Trojan:Win32/Tiggre!rfn is a harmful malware strain that poses a significant threat to computer systems. Tiggre Trojan is designed to infiltrate and compromise Windows-based systems, enabling unauthorized access and control for malicious actors.
The primary danger of Trojan:Win32/Tiggre!rfn lies in its ability to serve as a backdoor, allowing attackers to remotely control the compromised system, execute commands, and potentially steal sensitive data. It might also act as a dropper, downloading and installing additional malicious payloads onto the infected system. Due to its dynamic and evolving nature, this threat may change its behavior over time to bypass security measures and maintain its effectiveness.
Trojan:Win32/Tiggre!rfn Overview
The Trojan:Win32/Tiggre!rfn malware is a versatile threat that carries out various functions based on the choices made by its developers. One of its capabilities is the unauthorized use of system resources to mine cryptocurrencies. This process involves solving mathematical equations, with mining tools utilizing the computer’s power for these calculations.
Each time an equation is solved, a unit of currency (such as 1 Bitcoin) is successfully mined. Since multiple computers work on the same equation simultaneously, the resulting reward is divided among them based on their computing power and contribution. However, all the revenue goes into the cyber criminals’ crypto wallet, leaving users with no share of the profits.
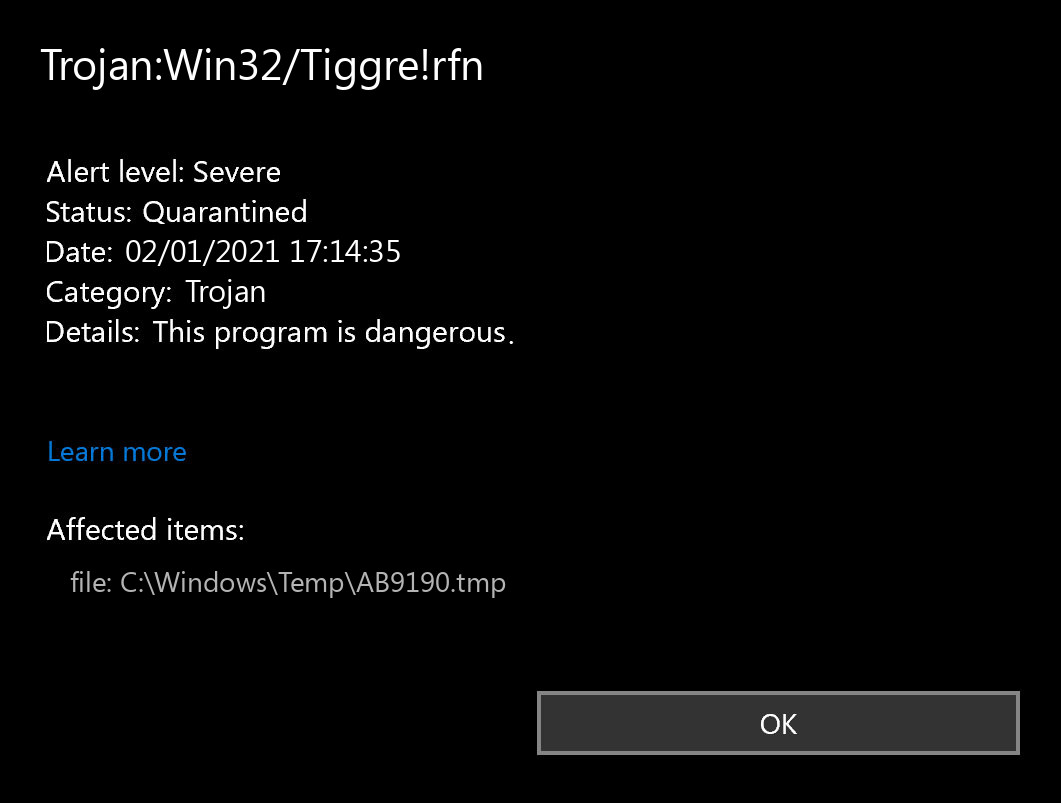
Trojan:Win32/Tiggre!rfn Virus Detection
It is important to note that all of this takes place without the users’ consent. As the mining activity consumes up to 100% of the computer’s resources, systems often become unstable and practically unusable. Moreover, under certain conditions like high room temperatures or poor cooling systems, hardware components may overheat and get damaged.
In addition to its crypto-mining capabilities, the Trojan Tiggre rfn also collects various types of data, including saved logins/passwords, keystrokes, and banking information, among others.
The collected data is often exploited for financial gain. Consequently, the presence of malware like the Trojan:Win32/Tiggre!rfn can result in significant financial and privacy issues. Cybercriminals can transfer funds to their accounts or engage in illegal activities using the victims’ identities.
In some instances, the Trojan:Win32/Tiggre!rfn infiltrates systems alongside adware-type applications. While not as harmful as the Trojan, these programs can be frustrating and troublesome. Adware-type apps are known for displaying intrusive advertisements and gathering sensitive data.
Intrusive ads cover up the underlying content of websites, greatly diminishing the browsing experience. Additionally, they can redirect users to malicious sites and secretly download and install malware through scripts. Clicking on these ads may lead to accessing harmful websites.
Furthermore, adware collects information such as IP addresses, visited URLs, search queries, and viewed pages, which is then shared with third parties, potentially including cybercriminals. As a result, adware poses a threat to both your privacy and your safety while browsing the internet. Therefore, it is crucial to remove any adware-type apps immediately.
Trojan:Win32/Tiggre!rfn Tecnical Details
System Modifications:
- Executable code extraction. Cybercriminals often use binary packers to hinder the malicious code from being reverse-engineered by malware analysts. A packer is a tool that compresses, encrypts, and modifies a malicious file’s format. Sometimes packers can be used for legitimate ends, for example, to protect a program against cracking or copying.
- Creates RWX memory. There is a security trick with memory regions that allows an attacker to fill a buffer with a shellcode and then execute it. Filling a buffer with shellcode isn’t a big deal, it’s just data. The problem arises when the attacker can control the instruction pointer (EIP), usually by corrupting a function’s stack frame using a stack-based buffer overflow, and then changing the flow of execution by assigning this pointer to the address of the shellcode.
- A process created a hidden window;
- HTTP traffic contains suspicious features which may be indicative of malware-related traffic;
- Performs some HTTP requests;
- The binary likely contains encrypted or compressed data. In this case, encryption is a way of hiding virus code from antiviruses and virus analysts.
- Uses Windows utilities for basic functionality;
- Attempts to repeatedly call a single API many times to delay analysis time. This significantly complicates the work of the virus analyzer. Typical malware tactics!
- Steals private information from local Internet browsers;
- Collects information about installed applications;
- Checks the CPU name from the registry, possibly for anti-virtualization;
- Attempts to access Bitcoin/ALTCoin wallets;
- Harvests credentials from local FTP client software;
- Harvests information related to installed instant messenger clients;
- Harvests information related to installed mail clients;
- Collects information to fingerprint the system. There are behavioral human characteristics that can be used to digitally identify a person to grant access to systems, devices, or data. Unlike passwords and verification codes, fingerprints are fundamental parts of users’ identities. Among the threats blocked on biometric data processing and storage systems is spyware, the malware used in phishing attacks (mostly spyware downloaders and droppers), ransomware, and Banking Trojans as posing the greatest danger.
- Uses suspicious command line tools or Windows utilities;
- Ciphering the documents found on the sufferer’s disk drive — so the target can no longer utilize the data;
- Preventing routine access to the victim’s workstation. This is the typical behavior of a virus called locker. It blocks access to the computer until the victim pays the ransom.
File details:
File Info:
crc32: 1DF61B8Fmd5: 302a9c536d1a765bb588bce610af3491name: 5.exesha1: 65b8b35199f403a50c2bd0016c09925d98404a2bsha256: 703bf6e8c4f52d364eee5871e8047278e06d8fb9e0468688213adaf656be60c1sha512: 12f2a65f72c984c6eeedb4c82d6f24ffaa39f1abfa6d124754b74acc7006b37ff4072c03dbba31e8044b77027aaf09eea7163ee65cf3aad9c8193a643363ee4assdeep: 12288:q8JNH5Ppc4JKkV85TQvQ7qk6TgR7KXPl6DtAB2f8un49s1XipL:q45+4J9V85svQ7F6EdKXPl6DqHsMpLtype: PE32 executable (GUI) Intel 80386, for MS WindowsVersion Info:
0: [No Data]
Trojan:Win32/Tiggre!rfn also known as:
| MicroWorld-eScan | Trojan.GenericKD.32765695 |
| FireEye | Generic.mg.302a9c536d1a765b |
| CAT-QuickHeal | Ransom.Stop.MP4 |
| ALYac | Trojan.Chapak.A |
| Cylance | Unsafe |
| Sangfor | Malware |
| K7AntiVirus | Riskware ( 0040eff71 ) |
| BitDefender | Trojan.GenericKD.32765695 |
| K7GW | Riskware ( 0040eff71 ) |
| Cybereason | malicious.199f40 |
| BitDefenderTheta | Gen:NN.ZexaF.32515.JyW@aWHiY0h |
| F-Prot | W32/FakeAlert.5!Maximus |
| Symantec | ML.Attribute.HighConfidence |
| Paloalto | generic.ml |
| GData | Trojan.GenericKD.32765695 |
| Kaspersky | Trojan.Win32.Chapak.efwz |
| ViRobot | Trojan.Win32.Z.Wacatac.580608.B |
| AegisLab | Trojan.Win32.Chapak.4!c |
| Rising | [email protected] (RDMK:x5DceDlMt3lemCH+NRZzug) |
| Ad-Aware | Trojan.GenericKD.32765695 |
| Sophos | Mal/Generic-S |
| F-Secure | Trojan.TR/AD.VidarStealer.ceeq |
| DrWeb | Trojan.Siggen8.58154 |
| Invincea | heuristic |
| McAfee-GW-Edition | BehavesLike.Win32.Generic.hc |
| SentinelOne | DFI – Malicious PE |
| Trapmine | malicious.moderate.ml.score |
| APEX | Malicious |
| Cyren | W32/FakeAlert.5!Maximus |
| Jiangmin | Trojan.Cutwail.de |
| Webroot | W32.Trojan.Gen |
| Avira | TR/AD.VidarStealer.ceeq |
| Endgame | malicious (high confidence) |
| Arcabit | Trojan.Generic.D1F3F6FF |
| ZoneAlarm | Trojan.Win32.Chapak.efwz |
| Microsoft | Trojan:Win32/Tiggre!rfn |
| AhnLab-V3 | Trojan/Win32.RL_MalPe.R301428 |
| Acronis | suspicious |
| McAfee | Trojan-FRON!302A9C536D1A |
| MAX | malware (ai score=86) |
| Malwarebytes | Trojan.MalPack.GS |
| ESET-NOD32 | a variant of Win32/Kryptik.GYXK |
| Ikarus | Trojan.Win32.Crypt |
| Fortinet | W32/GenKryptik.DYVN!tr |
| AVG | FileRepMalware |
| CrowdStrike | win/malicious_confidence_90% (W) |
| Qihoo-360 | Win32/Trojan.443 |
How to remove Trojan:Win32/Tiggre!rfn?
Removing threats manually can be a complex and time-consuming task that demands advanced IT skills. To simplify the process and ensure effective malware removal, we recommend using Gridinsoft Anti-Malware, a professional automatic malware removal tool. By clicking the button below, you can easily download it:
Run the setup file.
When the setup file has finished downloading, double-click on the install-antimalware-fix.exe file to install GridinSoft Anti-Malware on your system.

An User Account Control asking you about allowing GridinSoft Anti-Malware to make changes to your device. So, you should click “Yes” to continue with the installation.

Press the “Install” button.

Once installed, Anti-Malware will automatically run.

Wait for the Anti-Malware scan to complete.
GridinSoft Anti-Malware will automatically start scanning your system for Tiggre!rfn files and other malicious programs. This process can take 20-30 minutes, so I suggest you periodically check on the status of the scan process.

Click on “Clean Now”.
When the scan has finished, you will see the list of infections that GridinSoft Anti-Malware has detected. To remove them click on the “Clean Now” button in the right corner.

FAQ
Trojan Tiggre is a type of versatile malware that performs various functions depending on the choices made by its developers. It can misuse system resources for cryptocurrency mining and gather sensitive data from infected computers.
Through spam emails containing malicious attachments, fake Flash Player updaters, and by visiting malicious websites. It can also be spread through “chain-infecting” methods and through scripts sent via Facebook.
Unauthorized usage of system resources for cryptocurrency mining, potential damage to hardware components due to increased resource consumption, loss of sensitive data (such as logins, passwords, and banking information), and the possibility of financial and privacy issues caused by cyber criminals misusing the collected data.