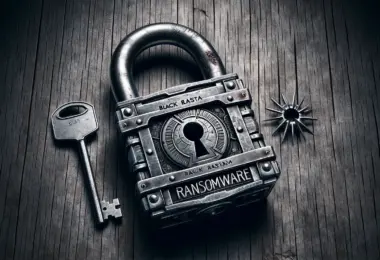
Ransomware is losing effectiveness, and victims increasingly refuse to pay the ransom. Specialists have been observing this trend since the middle of 2021, and some factors...
News
A new critical vulnerability in Jenkins has surfaced. The vulnerability in an open source automation server allows unauthorized attackers to perform remote code execution (RCE)...
The researchers have uncovered a new-old tactic used by cybercriminals. Frauds are distributing XMRig CoinMiner malware under the guise of cheats for popular games. As using...
In a concerning development, cybersecurity experts have detected active exploits (RCE) flaws in Atlassian Confluence. The vulnerability poses a severe threat due to the...
Recent research of SecurityDiscovery uncovers a data breach of a yet-unseen scale. An unnamed database, that primarily consists of data from other leaks, contains more than 26...
SRLabs researchers have recently released a free decryptor for the BlackBasta ransomware. They found a vulnerability in the malware’s encryption process and found the way to...
Hey there cyber-savvy readers! We’ve got some fantastic news to share – the notorious Qakbot botnet, also known as Qbot and Pinkslipbot, has been officially defeated! In an...
Hackers use multi-stage attacks to inject multiple remote-access trojans (RAT). The scheme involves Freeze.rs – open-source greyware used to circumvent protective mechanisms and...
Web applications with insecure direct object references (IDORs) are at significant risk of hacking, as the US Cybersecurity and Infrastructure Protection Agency (CISA), in...
Wiz analysts are confident that the recent theft of Microsoft’s MSA (Microsoft account consumer signing key) cryptographic key from Microsoft could have much more serious...
A critical Super Admin privilege escalation vulnerability threatens over 900,000 MikroTik routers running RouterOS. The issue is tracked as CVE-2023-30799 and allows attackers who...
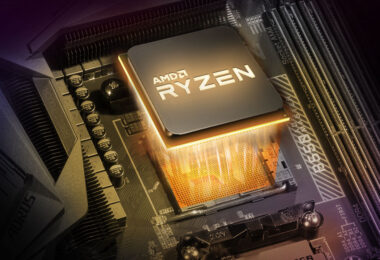
Google security expert Tavis Ormandy has identified a dangerous vulnerability affecting AMD Zen 2 processors. The problem allows stealing confidential data (including passwords...
According to Checkmarx analysts, two unnamed banks have been the victims of attacks on the open-source supply chain in recent months. Researchers say these are the first incidents...
According to Fortinet, at least three DDos botnets are exploiting the CVE-2023-28771 vulnerability recently discovered in Zyxel hardware. Experts say the attacks are taking place...