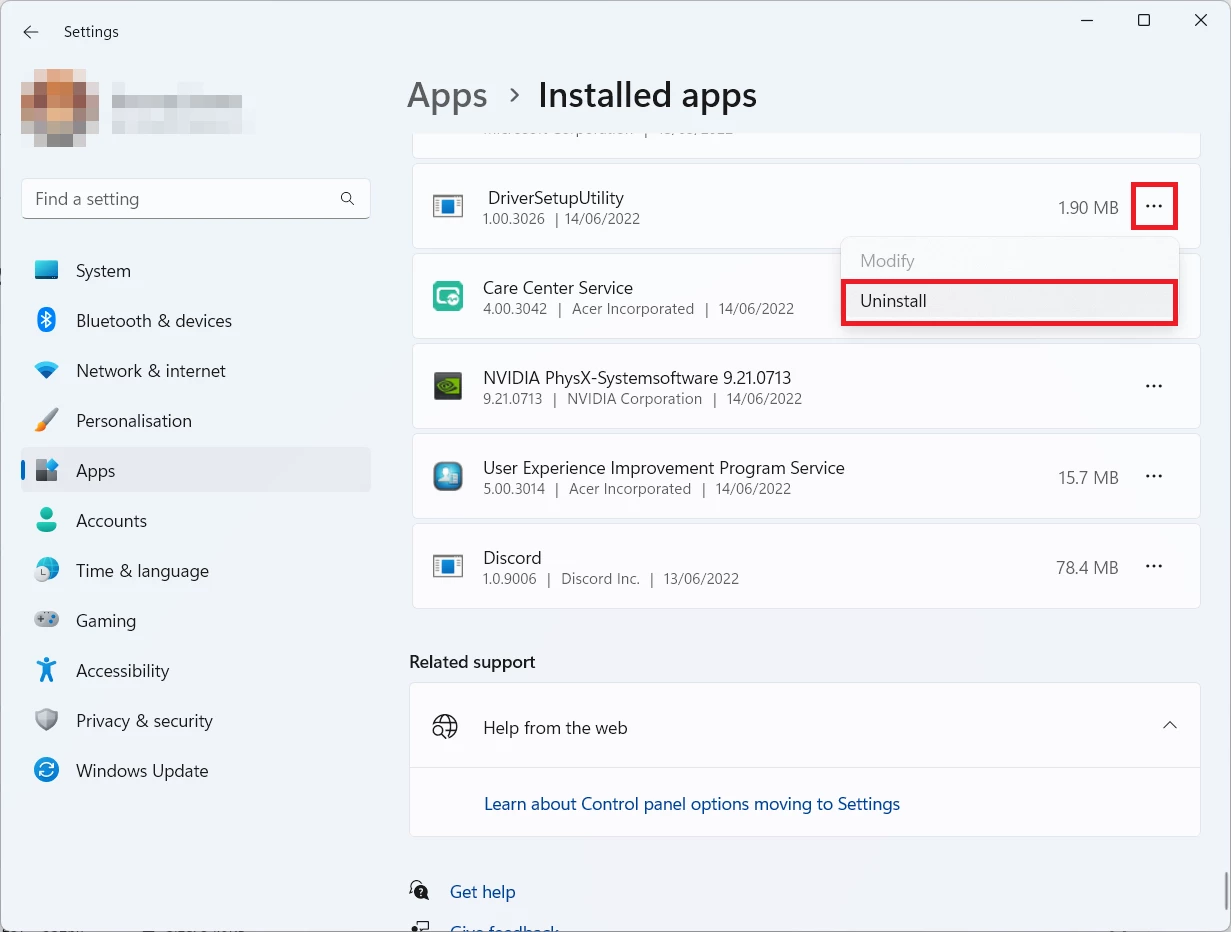
There, find the apps you do not remember installing. If you know a specific one that Avast/AVG is complaining on with the Win32/Uwamson detection, seek for them. Click the three-dot symbol to the right, and then choose “Uninstall”.
Reset your browser settings
You may see the list of options for each browser. By default, they are set up in a manner that fits the majority of users. Press the “Reset” button (lower right corner). In a minute your browser will be as good as new.
Reset your browsers manually
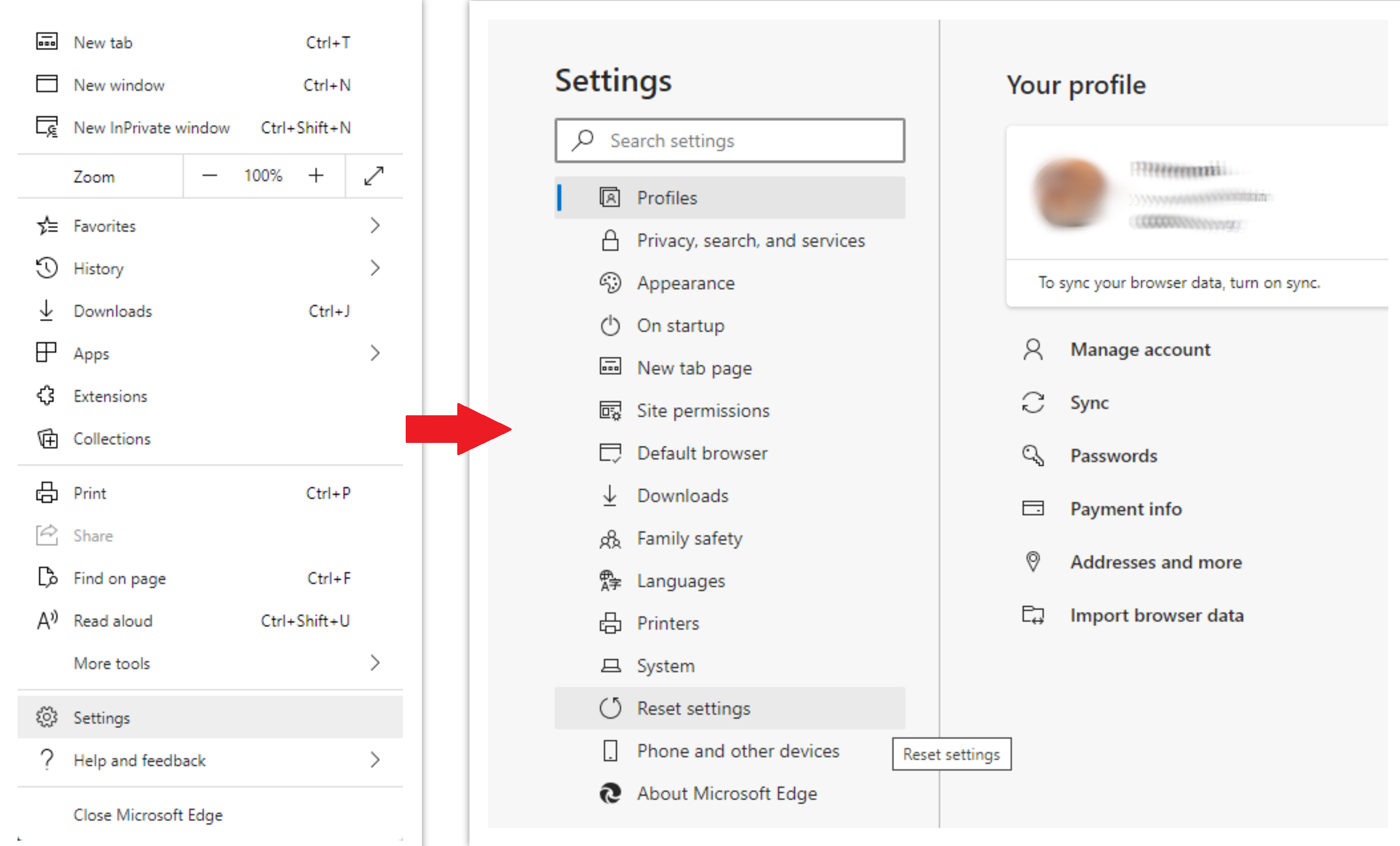
To reset Edge, do the following steps:
- Open the “Settings and more” tab in the upper right corner, then find here “Settings” button. In the appeared menu, choose the “Reset settings” option:
- After picking the Reset Settings option, you will see the following menu, stating the settings which will be reverted to the original:
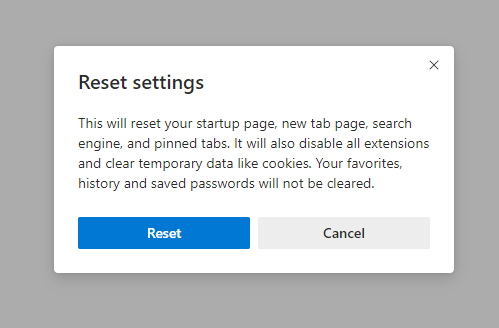
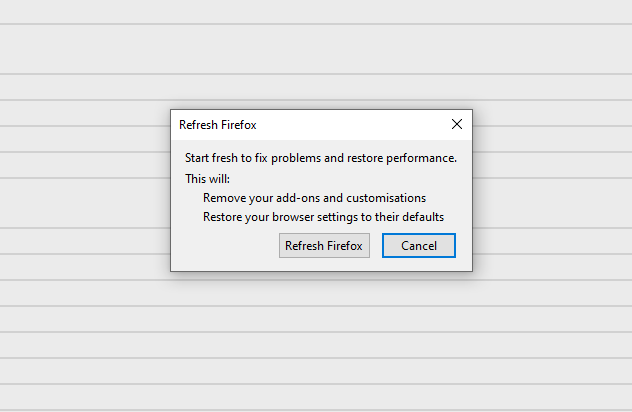
For Mozilla Firefox, do the next actions:
- Open the Menu tab (three strips in the upper right corner) and click the “Help” button. In the appeared menu choose “Troubleshooting information”:
- In the next screen, find the “Refresh Firefox” option:
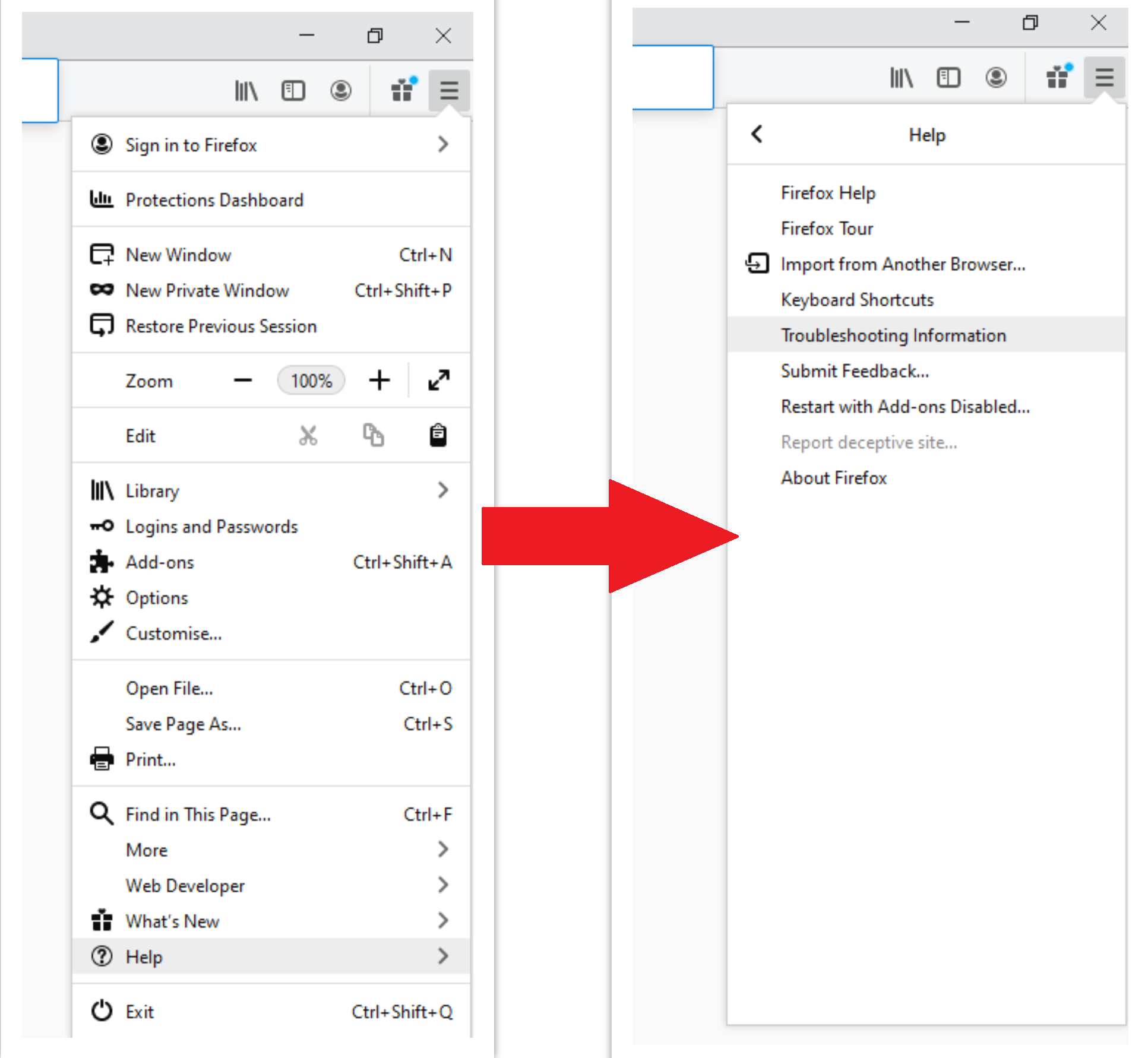
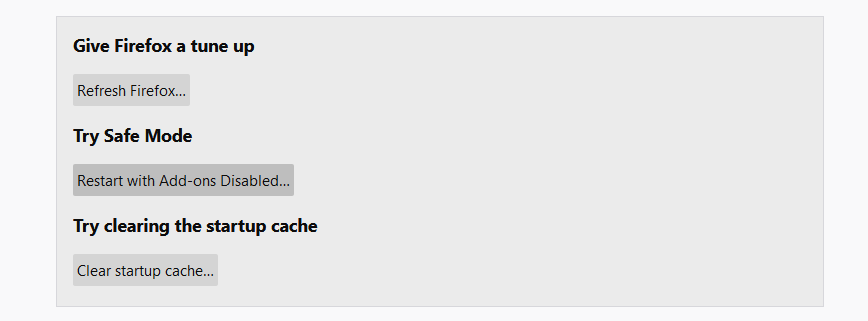
After choosing this option, you will see the next message:
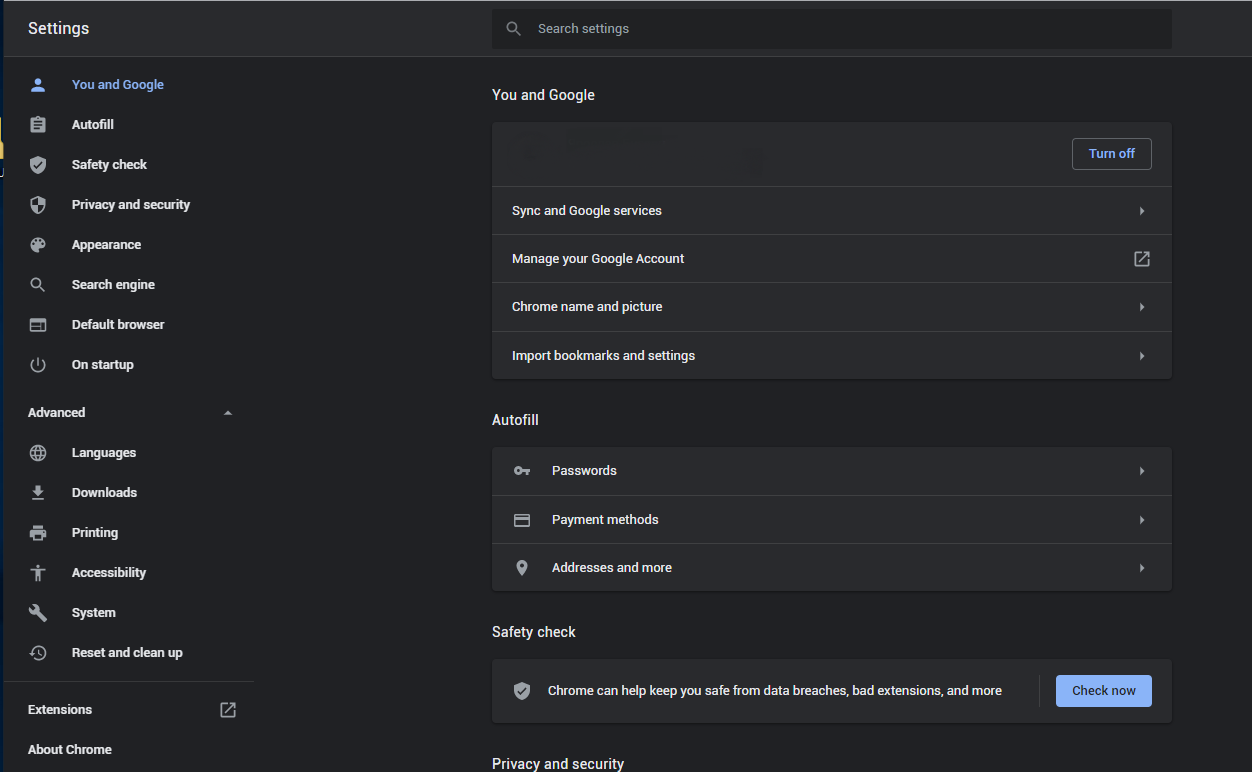
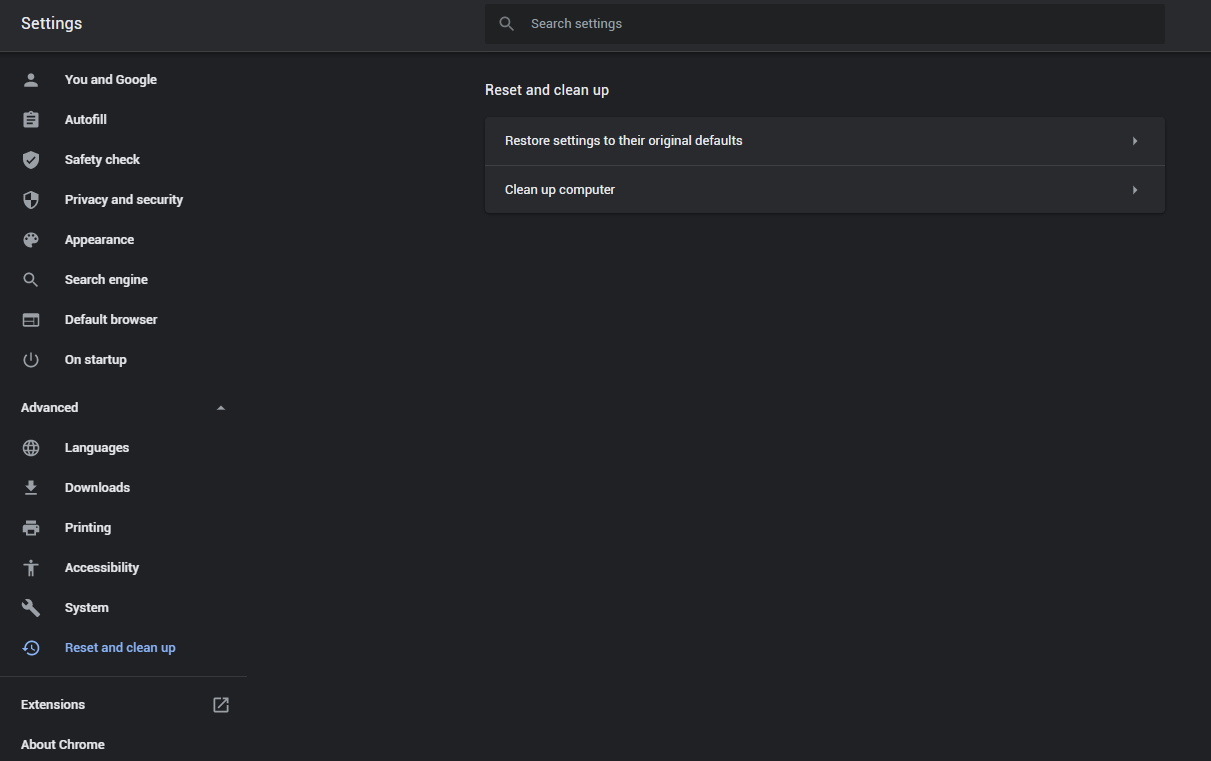
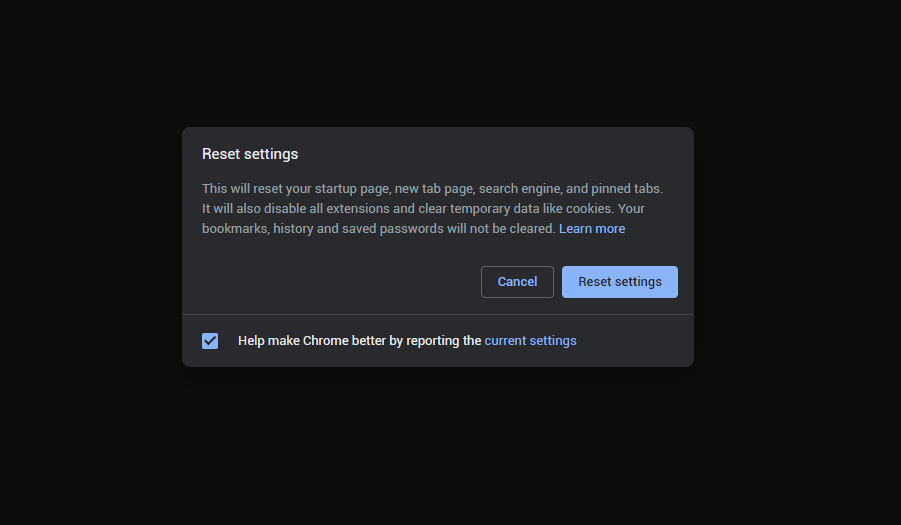
If you use Google Chrome
- Open the Settings tab, and find the “Advanced” button. In the extended tab choose the “Reset and clean up” button:
- In the appeared list, click on the “Restore settings to their original defaults”:
- Finally, you will see the window, where you can see all the settings which will be reset to default:
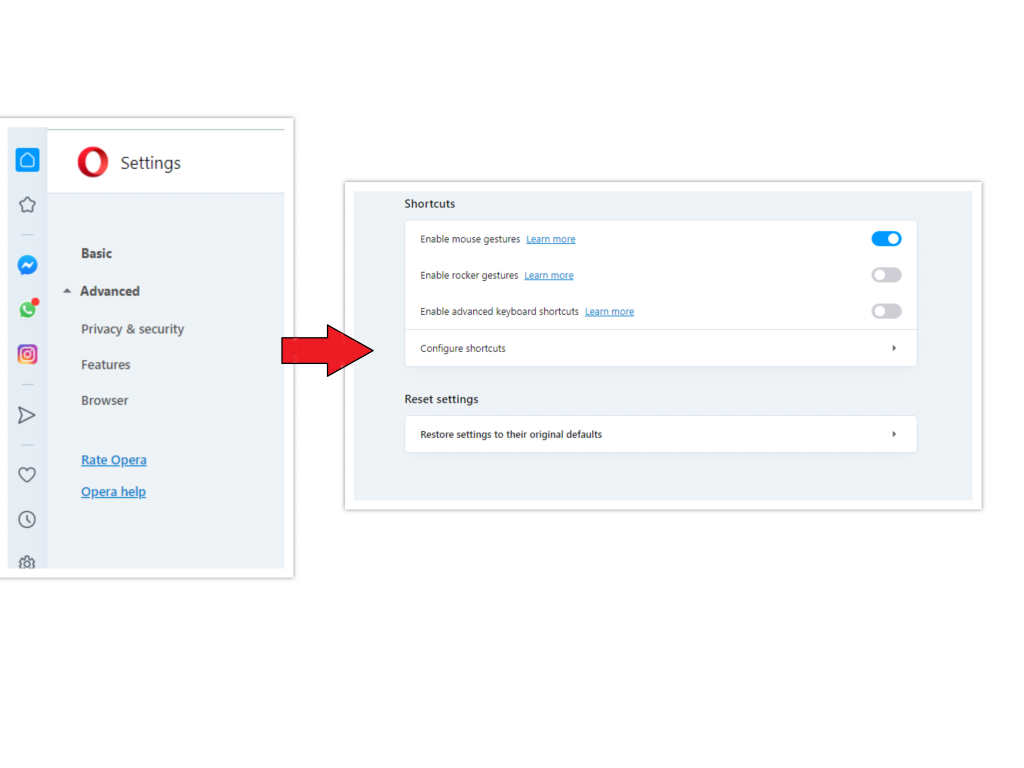
Opera can be reset in the next way
- Open the Settings menu by pressing the gear icon in the toolbar (left side of the browser window), then click the “Advanced” option, and choose the “Browser” button in the drop-down list. Scroll down, to the bottom of the settings menu. Find there “Restore settings to their original defaults” option:
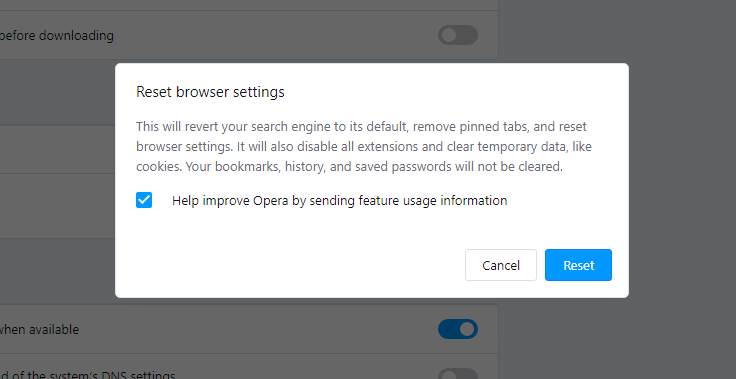
- After clicking the “Restore settings…” button, you will see the window, where all settings, which will be reset, are shown:
When the browsers are reset, you need to ensure that your browser will connect the right DNS while connecting to the web page you need. Create a text file titled “hosts” on your PC’s desktop, then open it and fill it with the following lines1:
# Copyright (c) 1993-2006 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# Localhost name resolution is handled within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
References
- Official Microsoft guide for hosts file reset.


no i dont download stuff now i got microsoft malware trojan red line 🙁